Abstract
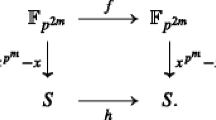
Based on the Feistel and MISTY structures, this paper presents several new constructions of complete permutation polynomials (CPPs) of the finite field \({\mathbb {F}}_{2^{n}}^2\) for a positive integer n and three constructions of CPPs over \({\mathbb {F}}_{p^{n}}^m\) for any prime p and positive integer \(m\ge 2\). In addition, we investigate the upper bound on the algebraic degree of these CPPs and show that some of them can have nearly optimal algebraic degree.
Similar content being viewed by others
References
Bartolia D., Giulietti M., Zinib G.: On monomial complete permutation polynomials. Finite Fields Appl. 41, 132–158 (2016).
Bassalygo L., Zinoviev V.: Permutation and complete permutation polynomials. Finite Fields Appl. 33, 198–211 (2015).
Diffie W., Ledin G. (translators): SMS4 encryption algorithm for wireless networks. https://eprint.iacr.org/2008/329.pdf.
Feng D., Feng X., Zhang W., et al.: Loiss: a byte-oriented stream cipher. In: IWCC’11 Proceedings of the Third International Conference on Coding and Cryptology, pp. 109-125. Springer, New York (2011).
Hou X.: Permutation polynomials over finite fields-a survey of recent advances. Finite Fields Appl. 32, 82–119 (2015).
Lidl R., Niederreiter H.: Finite Fields Encycl. Math. Appl. Cambridge University Press, Cambridge (1997).
Mann H.B.: The construction of orthogonal Latin squares. Ann. Math. Stat. 13(4), 418–423 (1942).
Markovski S., Mileva A.: Generating huge quasigroups from small non-linear bijections via extended Feistel function. Quasigroups Relat. Syst. 17(1), 91–106 (2009).
Matsui M.: New block encryption algorithm MISTY. In: Fast Software Encryption—FSE’97. Lect. Notes Comput. Sci, vol. 1267, pp. 54–68. Springer, New York (1997)
Mileva A., Markovski S.: Quasigroup representation of some Feistel and generalized Feistel ciphers. In: ICT Innovations 2012. Advances in Intelligent Systems and Computing, vol. 207, pp. 161–171. Springer, Berlin (2012).
Mileva A., Markovski S.: Shapeless quasigroups derived by Feistel orthomorphisms. Glas. Mat. 47(67), 333–349 (2012).
Mittenthal L.: Nonlinear dynamic substitution devices and methods for block substitutions employing coset decompositions and direct geometric generation. US Patent 5647001 (1997).
Mittenthal L.: Block substitutions using orthomorphic mappings. Adv. Appl. Math. 16(10), 59–71 (1995).
Mullen G.L., Panario D.: Handbook of Finite Fields. Taylor-Francis, Boca Raton (2013).
Muratovic-Ribic A., Pasalic E.: A note on complete mapping polynomials over finite fields and their applications in cryptography. Finite Fields Appl. 25, 306–315 (2014).
National Institute of Standards and Technology.: Data Encryption Standard, FIPS Publication 46-2 (1993). http://www.itl.nist.gov/fipspubs/fip46-2.htm.
Niederreiter H., Robinson K.H.: Complete mappings of finite fields. J. Aust. Math. Soc. A 33(2), 197–212 (1982).
Sarkar S., Bhattacharya S., Cesmelioglu A.: On some permutation binomials of the form \(x^{\frac{2^n-1}{k}+1}+ax\) over \({\mathbb{F}}_{2^n}\): existence and count. In: WAIFI, 2012. Lect. Notes Comput. Sci., vol. 7369, pp. 236–246. Springer, New York (2012).
Schnorr C.P., Vaudenay S.: Black box cryptanalysis of hash networks based on multipermutations. In: Advances in Cryptology-Eurocrypt’94, pp. 47–57. Springer, New York (1995).
Specification of SMS4, block cipher for WLAN products-SMS4 (in Chinese). http://www.oscca.gov.cn/UpFile/200621016423197990.pdf.
Stǎnicǎ P., Gangopadhyay S., Chaturvedi A., Gangopadhyay A.K., Maitra S.: Investigations on bent and negabent functions via the negaHadamard transform. IEEE Trans. Inf. Theory 58, 4064–4072 (2012).
Tu Z., Zeng X., Hu L.: Several classes of complete permutation polynomials. Finite Fields Appl. 25, 182–193 (2014).
Tuxanidy A., Wang Q.: Compositional inverses, complete mappings, orthogonal Latin squares and bent functions. arXiv:1409.6540 [math.NT] (2014).
Vaudenay S.: On the Lai-Massey scheme. In: Advances in Cryptology—ASIACRYPT’99. Lect. Notes Comput. Sci., vol. 1716, pp. 8–19. Springer, New York (1999).
Vaudenay S.: On the need for multipermutations: cryptanalysis of MD4 and SAFER. In: Fast Software Encryption—FSE’94. Lect. Notes Comput. Sci., vol. 1008, pp. 286–297. Springer, New York (1994).
Wan D.: On a problem of Niederreiter and Robinson about finite fields. J. Aust. Math. Soc. A 41(3), 336–338 (1986).
Wu B., Lin D.: On constructing complete permutation polynomials over finite fields of even characteristic. Discret. Appl. Math. 184, 213–222 (2015).
Wu G., Li N., Helleseth T., Zhang Y.: Some classes of monomial complete permutation polynomials over finite fields of characteristic two. Finite Fields Appl. 28, 148–165 (2014).
Wu G., Li N., Helleseth T., Zhang Y.: More classes of complete permutation polynomials over \({\mathbb{F}}_{q}\). Sci. China Math. 58(10), 1–14 (2015).
Xu G., Cao X.: Complete permutation polynomials over finite fields of odd characteristic. Finite Fields Appl. 31, 228–240 (2015).
Yuan Y., Tong Y., Zhang H.: Complete mapping polynomials over finite field \({\mathbb{F}}_{16}\). In: Arithmetic of Finite Fields. Lect. Notes Comput. Sci., vol. 4547, pp. 147–158. Springer, New York (2007).
Yuan P., Ding C.: Permutation polynomials over finite fields from a powerful lemma. Finite Fields Appl. 17(6), 560–574 (2011).
Zha Z., Hu L., Cao X.: Constructing permutations and complete permutations over finite fields via subfield-valued polynomials. Finite Fields Appl. 31, 162–177 (2015).
Acknowledgements
The authors would like to thank Prof. Xiwang Cao and Dr. Nian Li for their valuable discussions and suggestions. The authors also thank the anonymous referees whose comments significantly improved the quality of the paper. X. Zeng was supported by National Natural Science Foundation of China under Grant 61472120 and National Natural Science Foundation of Hubei Province of China under Grant 2017CFB143. The work of T. Helleseth and C. Li is supported by the Research Council of Norway; C. Li’s work is also partly supported by the research project (No. 720025) from UH-nett Vest in Norway and the National Natural Science Foundation of China under Grant 61771021.
Author information
Authors and Affiliations
Corresponding author
Additional information
Communicated by P. Charpin.
Rights and permissions
About this article
Cite this article
Xu, X., Li, C., Zeng, X. et al. Constructions of complete permutation polynomials. Des. Codes Cryptogr. 86, 2869–2892 (2018). https://doi.org/10.1007/s10623-018-0480-7
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10623-018-0480-7