Abstract
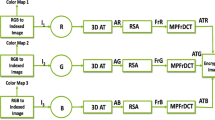
In this paper, we propose the general procedures for generating a visible RSA public key for overcoming the drawback of people (without cryptographic background) not understanding what is meant by “public key”. Instead of generating a randomlike public key, a visible public key system allows the user to use a predefined image (e.g., picture, photo, signet, or handwriting signature) as his/her visible public key such that other users can decode the image as the receiver’s/signer’s public key directly for encrypting a message or verifying a signature. Of course, our procedures can also be applied to a predefined sound and/or video to generate an audible or audio-visual public key. Two algorithms for generating visible RSA public keys based on generating RSA moduli with a predetermined portion are proposed. One is suitable for the environment where all users use a common exponent, and the other is for different exponents. The constructions are almost as efficient as the generation of RSA moduli with a predetermined portion. The quality of the resulting visible public keys is almost the same as the original image, without compromising security. Experimental results show that the size and quality of visible public keys can be accepted by human eyes for practical applications.
Similar content being viewed by others
References
ANSI X9.31 (May 1998) American national standard for financial services: digital signatures using reversible public key cryptography for the financial services industry (rDSA)
Bender W, Gruhl D, Morimoto N (1994) Techniques for data hiding. MIT Media Lab, Cambridge, MA. Technical report
Coppersmith D (1996) Finding a small root of a bivariate integer equation: faction with high bits known. In: Advances in Cryptology: Proceedings of EUROCRYPT’96. Lecture notes in computer science, vol 1070. Springer, Berlin Heidelberg New York, pp 178–189
Cox IJ, Killian J, Leighton T, Shannoon T (1997) Secure spread spectrum watermarking for multimedia. IEEE Trans Image Process 6(12):1673–1687
Girault M (1991) Self-certified public keys. In: Advances in Cryptology: Proceedings of EUROCRYPT’91. Lecture notes in computer science, vol 0547. Springer, Berlin Heidelberg New York, pp 490–497
Imai H (2002) Current trends of cryptology in Japan. In: Proceedings of the 2nd international workshop for Asian public key infrastructure, location, day month 2002, p 89
ITU.T X.509 (May 1997) Authentication framework
Koblitz N (1987) Elliptic curve cryptosystems. Math Comput 48:203–209
Kaliski B, Staddon J (1998) IETF RFC 2437: PKCS #1: RSA Cryptography Specifications version 2.0
Lenstra AK (1996) Generating RSA moduli with a predetermined portion. In: Advances in Cryptology: Proceedings of ASIACRYPT’98. Lecture notes in computer science, vol 1514. Springer, Berlin Heidelberg New York, pp 10–16
Lenstra AK (2001) Unbelievable security. Matching AES security using public key systems. In: Advances in Cryptology: Proceedings of ASIACRYPT 2001. Lecture notes in computer science, vol 2248. Springer, Berlin Heidelberg New York, pp 66–86
Lenstra AK, Verheul ER (2003) Selecting cryptographic key size. J Cryptol (in press). Available at: www.cryptosavvy.com
National Institute of Standards and Technology. http://csrc.nist.gov/encryption/aes
Netravali AN, Haskell BG (1995) Digital pictures: representation, compression, and standards, 2nd edn. Plenum Press, New York
Santesson S, Housley R, Freeman T (2002) Internet X.509 public key infrastructure logotypes in X. 509 certificates
Shamir A (1985) Identity-based cryptosystems and signature schemes. In: Advances in Cryptology: Proceedings of CRYPTO’84. Lecture notes in computer science, vol 0196. Springer, Berlin Heidelberg New York, pp 47–53
Taubman DS, Marcellin MW (2002) JPEG2000 – image compression fundamentals, standards and practice. Kluwer, Dordrecht
Vanstone SA, Zuccherato RJ (1995) Short RSA keys and their generation. J Cryptol volume:101–114
Zimmerman P (1995) PGP Source Code and Internals, MIT Press
Author information
Authors and Affiliations
Rights and permissions
About this article
Cite this article
Laih, C., Chen, K. Generating visible RSA public keys for PKI. IJIS 2, 103–109 (2004). https://doi.org/10.1007/s10207-003-0030-8
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10207-003-0030-8