Abstract
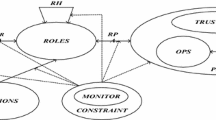
Access control is an important security mechanism for the protection of sensitive information and critical system resources. While it has been well-known that traditional access control models (TACMs), such as DAC, MAC, RBAC, etc., are not well suited for open networks due to the lack of dynamism in the management of access privileges, pro-active or dynamic access control models (PACMs) developed in recent years generally suffer from performance problems due to complex evaluation performed prior to access authorization. In game theory based dynamic access control models, which are one type of dynamic models, each access is modeled as a game that is played between the accessing subject and the accessed or protected object and the result of the play serves as the basis for making the authorization decision. Thus, delay is unavoidably introduced into the authorization process due to such pre-access evaluation. To overcome the shortcomings of TACMs and PACMs simultaneously, in this paper, we propose a new access control model called ISAC that, unlike all present access control models, is used not as a mechanism for access authorization but one for dynamic management of access privileges upon the completion of each access with the result being an updated set of access privileges for the accessing subject and used for updating the corresponding access control list for the subject. Access authorization will still be performed in the same way as that in the traditional access control models. Thus, ISAC offers the advantages of both traditional access control models in performance and pro-active access control models in dynamism. We will apply incomplete information static game to the development of ISAC in which we will show that there exists at least one Bayesian Nash equilibrium for the game play, which is the theoretical foundation for ISAC. We will also describe a framework design and an example implementation to illustrate the application of ISAC to access control. At last, we will present some experimental results to show that while maintaining the effectiveness of dynamic access control through the management of access privileges, ISAC can achieve the performance of traditional access control models.














Similar content being viewed by others
References
Lampson, B.W.: Protection. Proceeding of the 5th Princeton Symposium on Information Sciences and Systems, Princeton, NJ, pp. 437–443 (1971)
Snyder, L.: Formal models of capability-based protection systems. IEEE Trans. Comput. 30, 172–181 (1981)
Bell, D.E., LaPadula, L.: Secure computer systems: a mathematical model. In: Mitre Corporation, Bedford, MA, vol. 4, pp. 229–263 (1973)
Sandhu, R.S., Coyne, E.J., Feinstein, H.L., Youman, C.E.: Role-based access control models. IEEE Trans. Comput. 29(2), 38–47 (1996)
Ferraiolo, D., Kuhn, D.: Role-based access control. In: Proceeding of the NIST-NSA National (USA) Computer Security Conference, Baltimore, pp. 554–563 (1992)
Corradi, A., Montanari, R., Tibaldi, D.: Context-based access control management in ubiquitous environments. In: Proceeding of the 3rd IEEE International Symposium on Network Computing and Applications, Boston, pp. 253–260 (2004)
Rubart, J.: Context-based access control. Proceeding of the 2005 Symposia on Metainformatics, Esbjerg, pp. 145–156 (2005)
Yao, H., Hu, H., Lu, Z., Li, R.: Dynamic role and context-based access control for grid applications. In: Proceeding of the IEEE Region 10 Conference, Melbourne, pp. 1619–1625 (2005)
Betarte, G., Gatto, A., Martinez, R., Zipitria, F.: ACTkit: a framework for the definition and enforcement of role, content and context-based access control policies. IEEE Latin Am. Trans. 10(3), 1742–1751 (2012)
Shebaro, B., Oluwatimi, O., Bertino, E.: Context-based access control systems for mobile devices. IEEE Trans. Depend. Secure Comput. 12(2), 150–163 (2015)
Covington, M.J., Sastry, M.R.: A contextual attribute-based access control model. In: Proceedings of the 2006 International Conference on On the Move to Meaningful Internet Systems: AWeSOMe, CAMS, COMINF, IS, KSinBIT, MIOS-CIAO, MONET - Volume Part II, Montpellier, pp. 1996–2006 (2006)
Wang, B., Wang, L.: Design of attribute-based access control model for power information systems. Dianli Xitong Zidonghua 31(7), 81–84 (2007)
Kolter, J., Schillinger, R., Pernul, G.: A privacy-enhanced attribute-based access control system. In: Proceeding of the 21st Annual Conference on Data and Applications Security, Redondo, pp. 129–143 (2007)
Yeh, L., Chen, Y., Huang, J.: ABACS: an attribute-based access control system for emergency services over vehicular ad hoc networks. IEEE J. Sel. Areas Commun. 29(3), 630–643 (2011)
Xie, X., Ma, H., Li, J., Chen, X.: An efficient ciphertext-policy attribute-based access control towards revocation in cloud computing. J. Univ. Comput. Sci. 19(16), 2349–2367 (2013)
Hu, V., Kuhn, D., Ferraiolo, D.: Attribute-based access control. Computer 48(2), 85–88 (2015)
Ma, S., He, J., Shuai, X.: Application of fuzzy comprehensive evaluation method in trust quantification. Int. J. Comput. Intell. Syst. 4(5), 768–776 (2011)
Ma, S., He, J., Gao, F.: An access control model based on multi-factors trust. J. Netw. 7(1), 173–178 (2012)
Duan, J., Gao, D., Foh, C., Zhang, H.: TC-BAC: a trust and centrality degree based access control model in wireless sensor networks. Ad Hoc Netw. 11(8), 2675–2692 (2013)
Taylor, J.M., Sharif, H.R.: Security challenges and methods for protecting critical infrastructure cyber-physical systems. In: Proceeding of the 2017 International Conference on Selected Topics in Mobile and Wireless Networking, Avignon, pp. 1–6 (2017)
Fudenberg, D., Tirole, J.: Game Theory. MIT Press, Cambridge (1991)
Nash, J.: Equilibrium points in N-person games. Proc. Natl. Acad. Sci. U.S. Am. 36(1), 48–49 (1950)
Robert, D.: Game Theory for Applied Economists. Priceton University Press, Priceton (1992)
Chang, S.Y., Hu, Y.C.: SecureMAC: securing wireless medium access control against insider denial-of-service attacks. IEEE Trans. Mob. Comput. 16(12), 3527–3540 (2017)
Jang, H., Yun, S.-Y., Shin, J., Yi, Y.: Game theoretic perspective of optimal CSMA. IEEE Trans. Wirel. Commun. 17(1), 194–209 (2018)
Shahrokhzadeh, B., Dehghan, M.: A distributed game-theoretic approach for target coverage in visual sensor networks. IEEE Sens. J. 17(22), 7542–7552 (2017)
Hao, X., Wang, M., Hou, S., Gong, Q., Liu, B.: Distributed topology control and channel allocation algorithm for energy efficiency in wireless sensor network: from a game perspective. Wirel. Personal Commun. 80(4), 1557–1577 (2015)
Zhao, X., Zhang, X., Guo, H., Liu, Q.: The inter-cluster routing algorithm in wireless sensor network based on the game theory. In: Proceeding of the 4th International Conference on Digital Manufacturing and Automation, Qindao, pp. 1477–1480 (2013)
Maani, E., Chen, Z., Katsaggelos, A.: A game theoretic approach to video streaming over peer-to-peer networks. Signal Process. 27(5), 545–554 (2012)
Koutsopoulos, I., Tassiulas, L., Gkatzikis, L.: Client-server games and their equilibria in peer-to-peer networks. Comput. Netw. 67(12), 201–218 (2014)
Narang, P., Hota, C.: Game-theoretic strategies for IDS deployment in peer-to-peer networks. Inform. Syst. Front. 17(5), 1017–1028 (2015)
Anggorojati, B., Prasad, N., Prasad, R.: An intrusion detection game in access control system for the M2M local cloud platform. In: Proceeding of the 19th Asia-Pacific Conference on Communications, Bali, pp. 345–350 (2013)
Wong, W., Lee, W., Wei, H.: Base on game theory model to improve trust access control in cloud file-sharing system. In: Proceeding of the 10th International Conference on Intelligent Information Hiding and Multimedia Signal Processing, Kitakyushu, 702–705 (2014)
Liu, H., Li, X., Xu, M., Mo, R., Ma, J.: A fair data access control towards rational users in cloud storage. Inf. Sci. 418, 258–271 (2017)
Palomar E., Alcaide A., Molina E., Zhang Y.: Coalitional games for the management of anonymous access in online social networks. In: Proceeding of the 11th Annual International Conference on Privacy, Security and Trust, Tarragona, pp. 1–10 (2013)
Liu, E., Liu, Z., Shao, F., Zhang, Z.: A game-theoretical approach to multimedia social networks security. Sci. World J. 1, 1–9 (2014)
Zhang, S., Cai, W., Li, Y.: A game theory-based social network access control method. J. Northwest. Polytech. Univ. 29(4), 652–657 (2011). (in Chinese)
Zhang, Y., He, J., Zhao, B., Huang, Z., Liu, R.: Towards more pro-active access control in computer systems and networks. Comput. Secur. 49, 132–146 (2015)
Zhang, Y., He, J., Zhao, B., Liu, R.: Application of game theory for dynamic access control in security systems. Int. J. High Perform. Comput. Netw. 9(5/6), 451–461 (2016)
Harsanyi, J.C.: Games with incomplete information played by “Bayesian” players. Manage. Sci. 14(3), 159–182 (1967)
Acknowledgement
The work in this paper has been supported by National Natural Science Foundation of China (61602456) and National High Technology Research and Development Program of China (863 Program) (2015AA017204).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Zhu, N., Cai, F., He, J. et al. Management of access privileges for dynamic access control. Cluster Comput 22 (Suppl 4), 8899–8917 (2019). https://doi.org/10.1007/s10586-018-2018-1
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10586-018-2018-1