Abstract
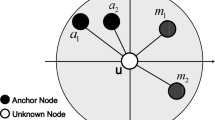
Wireless sensor nodes remain vulnerable to malicious attacks in hostile environments. Adversarial attacks capturing a few benevolent nodes and creating multiple duplicate identities make the localization process very tricky. Incorrect position estimations often lead to the wrong decision regarding the monitored event. This paper presents a secure localization scheme mitigating such attacks using fuzzy-based anchor mobility control. All nodes periodically broadcast signals over the network using omnidirectional antennas. The anchor each time forms an individual cluster using some neighboring nodes with an \({\text{Received Signal Strength}}\) (\(\mathrm{RSS}\)) exceeding a prescribed threshold. The mobility control algorithm keeps the anchor moving along a path that allows cluster formations at two successive anchor positions containing at least the nodes encountered first in the previous case. The current cluster size and the node location with minimal signal strength are two determining factors for the fuzzy controller to explore a new anchor path. The misbehaving nodes are detected and blocked by observing anomalies in node identities within the subsequent two clusters. The anchor contains an adaptive antenna and remains location-aware with a Global Positioning System (GPS) receiver. The anchor determines the \({\text{Angle of Arrival}}\) (\(\mathrm{AoA}\)) information of all the signals intercepted in each cluster using such an antenna. Then, the anchor generates and transmits beacon messages to each legitimate node. Upon receipt of two beacon messages, the nodes localize themselves autonomously and switch to power-saving mode. The simulation results corroborate its competence comparable to existing methods for localization accuracy and intrusion detection precision.






















Similar content being viewed by others
Data availability
Data is only available on request.
Code availability
Not available.
References
Alakhras M, Oussalah M, Hussein M (2020) A survey of fuzzy logic in wireless localization. J Wirel Commun Netw 89:1–45. https://doi.org/10.1186/s13638-020-01703-7
Amara SO, Beghdad R, Oussalah M (2013) Securing wireless sensor networks: a survey. EDPACS: the EDP audit, control, and security. Newsletter 47:6–29. https://doi.org/10.1080/07366981.2013.754207
Angurala M, Bala M, Bamber SS (2020) Performance analysis of modified AODV routing protocol with lifetime extension of wireless sensor networks. IEEE Access 8:10606–10613. https://doi.org/10.1109/ACCESS.2020.2965329
Anita EAM, Geetha R, Kannan E (2015) A novel hybrid key management scheme for establishing secure communication in wireless sensor networks. Wirel Pers Commun 82:1419–1433. https://doi.org/10.1007/s11277-015-2290-9
Basilico N, Gatti N, Monga M, Sicari S (2014) Security games for node localization through verifiable multilateration. IEEE Trans Dependable Secure Comput 11:72–85. https://doi.org/10.1109/TDSC.2013.30
Biswas RN, Mitra SK, Naskar MK (2014) A robust mobile anchor based localization technique for wireless sensor networks using smart antenna. Int J Ad Hoc Ubiquitous Comput 15:23–37. https://doi.org/10.1504/IJAHUC.2014.059914
Biswas RN, Mitra SK, Naskar MK (2019) Preserving security of mobile anchors against physical layer attacks: a resilient scheme for wireless node localization. In: Banday MT (ed) Cryptographic security solutions for the internet of things. IGI Global, Hershey, pp 250–282
Boukerche A, Oliveira HABF, Nakamura EF, Loureiro AAF (2008) Secure localization algorithms for wireless sensor networks. IEEE Commun Mag 46:96–101. https://doi.org/10.1109/MCOM.2008.4481347
Chakavarika TT, Gupta SK, Chaurasia BK (2017) Energy efficient key distribution and management scheme in wireless sensor networks. Wirel Pers Commun 97:1059–1070. https://doi.org/10.1007/s11277-017-4551-2
Chiang JT, Haas JJ, Choi J, Hu YC (2012) Secure location verification using simultaneous multilateration. IEEE Trans Wirel Commun 11:584–591. https://doi.org/10.1109/TWC.2011.120911.101147
Choi J, Bang J, Kim LH, Ahn M, Kwon T (2015) Location-based key management strong against insider threats in wireless sensor networks. IEEE Syst J 11:494–502. https://doi.org/10.1109/JSYST.2015.2422736
Civicioglu P (2012) Transforming geocentric cartesian coordinates to geodetic coordinates by using differential search algorithm. Comput Geosci 46:229–247. https://doi.org/10.1016/j.cageo.2011.12.011
Compagno A, Conti M, D’Amico AA, Dini G, Perazzo P, Taponecco L (2016) Modeling enlargement attacks against UWB distance bounding protocols. IEEE Trans Inf Forensics Secur 11:1565–1577. https://doi.org/10.1109/TIFS.2016.2541613
Conti M, Pietro RD, Mancini LV, Mei A (2011) Distributed detection of clone attacks in wireless sensor networks. IEEE Trans Dependable Secure Comput 8:685–698. https://doi.org/10.1109/TDSC.2010.25
Das SK, Ho JW (2011) A synopsis on node compromise detection in wireless sensor networks using sequential analysis (Invited Review Article). Comput Commun 34:2003–2012. https://doi.org/10.1016/j.comcom.2011.07.004
Delaët S, Mandal PS, Rokicki MA, Tixeuil S (2011) Deterministic secure positioning in wireless sensor networks. Theor Comput Sci 412:4471–4481. https://doi.org/10.1016/j.tcs.2011.04.010
Esposito C, Choi C (2017) Signaling game based strategy for secure positioning in wireless sensor networks. Pervasive Mob Comput 40:611–627. https://doi.org/10.1016/j.pmcj.2017.06.025
Garcia-Alfaro J, Barbeau M, Kranakis E (2011) Secure geolocalization of wireless sensor nodes in the presence of misbehaving anchor nodes. Ann Telecommun 66:535–552. https://doi.org/10.1007/s12243-010-0221-z
Garg R, Varna AL, Wu M (2012) An efficient gradient descent approach to secure localization in resource constrained wireless sensor networks. IEEE Trans Inf Forensics Secur 7:717–730. https://doi.org/10.1109/TIFS.2012.2184094
Giri A, Dutta S, Neogy S (2020) Information-theoretic approach for secure localization against Sybil attack in wireless sensor network. J Ambient Intell Human Comput. https://doi.org/10.1007/s12652-020-02690-9
Gross FB (2005) Smart antennas for wireless communications. McGraw-Hill Companies Inc., New York
Gu Q, Tang T, Ma F (2016) Energy-efficient train tracking operation based on multiple optimization models. IEEE Trans Intell Transp Syst 17:882–892. https://doi.org/10.1109/TITS.2015.2502609
Han G, Jiang J, Shu L, Guizani M, Nishio S (2013) A two-step secure localization for wireless sensor networks. Comput J 56:1154–1166. https://doi.org/10.1093/comjnl/bxr138
Ho JW, Wright M, Das SK (2012a) Distributed detection of mobile malicious node attacks in wireless sensor networks. Ad Hoc Netw 10:512–523. https://doi.org/10.1016/j.adhoc.2011.09.006
Ho JW, Wright M, Das SK (2012b) Zone trust: fast zone-based node compromise detection and revocation in wireless sensor networks using sequential hypothesis testing. IEEE Trans Dependable Secure Comput 9:494–516. https://doi.org/10.1109/TDSC.2011.65
Huang M, Yu B (2018) SDN-based secure localization in heterogeneous WSN. In: Qing S, Mitchell C, Chen L, Liu D (eds) Information and communications security. Springer, Cham, pp 276–287
Jadliwala M, Zhong S, Upadhyaya SJ, Qiao C, Hubaux JP (2010) Secure distance-based localization in the presence of cheating beacon nodes. IEEE Trans Mob Comput 9:810–823. https://doi.org/10.1109/TMC.2010.20
Jiang J, Han G, Zhu C, Dong Y, Zhang N (2011) Secure localization in wireless sensor networks: a survey (invited paper). J Commun 6:460–470. https://doi.org/10.4304/jcm.6.6.460-470
Jokhio SH, Jokhio IA, Kemp AH (2012) Node capture attack detection and defence in wireless sensor networks. IET Wirel Sens Syst 2:161–169. https://doi.org/10.1049/iet-wss.2011.0064
Kumar G, Rai MK, Kim H, Saha R (2017) A secure localization approach using mutual authentication and insider node validation in wireless sensor networks. Mob Inf Syst 2017:1–12. https://doi.org/10.1155/2017/3243570
Li L, Xu G, Jiao L, Li X, Wang H, Hu J, Xian H, Lian W, Gao H (2019) A secure random key distribution scheme against node replication attacks in industrial wireless sensor systems. IEEE Trans Ind Inform 16:2091–2101. https://doi.org/10.1109/TII.2019.2927296
Liberti JC, Rappaport TS (1999) Smart antennas for wireless communications: IS-95 and third generation CDMA applications. Prentice Hall, New Jersey
Liu X, Su S, Han F, Liu Y, Pan Z (2018) A range-based secure localization algorithm for wireless sensor networks. IEEE Sens J 19:785–796. https://doi.org/10.1109/JSEN.2018.2877306
Liu C, Yao X, Luo J (2019) Multiregional secure localization using compressive sensing in wireless sensor networks. ETRI J 41:739–749. https://doi.org/10.4218/etrij.2017-0116
Mendel JM (1995) Fuzzy logic systems for engineering: a tutorial. Proc IEEE Inst Electr Electron Eng 83:345–377. https://doi.org/10.1109/5.364485
Mi Q, Stankovic JA, Stoleru R (2012) Practical and secure localization and key distribution for wireless sensor networks. Ad Hoc Netw 10:946–961. https://doi.org/10.1016/j.adhoc.2011.12.008
Nguyen TN, Le VV, Chu SI, Liu BH, Hsu YC (2021) Secure localization algorithms against localization attacks in wireless sensor networks. Wirel Pers Commun. https://doi.org/10.1007/s11277-021-08404-4
Perazzo P, Taponecco L, D’Amico AA, Dini G (2016) Secure positioning in wireless sensor networks through enlargement miscontrol detection. ACM Trans Sens Netw 12:1–32. https://doi.org/10.1145/2943782
Pietro RD, Guarino S, Verde NV, Domingo-Ferrer J (2014) Security in wireless ad-hoc networks—a survey. Comput Commun 51:1–20. https://doi.org/10.1016/j.comcom.2014.06.003
Sarigiannidis P, Karapistoli E, Economides AA (2015) Detecting Sybil attacks in wireless sensor networks using UWB ranging-based information. Expert Syst Appl 42:7560–7572. https://doi.org/10.1016/j.eswa.2015.05.057
Ssu KF, Wang WT, Chang WC (2009) Detecting Sybil attacks in wireless sensor networks using neighboring information. Comput Netw 53:3042–3056. https://doi.org/10.1016/j.comnet.2009.07.013
Sun X, Wu X, Huang C, Xu Z, Zhong J (2016) Modified access polynomial based self-healing key management schemes with broadcast authentication and enhanced collusion resistance in wireless sensor networks. Ad Hoc Netw 37:324–336. https://doi.org/10.1016/j.adhoc.2015.08.027
Wang H, Wen Y, Lu Y, Zhao D, Ji C (2019) Secure localization algorithms in wireless sensor networks: a review. In: Bhatia S, Tiwari S, Mishra K, Trivedi M (eds) Advances in computer communication and computational sciences. Springer, Singapore, pp 543–553
Wei Y, Guan Y (2013) Lightweight location verification algorithms for wireless sensor networks. IEEE Trans Parallel Distrib Syst 24:938–950. https://doi.org/10.1109/TPDS.2012.42
Wu X, Cho J, d’Auriol BJ, Lee S (2007) Mobility-assisted relocation for self-deployment in wireless sensor networks. IEICE Trans Commun E90-B:2056–2069. https://doi.org/10.1093/ietcom/e90-b.8.2056
Xue W, Peng B, Wang S, Hua Y (2020) A type of energy-efficient secure localization algorithm FM based in dynamic sensor networks. J Wirel Commun Netw 39:1–7. https://doi.org/10.1186/s13638-020-1658-z
Zeng Y, Cao J, Hong J, Zhang S, Xie L (2013) Secure localization and location verification in wireless sensor networks: a survey. J Supercomput 64:685–701. https://doi.org/10.1007/s11227-010-0501-4
Zhang Z, Wu F, Jiang C, Deng J (2015) An efficient detection scheme of node replication attacks for wireless sensor networks. Int J Secur Netw 10:228–238. https://doi.org/10.1504/IJSN.2015.072440
Zhu B, Setia S, Jajodia S, Roy S, Wang L (2010) Localized multicast: efficient and distributed replica detection in large-scale sensor networks. IEEE Trans Mob Comput 9:913–926. https://doi.org/10.1109/TMC.2010.40
Zhu WT, Xiang Y, Zhou J, Deng RH, Bao F (2011) Secure localization with attack detection in wireless sensor networks. Int J Inf Secur 10:155–171. https://doi.org/10.1007/s10207-011-0127-4
Acknowledgements
The authors would like to express their gratitude to the esteemed editors and all anonymous reviewers for their valuable suggestions and comments to improve the quality of this paper.
Funding
This research work is not funded by any agency.
Author information
Authors and Affiliations
Contributions
All authors have an equal contribution to this research work.
Corresponding author
Ethics declarations
Conflict of interest
The authors have no potential conflicts of interest.
Compliance with ethical standards
This research work retains all ethical publication policies.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Biswas, R.N., Mitra, S.K. & Naskar, M.K. Localization under node capture attacks using fuzzy based anchor mobility control. J Ambient Intell Human Comput 14, 8583–8612 (2023). https://doi.org/10.1007/s12652-021-03619-6
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12652-021-03619-6