Abstract
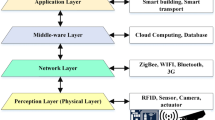
Most of the various sectors in today’s life such as bank, transport, voting, health, electricity, etc., are currently digitalized. In our research paper, we have surveyed the voting system and explored the existing drawbacks of the voting system concerning security and malfunction. The demerits in the existing schemes include less data security, vote modification, man in the middle attack, masquerade attack, denial of service attack, impersonation attack, etc. Such attacks can compromise security and allows attackers to modify the results. To resolve the above-mentioned issues as well as the attacks, this research paper proposes a protocol to overcome security-based issues. In the proposed system, a secure online e-voting system is developed for end-to-end users to avoid misappropriation on the vote during the result publication in India or any other country. The proposed E-Voting Cloud System (ECS) system has three phases: The first phase is the registration phase, the second phase is vote polling, and the third phase is result announcements. In the proposed system, the election commission of India can search and verify the vote data through cloud computing. For a detailed description of our proposed protocol, a cube data storage structure and user differentiated system are first implemented. Based on the cube data structure and user differentiated system model, the proposed protocol helps to store voter data in the cloud with the encrypted model and ECS. Finally, the candidate can decrypt the data using their key. The people can verify the result announced by the ECS. The performance analysis clearly shows that our proposed system is highly secure when compared to the existing system. Using the proposed work, secure data transfer can be performed in an efficient way for online e-voting applications.




Similar content being viewed by others
References
X. Chen, J. Li, J. Ma, Q. Tang, and W.Lou, “New algorithms for secureoutsourcingofmodularexponentiations,“IEEETransactions on Parallel and Distributed Systems, vol. 25, no. 9, pp. 2386–2396, 2014
Shen J, Shen J, Chen X, Huang X, Susilo W (2017) An efficient public auditing protocol with novel dynamic structure for cloud data. IEEE Trans Informat Forensics Secur 12(10):2402–2415
Wang B, Gu X, Ma L, Yan S (2017) Temperature error correction based on bp neural network in meteorological wireless sensor network. Int J Sensor Netw 23(4):265–278
Zhong W, Xie K, Liu Y, Yang C, Xie S (2018) Auctionmechanisms for energy trading in multi-energy systems. IEEE Trans Ind Informat 14(4):1511–1521
Kang J, Yu R, Huang X, Maharjan S, Zhang Y, Hossain E (2017) Enabling localized peer-to-peer electricity trading among plugin hybrid electric vehicles using consortium blockchains. IEEE Trans Ind Informat 13(6):3154–3164
Li J, Li X, Yang B, Sun X (2015) Segmentation-based image copymove forgery detection scheme. IEEE Trans Informat Forensics Secur 10(3):507–518
Chen X, Chen S, Wu Y (2017) Coverless information hiding method based on the chinese character encoding. J Internet Technol 18(2):313–320
Kong Y, Zhang M, Ye D (2017) A belief propagation-based method for task allocation in open and dynamic cloud environments. Knowl-Based Syst 115:123–132
Pan Z, Lei J, Zhang Y, Sun X, Kwong S (2016) Fast motion estimation based on content property for low-complexity h. 265/hevc encoder. IEEE Trans Broadcast 62(3):675–684
Ma T, Zhang Y, Cao J, Shen J, Tang M, Tian Y, Al-Dhelaan A, Al-Rodhaan M (2015) K dvem: a k-degree anonymity with vertex and edge modification algorithm. Computing 97(12):1165–1184
Thompson, Joseph KS (2016) Cognitive Radio Assisted OLSR Routing for Vehicular Sensor Networks. Procedia Comput Sci, Elsevier BV 89:271–282
Shen J, Wang C, Wang A, Sun X, Moh S, Hung PC (2017) Organizedtopologybasedroutingprotocolinincompletelypredictable ad-hoc networks. Comput Commun 99:107–118
Jian Shen, Chen Wang, Anxi Wang, Sai Ji, and Yan Zhang, “A Searchable and Verifiable Data Protection Scheme for Scholarly Big Data,” IEEE Trans Emerg Topics Comput, vol. 14, NO.8, DOI https://doi.org/10.1109/TETC.2018.2830368
Mohib Ullah, Arif Iqbal Umar, Noor ul Amin, Nizamuddin, “An Efficient and Secure Mobile Phone Voting System,” 978–1–4799-0615-4/13/$31.00 ©2013 IEEE
Xie Y, Wen H, Wu B, Jiang Y, Meng J A Modified Hierarchical Attribute-Based Encryption Access Control Method for Mobile Cloud Computing. IEEE Trans Cloud Comput. https://doi.org/10.1109/TCC.2015.2513388
Li R ChenglinShen, Heng he, ZhiyongXu, and Cheng-ZhongXu, “a lightweight secure data sharing scheme for Mobile cloud computing”, DOI https://doi.org/10.1109/TCC.2017.2649685. IEEE Trans Cloud Comput
Yang X, Yi X, Nepal S, Kelarev A, Han F A secure verifiable ranked choice online voting system based on Homomorphic encryption. IEEE Access. https://doi.org/10.1109/ACCESS.2018.2817518
Shamir A, Cryptosystems I-B, Schemes S (1984) Advances in cryptology: proceedings of CRYPTO 84. Lect Notes Comput Sci 7:47–53
Kiayias A, Zacharias T, Zhang B (2017) An Efficient E2E Verifiable E-voting System without Setup Assumptions. IEEE Secur Privacy 15:14–23
Xu L, Shen Y, Chan HC (2017) Understanding Content Voting Based on Social Foraging Theory. IEEE Trans Eng Manag 64:574–585
Kshetri N, Voas J (2018) Blockchain-Enabled E-Voting. IEEE Software 35:95–99
Gao S, Zheng D, Guo R (2019) An Anti Quantum E Voting Protocol In Block Chain With Audit Function. IEEE ACESSS 7:115304–115316
Shahzad B, Crowcroft AJ (2019) Trust Worthy Electronic Voting Used Adjusted Blockchain Technology. IEEE ACESSS 7:24477–24488
Qureshi A, Megías D, Rifà-Pous H (2019) SeVEP: Secure and Verifiable Electronic Polling System. IEEE Access 7:19266–19290
Arnob MS, Sarker N, Inzamam-UlHaque M, Bhuyan MGS (2020) Blockchain-Based Secured E-Voting System to Remove the Opacity andEnsure the Clarity of Election of Developing Countries. Int Res J Eng Technol 7(01):1826–1831
Nikhilesh Lalam M, Nithinn S, Jebakumar R (2020) BEVS - Blockchain Based E-Voting System. Int J Adv Sci Technol 29(9s):6241–6249
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
This article is part of the Topical Collection: Special Issue on Network In Box, Architecture, Networking and Applications
Guest Editor: Ching-Hsien Hsu
Rights and permissions
About this article
Cite this article
Shankar, A., Pandiaraja, P., Sumathi, K. et al. Privacy preserving E-voting cloud system based on ID based encryption. Peer-to-Peer Netw. Appl. 14, 2399–2409 (2021). https://doi.org/10.1007/s12083-020-00977-4
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12083-020-00977-4