Abstract
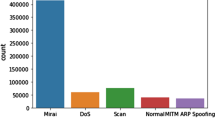
Internet of Things (IoT) devices are challenging to manage information security due to some factors such as processing capability, exponential growth in homes, and their low energy consumption which raises the risk of cyberattacks. One way to avoid cyberattacks is using an intrusion detection system that is able to recognize assaults while warning users so that appropriate countermeasures can be taken. Several deep learning and machine learning techniques have been used in the past to try to detect new assaults; however, these attempts have not been successful. In order to optimize IoT devices, in this study, we make a classification of network assaults using the convolutional neural network models mCNN and CNN. This study aims to assess the application of deep learning intrusion detection systems for IoT devices. The NF-UNSW-NB15-v2 dataset was used in this experiment to train the neural network. The network stream’s data were transformed into RGB images, which the neural network was trained on. The mCNN model outperformed the CNN model when compared to the proposed one for classifying network attacks. In addition, both networks perform better in most categories, with the exception of network attack detection, where the CNN performed worse than the suggested mCNN model.



Similar content being viewed by others
Data Availability
Not applicable.
References
Adeniji OD, Adeyemi SO, Ajagbe SA. An improved bagging ensemble in predicting mental disorder using hybridized random forest - artificial neural network model. Int J Comput Inform. 2022;46(4):543–550. https://doi.org/10.31449/inf.v46i4.3916.
Adhie RP, Hutama Y, Ahmar AS, Setiawan M, et al. Implementation cryptography data encryption standard (des) and triple data encryption standard (3DES) method in communication system based near field communication (NFC). J Phys Conf Ser. 2018;954: 012009.
Adimoolam M, John A, Balamurugan N, Ananth Kumar T. Green ICT communication, networking and data processing. In: Balusamy B, Chilamkurti N, Kadry S, editors. Green computing in smart cities: simulation and techniques. Berlin: Springer; 2021. p. 95–124.
Adly AS, Adly AS, Adly MS. Approaches based on artificial intelligence and the internet of intelligent things to prevent the spread of covid-19: scoping review. J Med Internet Res. 2020;22(8): e19104.
Ajagbe SA, Adesina AO, Ilupeju OA, Thanh DN et al. Challenges and perceptions in the use of ICT in student assessments during the covid-19 pandemic. In: 2021 8th international conference on information technology, computer and electrical engineering (ICITACEE). IEEE; 2021. pp. 89–94.
Ajagbe SA, Adigun MO. Deep learning techniques for detection and prediction of pandemic diseases: a systematic literature review. Multimed Tools Appl. 2023. https://doi.org/10.1007/s11042-023-15805-z.
Al-Emran M, Malik S.I, Al-Kabi MN. A survey of internet of things (IOT) in education: opportunities and challenges. In: Toward social internet of things (SIoT): enabling technologies, architectures and applications: emerging technologies for connected and smart social objects. Springer, Berlin; 2020. pp. 197–209.
Aljumah A. IOT-based intrusion detection system using convolution neural networks. PeerJ Comput Sci. 2021;7: e721.
Awotunde JB, Ajagbe SA, Florez H. Internet of things with wearable devices and artificial intelligence for elderly uninterrupted healthcare monitoring systems. In: International conference on applied informatics. Springer, Berlin; 2022. pp. 278–291.
Bansal SK. Towards a semantic extract-transform-load (ETL) framework for big data integration. In: 2014 IEEE international congress on big data. IEEE’ 2014. pp. 522–529.
Farooq MS, Riaz S, Abid A, Abid K, Naeem MA. A survey on the role of IOT in agriculture for the implementation of smart farming. IEEE Access. 2019;7:156237–71.
Gaber T, Awotunde JB, Folorunso SO, Ajagbe SA, Eldesouky E, et al. Industrial internet of things intrusion detection method using machine learning and optimization techniques. Wirel Commun Mob Comput. 2023;2023:1–15.
Hernandez J, Daza K, Florez H. Spiking neural network approach based on Caenorhabditis elegans worm for classification. IAENG Int J Comput Sci. 2022;49(4):1099–111.
Hernandez J, Daza K, Florez H, Misra S. Dynamic interface and access model by dead token for IOT systems. In: International conference on applied informatics. Springer; 2019. pp. 485–498.
Hernandez J, Florez H. An experimental comparison of algorithms for nodes clustering in a neural network of Caenorhabditis elegans. In: 21st international conference computational science and its applications. Springer; 2021. pp. 327–339.
Iyawa GE, Herselman M, Botha A. Digital health innovation ecosystems: from systematic literature review to conceptual framework. Proc Comput Sci. 2016;100:244–52.
Kodali RK, Yerroju S. Energy efficient home automation using IOT. In: 2018 international conference on communication, computing and Internet of Things (IC3IoT). IEEE; 2018. pp. 151–154.
Loshchilov I, Hutter F. Decoupled weight decay regularization. In: 7th international conference on learning representations; 2019.
Moustafa N, Slay J. Unsw-nb15: a comprehensive data set for network intrusion detection systems (UNSW-NB15 network data set). In: 2015 military communications and information systems conference (MilCIS). IEEE; 2015. pp. 1–6.
Nguyen SN, Nguyen VQ, Choi J, Kim K. Design and implementation of intrusion detection system using convolutional neural network for DOS detection. In: Proceedings of the 2nd international conference on machine learning and soft computing. 2018. pp. 34–38.
Rawat R, Oki OA, Sankaran S, Florez H, Ajagbe SA. Techniques for predicting dark web events focused on the delivery of illicit products and ordered crime. Int J Electr Comput Eng. 2023;13(5):5354–65.
Sarhan M, Layeghy S, Portmann M. Towards a standard feature set for network intrusion detection system datasets. Mob Netw Appl. 2022;27:357–70.
Sayed N, Shoaib M, Ahmed W, Qasem S, Albarrak A, Saeed F. Augmenting IOT intrusion detection system performance using deep neural network. Comput Mater Contin. 2022;74(1):1351–74.
Sergey Z, Komodakis N. Wide residual networks. In: British Machine Vision Association. 2016.
Vinod P, Jaipur R, Laxmi V, Gaur M. Survey on malware detection methods. In: Proceedings of the 3rd Hackers’ workshop on computer and internet security (IITKHACK’09). 2009. pp. 74–79.
Wang W, Zhao M, Wang J. Effective android malware detection with a hybrid model based on deep autoencoder and convolutional neural network. J Ambient Intell Hum Comput. 2019;10:3035–43.
Yang J, Deng J, Li S, Hao Y. Improved traffic detection with support vector machine based on restricted Boltzmann machine. Soft Comput. 2017;21:3101–12.
Funding
The authors declare that no fund was received for this study.
Author information
Authors and Affiliations
Contributions
SAA: conceptualization, writhing of original draft, validation, methodology, and coding. JBA: project administration, methodology, resource management, editing, and supervision. HF: resource management, review, editing, and supervision.
Corresponding author
Ethics declarations
Conflict of interest
The authors declare that they have no conflict of interest.
Ethics Approval
Not applicable.
Informed Consent
Not applicable.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
This article is part of the topical collection “Emerging Technologies in Applied Informatics” guest edited by Hector Florez and Marcelo Leon.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Ajagbe, S.A., Awotunde, J.B. & Florez, H. Ensuring Intrusion Detection for IoT Services Through an Improved CNN. SN COMPUT. SCI. 5, 49 (2024). https://doi.org/10.1007/s42979-023-02448-y
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s42979-023-02448-y