Abstract
In recent years, advanced threat and zero day attacks are increasing significantly, but the traditional network intrusion detection system based on feature filtering or based on a well known signature has some drawbacks. Accordingly, there is a need for security solutions that are suitable for IoT environment. A network intrusion detection system (NIDS) is a solution that examines network traffic and alerts system administrators if there are security breaches. In this paper, a fusion-based anomaly detection using modified isolation forest for Internet of Things (IoT) is proposed. The proposed NIDS has been evaluated using three benchmark datasets(UNSW-NB15, NLS-KDD and \(KDDCUP^{99}\)) in terms of F-score, accuracy and detection rate. Results show that the suggested approach reduces the run time by 28.80% for UNSW-NB15 in the training model and achieves 97.2%, 97.4% accuracy and detection rate respectively. Moreover, M-iForest outperforms other NIDS techniques that are selected from state-of-the-art relevant research found in the literature.








Similar content being viewed by others
Data Availability Statement
The \(KDDCUP^{99}\) data that support the findings of this study are available in UCI repository [https://archive.ics.uci.edu/ml/datasets/kdd+cup+1999+data], while the NSL-KDD dataset are available from Canadian Institute for Cybersecurity [https://www.unb.ca/cic/datasets/nsl.html], and finally the UNSW-NB15 dataset are available in Kaggle repository [https://www.kaggle.com/datasets/mrwellsdavid/unsw-nb15].
References
AbuAlghanam O, Albdour L, Adwan O (2021) Multimodal biometric fusion online handwritten signature verification using neural network and support vector machine. Transactions 7:8
Abualghanam O, Qatawneh M, Almobaideen W (2019) A survey of key distribution in the context of internet of things. J Theor Appl Inf Technol 97:3217–3241
AbuAlghanam O, Qatawneh M, Almobaideen W, Saadeh M (2022) A new hierarchical architecture and protocol for key distribution in the context of iot-based smart cities. J Inf Secur Appl 67:103173
Acharya N, Singh S (2018) An iwd-based feature selection method for intrusion detection system. Soft Comput 22:4407–4416
Ahmad T, Aziz MN (2019) Data preprocessing and feature selection for machine learning intrusion detection systems. ICIC Express Lett 13:93–101
Aksu D, Üstebay S, Aydin MA, Atmaca T (2018) Intrusion detection with comparative analysis of supervised learning techniques and fisher score feature selection algorithm. In: International symposium on computer and information sciences (pp. 141–149). Springer, New York
Al-Safi AHS, Hani ZIR, Zahra MMA (2021) Using a hybrid algorithm and feature selection for network anomaly intrusion detection. J Mech Eng Res Dev 44:253–262
Alamiedy TA, Anbar M, Alqattan ZN, Alzubi QM (2020) Anomaly-based intrusion detection system using multi-objective grey wolf optimisation algorithm. J Ambient Intell Hum Comput 11:3735–3756
Alazzam H, Alsmady A, Shorman AA (2019) Supervised detection of iot botnet attacks. In: Proceedings of the second international conference on data science, E-Learning and information systems, pp 1–6
Alazzam H, Sharieh A, Sabri KE (2020) A feature selection algorithm for intrusion detection system based on pigeon inspired optimizer. Expert Syst Appl 148:113249
Alazzam H, Sharieh A, Sabri KE (2021) A lightweight intelligent network intrusion detection system using ocsvm and pigeon inspired optimizer. Appl Intell, pp 1–18
Alghanam OA, Al-Khatib SN, Hiari MO (2022) Data mining model for predicting customer purchase behavior in e-commerce context. Int J Adv Comput Sci Appl 13
Alhajjar E, Maxwell P, Bastian N (2021) Adversarial machine learning in network intrusion detection systems. Exp Syst Appl p 115782
Asassfeh M, Obeid N, Almobaideen W (2020) Anonymous authentication protocols for iot based-healthcare systems: a survey. Int J Commun Netw Inf Secur 12:302–315
Bergman L, Hoshen Y (2020) Classification-based anomaly detection for general data. arXiv:2005.02359
Carletti M, Terzi M, Susto GA (2020) Interpretable anomaly detection with diffi: Depth-based isolation forest feature importance. arXiv:2007.11117
Chandola V, Banerjee A, Kumar V (2009) Anomaly detection: a survey. ACM Comput Surv 41:1–58
Cheng Z, Zou C, Dong J (2019) Outlier detection using isolation forest and local outlier factor. In: Proceedings of the conference on research in adaptive and convergent systems, pp 161–168
da Costa NL, de Lima MD, Barbosa R (2021) Evaluation of feature selection methods based on artificial neural network weights. Expert Syst Appl 168:114312
Dwivedi S, Vardhan M, Tripathi S (2021) Building an efficient intrusion detection system using grasshopper optimization algorithm for anomaly detection. Clust Comput 24:1881–1900
Farahnakian F, Heikkonen J (2018) Anomaly-based intrusion detection using deep neural networks. Int J Digit Content Technol Appl 12:70–118
Gopalan S, Raza A, AlmobaideenSun W (2021) Iot security in healthcare using ai: a survey. In: 2020 International Conference on Communications, Signal Processing, and their Applications (ICCSPA), pp 1–6
Gupta AR, Agrawal J (2021) The multi-demeanor fusion based robust intrusion detection system for anomaly and misuse detection in computer networks. J Ambient Intell Hum Comput 12:303–319
Halim Z, Yousaf MN, Waqas M, Sulaiman M, Abbas G, Hussain M, Ahmad I, Hanif M (2021) An effective genetic algorithm-based feature selection method for intrusion detection systems. Comput Secur 110:102448
Haneef F, Singh S (2017) A feature selection technique for intrusion detection system based on iwd and aco. Int J Adv Res Comput Sci 8
Hariri S, Kind MC, Brunner RJ (2019) Extended isolation forest. IEEE Trans Knowl Data Eng 33:1479–1489
Hariyale N, Rathore MS, Prasad R, Saurabh P (2020) A hybrid approach for intrusion detection system. In: Soft computing for problem solving, pp 391–403, Springer, New York
Huang C, Wen J, Xu Y, Jiang Q, Yang J, Wang Y, Zhang D (2022) Self-supervised attentive generative adversarial networks for video anomaly detection. IEEE Trans Neural Netw Learn Syst
Huang C, Wu Z, Wen J, Xu Y, Jiang Q, Wang Y (2021) Abnormal event detection using deep contrastive learning for intelligent video surveillance system. IEEE Trans Industr Inf 18:5171–5179
Huang C, Yang Z, Wen J, Xu Y, Jiang Q, Yang J, Wang Y (2021b) Self-supervision-augmented deep autoencoder for unsupervised visual anomaly detection. IEEE Trans Cybern
Kamarudin MH, Maple C, Watson T (2019) Hybrid feature selection technique for intrusion detection system. Int J High Perform Comput Netw 13:232–240
Kaplan MO, Alptekin SE (2020) An improved bigan based approach for anomaly detection. Procedia Comput Sci 176:185–194
Khan IA, Pi D, Khan N, Khan ZU, Hussain Y, Nawaz A, Ali F (2021) A privacy-conserving framework based intrusion detection method for detecting and recognizing malicious behaviours in cyber-physical power networks. Appl Intell 51:7306–7321
Kumar P, Gupta GP, Tripathi R (2021) A distributed ensemble design based intrusion detection system using fog computing to protect the internet of things networks. J Ambient Intell Hum Comput 12:9555–9572
Liu FT, Ting KM, Zhou Z-H (2008) Isolation forest. In: 2008 8th IEEE international conference on data mining, pp 413–422
Manimurugan S (2021) Iot-fog-cloud model for anomaly detection using improved naïve bayes and principal component analysis. In: Journal of Ambient Intelligence and Humanized Computing, pp 1–10
Mbanaso UM, Dandaura E (2015) The cyberspace: Redefining a new world. IOSR J Comput Eng (IOSR-JCE) 17:17–24
Meira J, Andrade R, Praça I, Carneiro J, Bolón-Canedo V, Alonso-Betanzos A, Marreiros G (2020) Performance evaluation of unsupervised techniques in cyber-attack anomaly detection. J Ambient Intell Hum Comput 11:4477–4489
Mishra S, Sagban R, Yakoob A, Gandhi N (2021) Swarm intelligence in anomaly detection systems: an overview. Int J Comput Appl 43:109–118
Mohammad RMA, Alsmadi MK (2021) Intrusion detection using highest wins feature selection algorithm. Neural Comput Appl 33:9805–9816
Mohammadi S, Mirvaziri H, Ghazizadeh-Ahsaee M, Karimipour H (2019) Cyber intrusion detection by combined feature selection algorithm. J Inf Secur Appl 44:80–88
Mojtahedi A, Sorouri F, Souha AN, Molazadeh A, Mehr SS (2022) Feature selection-based intrusion detection system using genetic whale optimization algorithm and sample-based classification. arXiv:2201.00584
Moustafa N, Slay J (2015) Unsw-nb15: a comprehensive data set for network intrusion detection systems (unsw-nb15 network data set). In: 2015 military communications and information systems conference (MilCIS), pp 1–6, IEEE
Nimbalkar P, Kshirsagar D (2021) Feature selection for intrusion detection system in internet-of-things (iot). ICT Express 7:177–181
Otair M, Ibrahim OT, Abualigah L, Altalhi M, Sumari P (2022) An enhanced grey wolf optimizer based particle swarm optimizer for intrusion detection system in wireless sensor networks. Wireless Netw 28:721–744
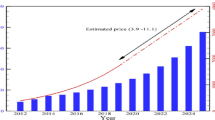
O’Dea S (2020) Forecast number of iot connected objects worldwide from 2018 to 2025, by type. https://www.statista.com/statistics/976079/number-of-iot-connected-objects-worldwide-by-type/
Qatawneh M, Almobaideen W, AbuAlghanam O (2020) Challenges of blockchain technology in context internet of things: a survey. Int J Comput Appl 175:13–20
Rajasegarar S, Leckie C, Palaniswami M (2008) Cesvm: centered hyperellipsoidal support vector machine based anomaly detection. In: 2008 IEEE International Conference on Communications, pp 1610–1614. IEEE
Reddy DK, Behera HS, Nayak J, Vijayakumar P, Naik B, Singh PK (2021) Deep neural network based anomaly detection in internet of things network traffic tracking for the applications of future smart cities. Trans Emerg Telecommun Technol 32:e4121
Revathi S, Malathi A (2013) A detailed analysis on nsl-kdd dataset using various machine learning techniques for intrusion detection. IJERT 2:1848–1853
Sanjaya SKSSS, Jena K (2014) A detail analysis on intrusion detection datasets. In: 2014 IEEE international advance computing conference (IACC)
Sohn I (2020) Deep belief network based intrusion detection techniques: a survey. Exp Syst Appl, pp 114170
Tavallaee M, Bagheri E, Lu W, Ghorbani AA (2009) A detailed analysis of the kdd cup 99 data set. In: 2009 IEEE symposium on computational intelligence for security and defense applications (pp 1–6), IEEE
Xu W, Jang-Jaccard J, Singh A, Wei Y, Sabrina F (2021) Improving performance of autoencoder-based network anomaly detection on nsl-kdd dataset. IEEE Access 9:140136–140146
Yang J, Li A, Xiao S, Lu W, Gao X (2021) Mtd-net: learning to detect deepfakes images by multi-scale texture difference. IEEE Trans Inf Forensics Secur 16:4234–4245
Yang J, Xiao S, Li A, Lan G, Wang H (2021) Detecting fake images by identifying potential texture difference. Fut Gen Comput Syst 125:127–135
Yang J, Xiao S, Li A, Lu W, Gao X, Li Y (2021c) Msta-net: forgery detection by generating manipulation trace based on multi-scale self-texture attention. In: IEEE transactions on circuits and systems for video technology,
Zhou Y, Cheng G, Jiang S, Dai M (2020) Building an efficient intrusion detection system based on feature selection and ensemble classifier. Comput Netw 174:107247
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
AbuAlghanam, O., Alazzam, H., Alhenawi, E. et al. Fusion-based anomaly detection system using modified isolation forest for internet of things. J Ambient Intell Human Comput 14, 131–145 (2023). https://doi.org/10.1007/s12652-022-04393-9
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12652-022-04393-9
Keywords
- Cybersecurity
- Intrusion detection system
- Isolation forest
- Network intrusion
- \(KDDCUP^{99}\)
- UNSW-NB15
- NSL-KDD