Abstract
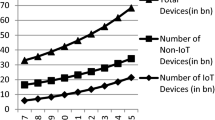
In the mobile telecommunication network, Long term Evolution (LTE) is the most successful technological development for the industrial services and applications. The Evolved Packet System based Authentication and Key Agreement (EPS-AKA) was the first protocol proposed to authenticate the communication entities in the LTE network. But, the EPS-AKA protocol suffers from the single key exposure problem and is susceptible to various security attacks. Also, the protocol incurs high bandwidth consumption and computation overhead over the communication network. Moreover, the protocol doesn’t support the Internet of Things (IoT) based applications and has several security issues such as the privacy violation of the user identity and key set identifier (KSI). To resolve the above problems, various AKA protocols were proposed by the researchers. Unfortunately, none of the protocols succeeded to overcome the privacy preservation and single key exposure problem from the communication network. In this paper, we propose the performance and security enhanced (PSE-AKA) protocol for IoT enabled LTE/LTE-A network. The proposed protocol follows the cocktail therapy to generate the authentication vectors that improves the performance in terms of computation and communication overhead. The protocol preserves the privacy of objects, protects the KSI and avoids the identified attacks from the communication network. The formal verification and security analysis of the proposed protocol is carried out using the BAN logic and AVISPA tool respectively. The security analysis shows that the protocol achieves the security goals and secure against various known attacks. Finally, the performance analysis shows that the proposed protocol generates the less overhead and reduces the bandwidth consumption from the network.








Similar content being viewed by others
References
Jover RP (2015) Security and impact of the IoT on LTE mobile networks. In: Security and Privacy in the Internet of Things (IoT): Models, Algorithms, and Implementations, vol. 6, CRC Press
Whitmore A, Agarwal A, Da Xu L (2015) The internet of things a survey of topics and trends. Inf Syst Front 17(2):261–274
Kim J, Choi SC, Yun J, Lee J (2018) Towards the oneM2M standards for building IoT ecosystem: analysis, implementation and lessons. Peer-to-Peer Netw Appl 11(1):139–151
Ghavimi F, Chen H-H (2015) M2M communications in 3GPP LTE/LTE-a networks: architectures, service requirements, challenges, and applications. IEEE Commun Surv Tutorials 17(2):525–549
Kim J, Lee J, Kim J, Yun J (2014) M2M service platforms: survey, issues, and enabling technologies. IEEE Commun Surv Tutorials 16(1):61–76
Jang Y, Kim J, Lee W (2017) Development and application of internet of things educational tool based on peer to peer network. Peer-to-Peer Netw Appl 11(6):1217–1229
Lin X, Andrews J, Ghosh A, Ratasuk R (2014) An overview of 3GPP device-to-device proximity services. IEEE Commun Mag 52(4):40–48
3rd Generation Partnership Project(3GPP) (2014) Technical specification group services and system aspects; service requirements for machine-type communication (MTC); (release 13), 3GPP TS 22.368 V13.1.0
Park RC, Jung H, Chung KY, Kim KJ (2014) Performance analysis of LTE downlink system using relay-based selective transmission. Pers Ubiquit Comput 18(3):543–551
Alam M, Yang D, Rodriguez J, Abd-alhameed R (2014) Secure device-to-device communication in LTE-a. IEEE Commun Mag 52(4):66–73
Bae WS (2016) Designing and verifying a P2P service security protocol in M2M environment. Peer-to-Peer Netw Appl 9(3):539–545
Wang G, Liu T (2018) Resource allocation for M2M-enabled cellular network using Nash bargaining game theory. Peer-to-Peer Netw Appl 11(1):110–123
Park Y, Park T (2007) A survey of security threats on 4G networks, Globecom Workshops, 2007. IEEE: 1–6
Aiash M, Mapp G, Lasebae A, Phan R (2010) Providing security in 4G systems: unveiling the challenges. In: Sixth advanced international conference on telecommunications (AICT). IEEE, pp 439–444
Bikos AN, Sklavos N (2013) LTE/SAE security issues on 4G wireless networks. IEEE Secur Priv 11(2):55–62
Abdeljebbar M, Elkouch R (2016) Security analysis of LTE/SAE networks over e-UTRAN. In: International conference on information technology for organizations development (IT4OD). IEEE, pp 1–5
Purkhiabani M, Salahi A (2012) Enhanced authentication and key agreement procedure of next generation 3GPP mobile networks. Int J Inform Electronics Eng 2(1):69
Vintilă C-E, Patriciu V-V, Bica I (2011) Security analysis of LTE access network. In: Proc. 10th Intl Conf. Networks, pp 29–34
Zhang J, Wang ZJ, Quan Z, Yin J, Chen Y, Guo M (2018) Optimizing power consumption of mobile devices for video streaming over 4G LTE networks. Peer-to-Peer Netw Appl 11(5):1101–1114
Deng Y, Fu H, Xie X, Zhou J, Zhang Y, Shi J (2009) A novel 3GPP SAE authentication and key agreement protocol. In: IEEE international conference on network infrastructure and digital content (ICNIDC 2009). IEEE, pp 557–561
Gu L, Gregory MA (2011) A green and secure authentication for the 4th generation mobile network. In: Australasian telecommunication networks and applications conference (ATNAC 2011). IEEE, pp 1–7
Hadiji F, Zarai F, Kamoun L (2009) Authentication protocol in fourth generation wireless networks. In: IFIP International Conference on Wireless and Optical Communications Networks (WOCN 2009). IEEE, pp 1–4
Hamandi K, Sarji I, Chehab A, Elhajj IH, Kayssi A (2013) Privacy enhanced and computationally efficient HSK-AKA LTE scheme. In: 27th International conference on advanced information networking and applications workshops (WAINA 2013). IEEE, pp 929–934
He D, Wang J, Zheng Y (2008) User authentication scheme based on self certified public-key for next generation wireless network. In: International symposium on biometrics and security technologies (ISBAST 2008). IEEE, pp 1–8
Køien GM (2011) Mutual entity authentication for LTE. In: 7th International wireless communications and mobile computing conference (IWCMC 2011). IEEE, pp 689–694
Li X, Wang Y (2011) Security enhanced authentication and key agreement protocol for LTE/SAE network. In: 7th International conference on wireless communications, networking and mobile computing (WiCOM 2011). IEEE, pp 1–4
Zheng Y, He D, Tang X, Wang H (2005) AKA and authorization scheme for 4G mobile networks based on trusted mobile platform. In: Fifth international conference on information, communications and signal processing. IEEE, pp 976–980
Cao J, Ma M, Li H, Zhang Y, Luo Z (2014) A survey on security aspects for LTE and LTE-a networks. IEEE Commun Surv Tutorials 16(1):283–302
Peng C, Tu G-H, Li C-Y, Lu S (2012) Can we pay for what we get in 3G data access?. In: Proceedings of the 18th annual international conference on mobile computing and networking. ACM, pp 113–124
Vintilă C-E, Patriciu V-V, Bica I (2011) A J-PAKE based solution for secure authentication in a 4G network, NEHIPISIC’11 Proceeding of 10th WSEAS international conference on electronics, hardware, wireless and optical communications
Choudhury H, Roychoudhury B, Saikia DK (2012) Enhancing user identity privacy in LTE. In: 11th International conference on trust, security and privacy in computing and communications. IEEE, pp 949–957
Prasad M, Manoharan R (2015) A robust secure DS-AKA with mutual authentication for LTE-a. Appl Math Sci 9(47):2337–2349
Hamandi K, Abdo JB, Elhajj IH, Kayssi A, Chehab A (2017) A privacy-enhanced computationally-efficient and comprehensive LTE-AKA. Comput Commun 98:20–30
Ramadan M, Li F, Xu C, Mohamed A, Abdalla H, Ali AA (2016) User-to-user mutual authentication and key agreement scheme for LTE cellular system. IJ Netw Secur 18(4):769–781
Baza MI, Fouda MM, Eldien AST, Mansour HA (2015) An efficient distributed approach for key management in microgrids. In: 11th International computer engineering conference (ICENCO-2015). IEEE, pp 19–24
Degefa FB, Lee D, Kim J, Choi Y, Won D (2016) Performance and security enhanced authentication and key agreement protocol for SAE/LTE network. Comput Netw 94:145–163
Saxena N, Grijalva S, Chaudhari NS (2016) Authentication protocol for an IoT-enabled LTE network. ACM Trans Internet Technol (TOIT) 16(4):25
Mohammadali A, Haghighi MS, Tadayon MH, Mohammadi-Nodooshan A (2018) A novel identity-based key establishment method for advanced metering infrastructure in smart grid. IEEE Trans Smart Grid 9(4):2834–2842
Sharma C, Vaid R (2019) Analysis of existing protocols in WSN based on key parameters. In: Proceedings of 2nd international conference on communication, computing and networking. Springer, Berlin, pp 165–171
Ou H-H, Hwang M-S, Jan J-K (2010) A cocktail protocol with the authentication and key agreement on the umts. J Syst Softw 83(2):316–325
Calhoun P, Loughney J, Guttman E, Zorn G, Arkko J (2003) Diameter base protocol, Technical report
Fajardo V, Arkko J, Loughney J, Zorn G (2012) Diameter base protocol, Technical report
Burrows M, Abadi M, Needham R (1989) A logic of authentication. In: Proceedings of the royal society of london a: mathematical, physical and engineering sciences, vol 426. The Royal Society, pp 233–271
Burrows M, Abadi M, Needham R (1988) Authentication: a practical study in belief and action. In: Proceedings of the 2nd conference on theoretical aspects of reasoning about knowledge. Morgan Kaufmann Publishers Inc., pp 325–342
Gaarder K, Snekkenes E (1990) On the formal analysis of pkcs authentication protocols. In: Advances in Cryptology AUSCRYPT’90. Springer, pp 105–121
Odelu V, Das AK, Goswami A (2015) A secure biometrics-based multiserver authentication protocol using smart cards. IEEE Trans Inform Forensics Secur 10(9):1953–1966
Armando A, Basin D, Boichut Y, Chevalier Y, Compagna L, Cuéllar J, Drielsma PH, Héam P-C, Kouchnarenko O, Mantovani J, et al (2005) The avispa tool for the automated validation of internet security protocols and applications. In: International conference on computer aided verification. Springer, pp 281–285
Avispa Automated Validation of Internet Security Protocols (2003) http://www.avispa-project.org
Lai C, Li H, Li X, Cao J (2015) A novel group access authentication and key agreement protocol for machine-type communication. Trans Emerging Telecommun Technol 26(3):414–431
Jiang R, Lai C, Luo J, Wang X, Wang H (2013) EAP-based group authentication and key agreement protocol for machine-type communications, Int J Distributed Sensor Netw
Lai C, Li H, Lu R, Shen XS (2013) SE-AKA: a secure and efficient group authentication and key agreement protocol for LTE networks. Comput Netw 57(17):3492–3510
Michael S Multiprecision integer and rational arithmetic c/c++ library (mir- acl). Available online at https://libraries.docs.miracl.com/miracl-user-manual/installation
Gupta M, Chaudhari NS (2019) Anonymous two factor authentication protocol for roaming service in global mobility network with security beyond traditional limit. Ad Hoc Networks 84:56–67
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendix: HLPSL code defining the role of MS, MME and HSS
Appendix: HLPSL code defining the role of MS, MME and HSS



Rights and permissions
About this article
Cite this article
Parne, B.L., Gupta, S. & Chaudhari, N.S. PSE-AKA: Performance and security enhanced authentication key agreement protocol for IoT enabled LTE/LTE-A networks. Peer-to-Peer Netw. Appl. 12, 1156–1177 (2019). https://doi.org/10.1007/s12083-019-00785-5
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12083-019-00785-5