Abstract
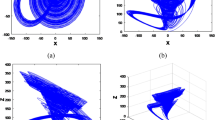
Secure hash functions, such as SHA-2 and SHA-3, play an important role in cryptography; however, they are unkeyed and cannot produce the specific hash value with a specified length. First, we constructed a 3D exponent chaotic map (3D-ECM) and analyzed its dynamical characteristics, which has ergodicity and better randomness within a larger parameter range, and can serve as sponge function to absorb message through parallel impulse perturbation to both exponent and state variable. The keyed hash function has a larger key space and can generate 224, 256, 384, 512 or longer hash value via parameter switcher. Theoretical analysis and numerical simulation demonstrated that the algorithm can meet all the performance requirements of a hash function in efficient and flexibility. Its practicable and reliable means high potential to be applied to blockchain or other cryptography area.






Similar content being viewed by others
References
Alawida M, Samsudin A, Teh JS (2019) Enhanced digital chaotic maps based on bit reversal with applications in random bit generators. Inf Sci 512:1155–1169
Bertoni G, Daemen J, Peeters M, et al (2011) The Keccak sponge function family. Submission to NIST’s SHA-3 competition
Cachin C (2017) Blockchain, cryptography, and consensus: invited presentation at the 10th interaction and concurrency experience. Electron Proc Theor Comput Sci 261:1
Chen L, Chen L, Jordan S, et al. (2016) Report on post-quantum cryptography. US Department of Commerce, National Institute of Standards and Technology
Chenaghlu MA, Jamali S, Khasmakhi NN (2016) A novel keyed parallel hashing scheme based on a new chaotic system. Chaos Solitons Fractals 87:216–225
Dworkin MJ (2015) Sha-3 standard: Permutation-based hash and extendable-output functions. Federal Inf. Process. Stds.(NIST FIPS)-202
Fox-Brewster T (2017). Google just 'Shattered' an old crypto algorithm-here's why that's big for web security
Guo W, Wang X, He D, Cao Y (2009) Cryptanalysis on a parallel keyed hash function based on chaotic maps. Phys Lett A 373(36):3201–3206
Kadir A, Aili M, Sattar M (2017) Color image encryption scheme using coupled hyper chaotic system with multiple impulse injections. Optik-Int J Light Electron Opt 129:231–238
Kanso A, Ghebleh M (2013) A fast and efficient chaos-based keyed hash function. Commun Nonlinear Sci Numer Simul 18(1):109–123
Kanso A, Yahyaoui H, Almulla M (2012) Keyed hash function based on a chaotic map. Inf Sci 186(1):249–264
Li X, Hou J (2016) Bursting phenomenon in a piecewise mechanical system with parameter perturbation in stiffness. Int J Non-Linear Mech 81:165–176
Li Y, Li X, Liu X (2017) A fast and efficient hash function based on generalized chaotic mapping with variable parameters. Neural Comput Appl 28(6):1405–1415
Lin Z, Guyeux C, Yu S et al (2017) On the use of chaotic iterations to design keyed hash function. Clust Comput 22(2):905–919
Liu H, Kadir A, Xu C (2020) Color image encryption with cipher feedback and coupling chaotic map. Int J Bifurc chaos 30(12):2050173
Santhanalakshmi S, Patra GK (2017) Design of secure cryptographic hash function using soft computing techniques. Int J Adv Soft Comput Appl. 9(2)
Sobti R, Geetha G (2012) Cryptographic hash functions: a review. IJCSI Int J Comput Sci Issues 9(2):461–479
Sotirov A, Stevens M, Appelbaum J, et al (2008) MD5 considered harmful today, creating a rogue CA certificate. In: 25th Annual chaos communication congress. (EPFL-CONF-164547)
Teh JS, Tan K, Alawida M (2019) A chaos-based keyed hash function based on fixed point representation. Clust Comput 22(1):649–660
Teh JS, Alawida M, Jia JH (2020) Unkeyed hash function based on chaotic sponge construction and fixed-point arithmetic. Nonlinear Dyn 2:713–729
Tiwari H, Asawa K (2014) Building a 256-bit hash function on a stronger MD variant. Open Comput Sci 4(2):67–85
Wang X, Yin YL, Yu H (2005) Finding collisions in the full SHA-1. Crypto 3621:17–36
Wu X, Wang D, Kurths J et al (2016) A novel lossless color image encryption scheme using 2D DWT and 6D hyperchaotic system. Inf Sci 349:137–153
Xiao D, Liao X, Deng S (2005) One-way Hash function construction based on the chaotic map with changeable-parameter. Chaos Solitons Fractals 24(1):65–71
Zhang YQ, Wang XY (2014) A symmetric image encryption algorithm based on mixed linear–nonlinear coupled map lattice. Inf Sci 273:329–351
Zhang YQ, Wang XY (2015) A new image encryption algorithm based on non-adjacent coupled map lattices. Appl Soft Comput 26:10–20
Acknowledgements
This research is supported by the National Natural Science Foundation of China (No.: 61662073).
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest
The Authors declare that they have no conflict of interest.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Liu, H., Wang, X. & Kadir, A. Constructing chaos-based hash function via parallel impulse perturbation. Soft Comput 25, 11077–11086 (2021). https://doi.org/10.1007/s00500-021-05849-4
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s00500-021-05849-4