Abstract
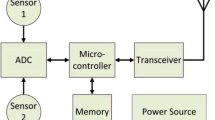
The manufacturing industry is one of the most suitable sectors that can significantly benefit from implementing the Industrial Internet of Things (IIoT) concepts and technologies. The extensive automation in the manufacturing industries leads to many heterogeneous applications based on IIoT, requiring effective integration of many heterogeneous systems and seamless operations across the machines. The problem of integration and seamless operation introduces IIoT as a separate field of study in smart manufacturing that brings many challenges, including security, traceability, trust, and reliability. In IIoT, many devices will be connected using wireless and internet infrastructure to communicate with each other. In such a scenario, the IIoT devices' trustworthiness becomes an essential factor in avoiding injection by malicious machines. Therefore, an intelligent computational model is needed to cluster and classify the IIoT devices' trustworthiness accurately. In this paper, we present a trust model based on the neutrosophic weighted product method (WPM) used by IIoT applications to assess IIoT devices' trust score. The developed model assesses devices' trustworthiness based on the spatial knowledge, temporal experience, and behavioural pattern retrieved from the IIoT devices. Furthermore, the model proposes neutrosophic K-NN clustering and neutrosophic support vector machines (SVM) for classifying the extracted characteristics. The proposed neutrosophic SVM method is able to correctly identify the trust boundaries and produces the final trust score. The simulation results show that the proposed trust model detects the misbehaviour of IIoT devices more accurately than other aggregation methods.









Similar content being viewed by others
Availability of data and material
No.
Code availability
No.
References
Abera T, Asokan N, Davi Lucas, Koushanfar F, Paverd A, Sadeghi A-R, Tsudik G (2016) Invited: things, trouble, trust: on building trust in IoT systems. In: 2016 53nd ACM/EDAC/IEEE Design Automation Conference (DAC), pp 1–6, https://doi.org/10.1145/2897937.2905020
Abuhasel KA, Khan MA (2020) A Secure Industrial Internet of Things (IIoT) framework for resource management in smart manufacturing. IEEE Access 8:117354–117364. https://doi.org/10.1109/access.2020.3004711
Akbulut Y, Sengur A, Guo Y, Smarandache F (2017) NS-k-NN: neutrosophic set-based k-nearest neighbors classifier. Symmetry 9:179
Arachchige PCM, Bertok P, Khalil I, Liu D, Camtepe S, Atiquzzaman M (2020) A trustworthy privacy preserving framework for machine learning in industrial IoT systems. IEEE Trans Ind Inform 16(9):6092–6102. https://doi.org/10.1109/TII.2020.2974555
Boltürk E, Karaşan A, Kahraman C (2019) Simple additive weighting and weighted product methods using neutrosophic sets. In: Kahraman C, Otay İ (eds) Fuzzy multi-criteria decision-making using neutrosophic. Sets studies in fuzziness and soft computing, vol 369. Springer, Cham
Boudagdigue C, Benslimane A, Kobbane A, Liu J (2020) Trust management in industrial internet of things. IEEE Trans Inform Forensics Secur 15:3667–3682. https://doi.org/10.1109/TIFS.2020.2997179
Boyes H, Bil H, Joe C, Tim W (2018) The industrial internet of things (IIoT): an analysis framework. Comput Ind 101(2018):1–12. https://doi.org/10.1016/j.compind.2018.04.015
Elhassouny A, Idbrahim S, Smarandache F (2019) Machine learning in neutrosophic environment: a survey. Neutrosophic Sets Syst 28:58–68
Fortino G, Messina F, Rosaci D, Sarné GML, Savaglio C (2020) A trust-based team formation framework for mobile intelligence in smart factories. IEEE Trans Ind Inform 16(9):6133–6142. https://doi.org/10.1109/TII.2020.2963910
Fraile F, Tagawa T, Poler R, Ortiz A (2018) Trustworthy industrial IoT gateways for interoperability platforms and ecosystems. IEEE Internet Things J 5(6):4506–4514. https://doi.org/10.1109/JIOT.2018.2832041
Guo Y, Sengur A (2015) NCM: neutrosophic c-means clustering algorithm. Pattern Recogn. https://doi.org/10.1016/j.patcog.2015.02.018
Guo J, Chen I-R, Tsai JJP (2016) A survey of trust computation models for service management in internet of things systems. Comput Commun 97:1–14. https://doi.org/10.1016/j.comcom.2016.10.012
Hasan M, Islam MdM, Zarif MII, Hashem MMA (2019) Attack and anomaly detection in IoT sensors in IoT sites using machine learning approaches. Internet of Things 7:100059. https://doi.org/10.1016/j.iot.2019.100059
Hassan MM, Gumaei A, Huda S, Almogren A (2020) Increasing the trustworthiness in the industrial IoT networks through a reliable cyberattack detection model. IEEE Trans Ind Inform 16(9):6154–6162. https://doi.org/10.1109/TII.2020.2970074
Haverkort BR, Zimmermann A (2017) Smart industry: how ICT will change the game! IEEE Internet Comput 21(1):8–10. https://doi.org/10.1109/MIC.2017.22
Jayasinghe U, Lee GM, Um T-W, Shi Q (2019) Machine learning based trust computational model for IoT services. IEEE Trans Sustain Comput 4(1):39–52. https://doi.org/10.1109/TSUSC.2018.2839623
Ju W, Cheng H (2013) A novel neutrosophic logic SVM(n-SVM) and its application to image categorization. New Math Nat Comput 9(1):27–42
Khan ZA (2018) Using energy-efficient trust management to protect IoT networks for smart cities. Sustain Cities Soc 40:1–15. https://doi.org/10.1016/j.scs.2018.03.026
Liu X, Liu Y, Liu A, Yang LT (2019) Defending ON–OFF attacks using light probing messages in smart sensors for industrial communication systems. IEEE Trans Ind Inform 14(9):3801–3811. https://doi.org/10.1109/TII.2018.2836150
Pinto S, Gomes T, Pereira J, Cabral J, Tavares A (2017) IIoTEED: an enhanced, trusted execution environment for industrial IoT edge devices. IEEE Internet Comput 21(1):40–47. https://doi.org/10.1109/MIC.2017.17
Schulz T, Leister W (2012) Ideas for a trust indicator in the internet of things. In: 2012 First International Conference on Smart Systems, Devices and Technologies, Oslo, May 2012
Wang H, Smarandache F, Sunderraman R, Zhang YQ (2005) Interval neutrosophic sets and logic: theory and applications in computing. Infinite Study https://arxiv.org/abs/cs/0505014
Wang T, Wang P, Cai S, Ma Y, Liu A, Xie M (2020) A unified trustworthy environment establishment based on edge computing in industrial IoT. IEEE Trans Ind Inform 16(9):6083–6091. https://doi.org/10.1109/TII.2019.2955152
Wurm J, Hoang K, Arias O, Sadeghi A-R, Jin Y (2016) Security analysis on consumer and industrial IoT devices. In: 2016 21st Asia and South Pacific Design Automation Conference (ASP-DAC), Jan. 2016, pp 519–524, https://doi.org/10.1109/ASPDAC.2016.7428064
Yan Z, Zhang P, Vasilios AV (2014) A survey on trust management for internet of things. J Netw Comput Appl 42:120–134. https://doi.org/10.1016/j.jnca.2014.01.014
Yan X, Xu Y, Xing X, Cui B, Guo Z, Guo T (2020) Trustworthy network anomaly detection based on an adaptive learning rate and momentum in IIoT. IEEE Trans Ind Inform 16(9):6182–6192. https://doi.org/10.1109/TII.2020.2975227
Funding
This research was funded by the Deanship of Scientific Research at Princess Nourah bint Abdulrahman University through the Fast-track Research Funding Program to support publication in the top journal (Grant No. 42-FTTJ-10).
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflicts of interest
There is no conflict of interest among authors.
Consent for publication
All authors agree to publish the paper in Journal of Ambient Intelligence and Humanized Computing.
Ethical approval
This article does not contain any studies with human participants or animals performed by any of the authors.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Khan, M.A., Alghamdi, N.S. A neutrosophic WPM-based machine learning model for device trust in industrial internet of things. J Ambient Intell Human Comput 14, 3003–3017 (2023). https://doi.org/10.1007/s12652-021-03431-2
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12652-021-03431-2