Abstract
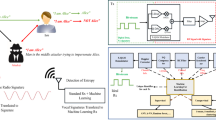
Cognitive radio (CR) technology is designed to improve reliability in communication between users through efficient and dynamic spectrum exploitation. CRs address the problems in spectrum allocation and channel access and improve the rate of radio resource utilization. The flexibility of the CR networks (CRN) and communication medium exposes it to a variety of threats; primary user emulation attack (PUEA) is a malicious and denial-of-service kind of adversary that defaces CRN performance. This manuscript proposes an adaptive learning-based attack detection in CRN for detecting and mitigating PUEA by analyzing the received power of the transmitter. The learning process endorses some beneficial features by distinguishing low spectrum legitimate PU from an adversary. The learning process adopts cyclostationary feature analysis for distinguishing adversaries and low power PU in CR communications. The process of learning is further enhanced by estimating distance variance and communication time-based analysis for improving the rate of signal classification and SU communication rate. The experimental analysis proves the stability of the proposed detection method by improving the SU throughput, with lesser signal classification time and misdetection probability.










Similar content being viewed by others
References
A. Abrardo, M. Barni, K. Kallas, B. Tondi, A game-theoretic framework for optimum decision fusion in the presence of by zantines. IEEE Trans. Inf. Forensics Secur. 11(6), 1333–1345 (2016)
S. Baskar, S. Periyanayagi, P.M. Shakeel, V.S. Dhulipala, An energy persistent range-dependent regulated transmission communication model for vehicular network applications. Comput. Netw. 152, 144–153 (2019)
K.M. Borle, B. Chen, W.K. Du, Physical layer spectrum usage authentication in cognitive radio: Analysis and implementation. IEEE Trans. Inf. Forensics Secur. 10(10), 2225–2235 (2015)
R.L. Chen, J.M. Park, Y.T. Hou, Toward secure distributed spectrum sensing in cognitive radio networks. IEEE Commun. Mag. 46(4), 50–55 (2008)
D. Das, S. Das, Intelligent resource allocation scheme for the cognitive radio network in the presence of primary user emulation attack. IET Commun. 11(15), 2370–2379 (2017)
X. Dong, Y. Gong, J. Ma, Y. Guo, Protecting operation-time privacy of primary users in downlink cognitive two-tier networks. IEEE Trans. Veh. Technol. 67(7), 6561–6572 (2018)
T. Duc-Tuyen, N. Nguyen-Thanh, P. Maille, P. Ciblat, and V. T. Nguyen, Mitigating selfish primary user emulation attacks in multi-channel cognitive radio networks: a surveillance game, in Proceedings of IEEE Globecom (2016)
S. M. Elghamrawy, Security in cognitive radio network: defense against primary user emulation attacks using genetic artificial bee colony (GABC) algorithm. Future Gener. Comput. Syst. (2018). https://doi.org/10.1016/j.future.2018.08.022
S. Fu, G. Zhang, L. Yang, Spectrum sensing defending against PUE attack based on fractal dimension. Clust. Comput. (2017). https://doi.org/10.1007/s10586-017-1427-x
M. Ghaznavi, A. Jamshidi, Defence against primary user emulation attack using statistical properties of the cognitive radio received power. IET Commun. 11(9), 1535–1542 (2017)
Q.M. Jiang, H.-F. Chen, L. Xie, K. Wang, On detecting primary user emulation attack using channel impulse response in the cognitive radio network. Front. Inf. Technol. Electron. Eng. 18(10), 1665–1676 (2017)
M. Karimi, S.M.S. Sadough, Efficient transmission strategy for cognitive radio systems under primary user emulation attack. IEEE Syst. J. 12(4), 3767–3774 (2018)
S.B.A. Khaliq, M.F. Amjad, H. Abbas, N. Shafqat, H. Afzal, Defence against PUE attacks in ad hoc cognitive radio networks: a mean field game approach. Telecommun. Syst. 70(1), 123–140 (2019)
S.C. Lin, C.Y. Wen, W.A. Sethares, Two-tier device-based authentication protocol against PUEA attacks for IoT applications. IEEE Trans. Signal Inf. Process. Netw. 4(1), 33–47 (2018)
M.H. Ling, K.-L.A. Yau, G.S. Poh, Trust and reputation management in cognitive radio networks: a survey. Secur. Commun. Netw. 7(11), 2160–2179 (2013)
S. Madbushi, R. Raut, M.S.S. Rukmini, Trust establishment in chaotic cognitive environment to improve attack detection accuracy under primary user emulation. Iran. J. Sci. Technol. Trans. Electr. Eng. 42(3), 291–297 (2018)
M.A. Mirza, M. Ahmad, M.A. Habib, N. Mahmood, C.M.N. Faisal, U. Ahmad, CDCSS: cluster-based distributed cooperative spectrum sensing model against primary user emulation (PUE) cyber attacks. J. Supercomput. 74(10), 5082–5098 (2018)
S.K.S.L. Preeth, R. Dhanalakshmi, R. Kumar, P.M. Shakeel, An adaptive fuzzy rule based energy efficient clustering and immune-inspired routing protocol for WSN-assisted IoT system. J. Ambient Intell. Humaniz. Comput. (2018). https://doi.org/10.1007/s12652-018-1154-z
D. Pu, B. Aygun, A.M. Wyglinski, Primary user emulation detection algorithm based on distributed sensor networks. Int. J. Wirel. Inf. Netw. 24(4), 344–355 (2017)
S. Shrivastava, A. Rajesh, P. Bora, Defense against primary user emulation attacks from the secondary user throughput perspective. AEU Int. J. Electron. Commun. 84, 131–143 (2018)
D.T. Ta, N. Nguyen-Thanh, P. Maille, V.-T. Nguyen, Strategic surveillance against primary user emulation attacks in cognitive radio networks. IEEE Trans. Cognit. Commun. Netw. 4(3), 582–596 (2018)
N.N. Thanh, P. Ciblat, A. Pham, V.-T. Nguyen, Surveillance strategies against primary user emulation attack in cognitive radio networks. IEEE Trans. Wirel. Commun. 14(9), 4981–4993 (2015)
N.L. Venkataraman, R. Kumar, P.M. Shakeel, Ant lion optimized bufferless routing in the design of low power application specific network on chip. Circuits Syst. Signal Process. 122, 122 (2019). https://doi.org/10.1007/s00034-019-01065-6
R. Yu, Y. Zhang, Y. Liu, S. Gjessing, M. Guizani, Securing cognitive radio networks against primary user emulation attacks. IEEE Netw. 29(4), 68–74 (2015)
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Arun, S., Umamaheswari, G. An Adaptive Learning-Based Attack Detection Technique for Mitigating Primary User Emulation in Cognitive Radio Networks. Circuits Syst Signal Process 39, 1071–1088 (2020). https://doi.org/10.1007/s00034-019-01123-z
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s00034-019-01123-z