Abstract
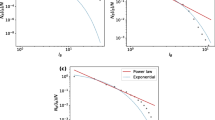
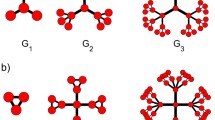
Complex networks have been widely applied in many complex systems existed in nature and society because of its rapid development. Many methods have been proposed to evaluate the vulnerability of the complex networks because of the high security requirements of the network. In this paper, a novel method is proposed to evaluate network’s vulnerability, which is based on fuzzy fractal dimension and average edge betweenness. Fuzzy fractal dimension can reflect the dynamic structure and topological structure of complex network, which is important to the vulnerability of complex network. So this proposed method can overcome the shortcomings of previous works by replacing the key coefficient p by fuzzy fractal dimension. In order to show this proposed method’s accuracy and effectiveness, six USAir networks in different years are applied in this paper. Three common methods are used to compare the results with this proposed method, and the RB attack strategy is used to analyze the vulnerability of dynamic characteristic. The fuzzy fractal dimension of randomly selecting largest connected subset which is close to the initial fuzzy fractal dimension shows the reliability and stability of this proposed method. The vulnerability order obtained by this proposed method is more realistic, because the Pearson correlation coefficient r about this method equals to 0.9805, which shows a extremely strong correlation with the reality.





Similar content being viewed by others
References
Albert, R., Albert, I., Nakarado, G.L.: Structural vulnerability of the north american power grid. Phys. Rev. E 69(2) (2004). https://doi.org/10.1103/PhysRevE.69.025103
Albert, R., Barabasi, A.L.: Statistical mechanics of complex networks. Rev. Mod. Phys. 74(1), 47–97 (2002). https://doi.org/10.1103/RevModPhys.74.47
Ayhan, M.B., Aydin, M.E., Oztemel, E.: A multi-agent based approach for change management in manufacturing enterprises. J. Intell. Manuf. 26(5), 975–988 (2015). https://doi.org/10.1007/s10845-013-0794-2
Bian, T., Zheng, H., Yin, L., Deng, Y.: Failure mode and effects analysis based on Dnumbers and topsis. Qual. Reliab. Eng. Int. Article ID: QRE2268 (2018). https://doi.org/10.1002/qre.2268
Boccaletti, S., Buldu, J., Criado, R., Flores, J., Latora, V., Pello, J., Romance, M.: Multiscale vulnerability of complex networks. Chaos 17(4) (2007). https://doi.org/10.1063/1.2801687
Bureau of transportation statistics. http://www.transtats.bts.gov/DL_SelectFields.asp?Table_ID=292
Carmona, C.J., Chrysostomou, C., Seker, H., del Jesus, M.J.: Fuzzy rules for describing subgroups from influenza a virus using a multi-objective evolutionary algorithm. Appl. Soft Comput. 13(8), 3439–3448 (2013). https://doi.org/10.1016/j.asoc.2013.04.011
Castillo, O., Lizarraga, E., Soria, J., Melin, P., Valdez, F.: New approach using ant colony optimization with ant set partition for fuzzy control design applied to the ball and beam system. Inf. Sci. 294, 203–215 (2015). https://doi.org/10.1016/j.ins.2014.09.040
Castillo, O., Melin, P.: Automated mathematical modelling, simulation and behavior identification of robotic dynamic systems using a new fuzzy-fractal-genetic approach. Robot. Auton. Syst. 28(1), 19–30 (1999). https://doi.org/10.1016/s0921-8890(99)00026-3
Castillo, O., Melin, P.: Hybrid intelligent systems for time series prediction using neural networks, fuzzy logic, and fractal theory. IEEE Trans. Neural Netw. 13(6), 1395–1408 (2002). https://doi.org/10.1109/tnn.2002.804316
Castillo, O., Melin, P.: Optimization of type-2 fuzzy systems based on bio-inspired methods: a concise review. Inf. Sci. 205, 1–19 (2012). https://doi.org/10.1016/j.ins.2012.04.003
Castillo, O., Melin, P., Pedrycz, W.: Design of interval type-2 fuzzy models through optimal granularity allocation. Appl. Soft Comput. 11(8), 5590–5601 (2011). https://doi.org/10.1016/j.asoc.2011.04.005
Castillo, O., Neyoy, H., Soria, J., Melin, P., Valdez, F.: A new approach for dynamic fuzzy logic parameter tuning in ant colony optimization and its application in fuzzy control of a mobile robot. Appl. Soft Comput. 28, 150–159 (2015). https://doi.org/10.1016/j.asoc.2014.12.002
Chan, K.Y., Engelke, U.: Varying spread fuzzy regression for affective quality estimation. IEEE Trans. Fuzzy Syst. 25(3), 594–613 (2017). https://doi.org/10.1109/tfuzz.2016.2566812
Chan, K.Y., Lam, H.K., Dillon, T.S., Ling, S.H.: A stepwise-based fuzzy regression procedure for developing customer preference models in new product development. IEEE Trans. Fuzzy Syst. 23(5), 1728–1745 (2015). https://doi.org/10.1109/tfuzz.2014.2375911
Chen, C.H., Lan, G.C., Hong, T.P., Lin, S.B.: Mining fuzzy temporal association rules by item lifespans. Appl. Soft Comput. 41, 265–274 (2016). https://doi.org/10.1016/j.asoc.2015.01.008
Chou, C.C.: A generalized similarity measure for fuzzy numbers. J. Intell. Fuzzy Syst. 30(2), 1147–1155 (2016)
Clough, J.R., Evans, T.S.: What is the dimension of citation space? Phys. Stat. Mech. Appl. 448, 235–247 (2016). https://doi.org/10.1016/j.physa.2015.12.053
Crisan, G.C., Pintea, C.M., Palade, V.: Emergency management using geographic information systems: application to the first romanian traveling salesman problem instance. Knowl. Inf. Syst. 50(1), 265–285 (2017). https://doi.org/10.1007/s10115-016-0938-8
Crucitti, P., Latora, V., Marchiori, M.: Model for cascading failures in complex networks. Phys. Rev. E 69(4) (2004). https://doi.org/10.1103/PhysRevE.69.045104
Deng, X., Deng, Y.: D-AHP method with different credibility of information. Soft Comput. pp. Published online, https://doi.org/10.1007/s00500-017-2993-9(2018)
Deng, X., Han, D., Dezert, J., Deng, Y., Shyr, Y.: Evidence combination from an evolutionary game theory perspective. IEEE Trans. Cybern. 46(9), 2070–2082 (2016)
Deng, X., Jiang, W.: An evidential axiomatic design approach for decision making using the evaluation of belief structure satisfaction to uncertain target values. Int. J. Intell. Syst. 33(1), 15–32 (2018). https://doi.org/10.1002/int.21929
Du, W.J., Zhang, J.G., An, X.L., Qin, S., Yu, J.N.: Outer synchronization between two coupled complex networks and its application in public traffic supernetwork. Discrete Dyn. Nat. Soc. p. 8 (2016). https://doi.org/10.1155/2016/8920764
Du, W.J., Zhang, J.G., Li, Y.Z., Qin, S.: Synchronization between different networks with time-varying delay and its application in bilayer coupled public traffic network. Math. Probl. Eng. p. 11 (2016). https://doi.org/10.1155/2016/6498316
Ekong, U., Lam, H.K., Xiao, B., Ouyang, G.X., Liu, H.B., Chan, K.Y., Ling, S.H.: Classification of epilepsy seizure phase using interval type-2 fuzzy support vector machines. Neurocomputing 199, 66–76 (2016). https://doi.org/10.1016/j.neucom.2016.03.033
Gallos, L.K., Fefferman, N.H.: The effect of disease-induced mortality on structural network properties. Plos One 10(8), 17 (2015). https://doi.org/10.1371/journal.pone.0136704
Gallos, L.K., Fefferman, N.H.: Simple and efficient self-healing strategy for damaged complex networks. Phys. Rev. E 92(5) (2015). https://doi.org/10.1103/PhysRevE.92.052806
Gallos, L.K., Makse, H.A., Sigman, M.: A small world of weak ties provides optimal global integration of self-similar modules in functional brain networks. Proc. Natl. Acad. Sci. U. S. A. 109(8), 2825–2830 (2012). https://doi.org/10.1073/pnas.1106612109
Gallos, L.K., Potiguar, F.Q., Andrade, J.S., Makse, H.A.: Imdb network revisited: Unveiling fractal and modular properties from a typical small-world network. Plos One 8(6), 8 (2013). https://doi.org/10.1371/journal.pone.0066443
Gao, J.X., Barzel, B., Barabasi, A.L.: Universal resilience patterns in complex networks. Nature 530(7590), 307–312 (2016). https://doi.org/10.1038/nature16948
Gou, L., Wei, B., Sadiq, R., Sadiq, Y., Deng, Y.: Topological vulnerability evaluation model based on fractal dimension of complex networks. Plos One 11(1) (2016). https://doi.org/10.1371/journal.pone.0146896
Hahn, K., Massopust, P.R., Prigarin, S.: A new method to measure complexity in binary or weighted networks and applications to functional connectivity in the human brain. Bmc Bioinform. 17, 18 (2016). https://doi.org/10.1186/s12859-016-0933-9
Hausdorff, F.: Dimension and outer dimension. Mathematische Annalen 79, 157–179 (1919)
Holme, P., Kim, B.J., Yoon, C.N., Han, S.K.: Attack vulnerability of complex networks. Phys. Rev. E 65(5) (2002). https://doi.org/10.1103/PhysRevE.65.056109
Holmgren, A.J.: Using graph models to analyze the vulnerability of electric power networks. Risk Anal. 26(4), 955–969 (2006). https://doi.org/10.1111/j.1539-6924.2006.00791.x
Hong, T.P., Lee, Y.C., Wu, M.T.: An effective parallel approach for genetic-fuzzy data mining. Expert Syst. Appl. 41(2), 655–662 (2014). https://doi.org/10.1016/j.eswa.2013.07.090
Huang, D.W., Yu, Z.G.: Dynamic-sensitive centrality of nodes in temporal networks. Sci. Rep. 7, 11 (2017). https://doi.org/10.1038/srep41454
Jiang, W., Wang, S.: An uncertainty measure for interval-valued evidences. Int. J. Comput. Commun. Control 12(5), 631–644 (2017)
Jiang, W., Wei, B., Liu, X., Li, X., Zheng, H.: Intuitionistic fuzzy evidential power aggregation operator and its application in multiple criteria decision-making. Int. J. Syst. Sci. Published on line. https://doi.org/10.1002/int.21939(2018)
Jiang, W., Wei, B., Liu, X., Li, X., Zheng, H.: Intuitionistic fuzzy power aggregation operator based on entropy and its application in decision making. Int. J. Intell. Syst. 33(1), 49–67 (2018). https://doi.org/10.1002/int.21939
Kang, B., Chhipi-Shrestha, G., Deng, Y., Hewage, K., Sadiq, R.: Stable strategies analysis based on the utility of z-number in the evolutionary games. Appl. Mathe. Comput. (2017). https://doi.org/10.1016/j.amc.2017.12.006
Lan, G.C., Hong, T.P., Lin, Y.H., Wang, S.L.: Fuzzy utility mining with upper-bound measure. Appl. Soft Comput. 30, 767–777 (2015). https://doi.org/10.1016/j.asoc.2015.01.055
Liu, T., Deng, Y., Chan, F.: Evidential supplier selection based on DEMATEL and game theory. Int. J. Fuzzy Syst. https://doi.org/10.1007/s40815-017-0400-4(2017)
Melin, P., Castillo, O.: An intelligent hybrid approach for industrial quality control combining neural networks, fuzzy logic and fractal theory. Inf. Sci. 177(7), 1543–1557 (2007). https://doi.org/10.1016/j.ins.2006.07.022
Mishkovski, I., Biey, M., Kocarev, L.: Vulnerability of complex networks. Commun. Nonlinear Sci. Numer. Simul. 16(1), 341–349 (2011). https://doi.org/10.1016/j.cnsns.2010.03.018
Morone, F., Makse, H.A.: Influence maximization in complex networks through optimal percolation. Nature 524(7563), 65–U122 (2015). https://doi.org/10.1038/nature14604
Newman, M.E.J.: The structure and function of complex networks. Siam Rev. 45(2), 167–256 (2003). https://doi.org/10.1137/s003614450342480
Paun, V.A., Paun, V.P.: Fracture surface evaluation of zircaloy-4. Mater. Plast. 53(2), 326–331 (2016)
Pedrycz, W.: From fuzzy data analysis and fuzzy regression to granular fuzzy data analysis. Fuzzy Sets Syst. 274, 12–17 (2015). https://doi.org/10.1016/j.fss.2014.04.017
Pedrycz, W.: From fuzzy models to granular fuzzy models. Int. J. Comput. Intell. Syst. 9, 35–42 (2016). https://doi.org/10.1080/18756891.2016.1180818
Pedrycz, W., Bargiela, A.: Fuzzy fractal dimensions and fuzzy modeling. Inf. Sci. 153, 199–216 (2003). https://doi.org/10.1016/s0020-0255(03)00075-6
Pedrycz, W., Jastrzebska, A., Homenda, W.: Design of fuzzy cognitive maps for modeling time series. IEEE Trans. Fuzzy Syst. 24(1), 120–130 (2016). https://doi.org/10.1109/tfuzz.2015.2428717
Schich, M., Song, C.M., Ahn, Y.Y., Mirsky, A., Martino, M., Barabasi, A.L., Helbing, D.: A network framework of cultural history. Science 345(6196), 558–562 (2014). https://doi.org/10.1126/science.1240064
Shanker, O.: Defining dimension of a complex network. Mod. Phys. Lett. B 21(6), 321–326 (2007). https://doi.org/10.1142/s0217984907012773
Song, C.M., Gallos, L.K., Havlin, S., Makse, H.A.: How to calculate the fractal dimension of a complex network: the box covering algorithm. J. Stat. Mech-Theory Exp. p. 16 (2007). https://doi.org/10.1088/1742-5468/2007/03/p03006
Song, C.M., Havlin, S., Makse, H.A.: Origins of fractality in the growth of complex networks. Nat. Phys. 2(4), 275–281 (2006). https://doi.org/10.1038/nphys266
Uslan, V., Seker, H.: Quantitative prediction of peptide binding affinity by using hybrid fuzzy support vector regression. Appl. Comput. 43, 210–221 (2016). https://doi.org/10.1016/j.asoc.2016.01.024
Wang, J.: Robustness of complex networks with the local protection strategy against cascading failures. Saf. Sci. 53, 219–225 (2013). https://doi.org/10.1016/j.ssci.2012.09.011
Wang, J.W., Rong, L.L.: Cascade-based attack vulnerability on the us power grid. Saf. Sci. 47(10), 1332–1336 (2009). https://doi.org/10.1016/j.ssci.2009.02.002
Wang, Z., Xia, C.Y., Meloni, S., Zhou, C.S., Moreno, Y.: Impact of social punishment on cooperative behavior in complex networks. Sci. Rep. 3, 7 (2013). https://doi.org/10.1038/srep03055
Xu, H., Deng, Y.: Dependent evidence combination based on shearman coefficient and pearson coefficient. IEEE Access https://doi.org/10.1109/ACCESS.2017.2783320 (2018)
Xu, S., Jiang, W., Deng, X., Shou, Y.: A modified physarum-inspired model for the user equilibrium traffic assignment problem. Appl. Math. Model. 55, 340–353 (2018). https://doi.org/10.1016/j.apm.2017.07.032
Yin, L., Deng, Y.: Measuring transferring similarity via local information. Phys. A: Stat. Mech. Appl. (2018). https://doi.org/10.1016/j.physa.2017.12.144
Zadeh, L.: Fuzzy sets. Inf. Control evaluation Method Based 8(3), 338–353 (1965). https://doi.org/10.1016/S0019-9958(65)90241-X
Zhang, R., Ashuri, B., Deng, Y.: A novel method for forecasting time series based on fuzzy logic and visibility graph. Adv. Data Anal. Classif. 11(4), 759–783 (2018). https://doi.org/10.1007/s11634-017-0300-3
Zhang, X., Feng, L., Berman, Y., Hu, N., Stanley, H.E.: Exacerbated vulnerability of coupled socio-economic risk in complex networks. Epl 116(1), 6 (2016). https://doi.org/10.1209/0295-5075/116/18001
Zhao, Z.Q., Yu, Z.G., Anh, V., Wu, J.Y., Han, G.S.: Protein folding kinetic order prediction from amino acid sequence based on horizontal visibility network. Curr. Bioinf. 11(2), 173–185 (2016). https://doi.org/10.2174/1574893611666160125221326
Zheng, H., Deng, Y.: Evaluation method based on fuzzy relations between Dempster-Shafer belief structure. Int. J. Intell. Syst. (2017). https://doi.org/10.1002/int.21956
Zheng, X., Deng, Y.: Dependence assessment in human reliability analysis based on evidence credibility decay model and iowa operator. Ann. Nucl. Energy 112, 673–684 (2018)
Acknowledgements
The authors greatly appreciate the reviewer’s suggestions and the editor’s encouragement. The work is partially supported by National Natural Science Foundation of China (Program No. 61671384, 61703338), Natural Science Basic Research Plan in Shaanxi Province of China (Program No. 2016JM6018), Project of Science and Technology Foundation, and Fundamental Research Funds for the Central Universities (Program No. 3102017OQD020).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Wen, T., Song, M. & Jiang, W. Evaluating Topological Vulnerability Based on Fuzzy Fractal Dimension. Int. J. Fuzzy Syst. 20, 1956–1967 (2018). https://doi.org/10.1007/s40815-018-0457-8
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s40815-018-0457-8