Abstract
SNOW-V is a stream cipher recently designed for the 5G communication systems. This paper proposes two efficient algorithms to evaluate precise correlations of SNOW-V’s two main nonlinear components, fully considering the linear hull effects. Based on these algorithms, we can efficiently find more high-correlation linear approximations than before. The ideas of these algorithms can be generalized to other similar nonlinear components in symmetric cipher. We apply our algorithms to the full SNOW-V stream cipher to search for different types of high-correlation linear approximations. Our results depict more linear approximations with higher correlations than those recently proposed for full SNOW-V and SNOW-\(\text {V}_{\boxplus _{32},\boxplus _8}\). The best linear approximation we found has an absolute correlation \(2^{-47.567}\). There are at least 8, 135 and 1092 linear approximations, whose absolute correlations are greater than \(2^{-47.851}\), \(2^{-49}\) and \(2^{-50}\), respectively. These linear approximations can derive a fast correlation attack with time/memory/data complexities \(2^{240.86}\), \(2^{240.37}\) and \(2^{236.87}\), which is better than previously known fast correlation attacks on full SNOW-V. Moreover, we propose some properties for linear trails with three active S-boxes, which give a theoretical explanation of what the automatic search method lacks of. Our work provides more detailed linear approximation properties for the full SNOW-V.






Similar content being viewed by others
Notes
As the complexity of correlation attacks for reduced variants in [8] is very high, the corresponding result is not listed here.
References
Canteaut A., Trabbia M.: Improved fast correlation attacks using parity-check equations of weight 4 and 5. In: Preneel B. (ed.) Advances in Cryptology—EUROCRYPT 2000, pp. 573–588. Springer, Berlin (2000).
Chose P., Joux A., Mitton M.: Fast correlation attacks: an algorithmic point of view. In: Knudsen L.R. (ed.) Advances in Cryptology—EUROCRYPT 2002, pp. 209–221. Springer, Berlin (2002).
Clark A., Golić J.D., Dawson E.: A comparison of fast correlation attacks. In: Gollmann D. (ed.) Fast Software Encryption, pp. 145–157. Springer, Berlin (1996).
Clark A., Dawson E., Fuller J., Golić J., Lee H.-J., Millan W., Moon S.-J., Simpson L.: The LILI-II keystream generator. In: Batten L., Seberry J. (eds.) Information Security and Privacy, pp. 25–39. Springer, Berlin (2002).
Courtois N.T., Meier W.: Algebraic attacks on stream ciphers with linear feedback. In: Biham E. (ed.) Advances in Cryptology—EUROCRYPT 2003, pp. 345–359. Springer, Berlin (2003).
Ekdahl P., Johansson T.: SNOW-A new stream cipher. In: Proceedings of First Open NESSIE Workshop, KU-Leuven, pp. 167–168 (2000).
Ekdahl P., Johansson T.: A new version of the stream cipher SNOW. In: Nyberg K., Heys H. (eds.) Selected Areas in Cryptography, pp. 47–61. Springer, Berlin (2003).
Ekdahl P., Johansson T., Maximov A., Yang J.: A new SNOW stream cipher called SNOW-V. IACR Trans. Symmetric Cryptol. 2019(3), 1–42 (2019).
Funabiki Y., Todo Y., Isobe T., Morii M.: Several milp-aided attacks against SNOW 2.0. In: Camenisch J., Papadimitratos P. (eds.) Cryptology and Network Security, pp. 394–413. Springer, Cham (2018).
Gong X., Zhang B.: Fast computation of linear approximation over certain composition functions and applications to SNOW 2.0 and SNOW 3G. Des. Codes Cryptogr. 88, 2407–2431 (2020).
Gong X., Zhang B.: Resistance of SNOW-V against fast correlation attacks. IACR Trans. Symmetric Cryptol. 2021(1), 378–410 (2021).
Hoki J., Isobe T., Ito R., Liu F., Sakamoto K.: Distinguishing and key recovery attacks on the reduced-round SNOW-V and SNOW-Vi. Cryptology ePrint Archive, Report 2021/546. https://eprint.iacr.org/2021/546 (2021).
Johansson T., Jönsson F.: Fast correlation attacks based on turbo code techniques. In: Wiener M.J. (ed.) Advances in Cryptology—CRYPTO ’99, 19th Annual International Cryptology Conference, vol. 1666, pp. 181–197. Lecture Notes in Computer Science. Springer, Berlin (1999).
Johansson T., Jönsson F.: Fast correlation attacks through reconstruction of linear polynomials. In: Bellare M. (ed.) Advances in Cryptology—CRYPTO 2000, pp. 300–315. Springer, Berlin (2000).
Jönsson F., Johansson T.: A fast correlation attack on LILI-128. Inf. Process. Lett. 81(3), 127–132 (2002).
Maximov A.: Some observations on ZUC-256. Cryptology ePrint Archive, Paper 2021/1134. https://eprint.iacr.org/2021/1134 (2021).
Maximov A., Johansson T.: Fast computation of large distributions and its cryptographic applications. In: Roy B. (ed.) Advances in Cryptology—ASIACRYPT 2005, pp. 313–332. Springer, Berlin (2005).
Meier W., Staffelbach O.: Fast correlation attacks on certain stream ciphers. J. Cryptol. 1(3), 159–176 (1989).
Mihaljevi M.J., Fossorier M.P.C., Imai H.: Fast correlation attack algorithm with list decoding and an application. In: Matsui M. (ed.) Fast Software Encryption, pp. 196–210. Springer, Berlin (2002).
Mihaljević M.J., Golić J.D.: Convergence of a bayesian iterative error-correction procedure on a noisy shift register sequence. In: Rueppel R.A. (ed.) Advances in Cryptology—EUROCRYPT’ 92, pp. 124–137. Springer, Berlin (1993).
Nikolić I., Sasaki Y.: Refinements of the k-tree algorithm for the generalized birthday problem. In: Iwata T., Cheon J.H. (eds.) Advances in Cryptology—ASIACRYPT 2015, pp. 683–703. Springer, Berlin (2015).
Nyberg K., Wallén J.: Improved linear distinguishers for SNOW 2.0. In: Robshaw M. (ed.) Fast Software Encryption, pp. 144–162. Springer, Berlin (2006).
Shi Z., Jin C., Jin Y.: Improved linear approximations of SNOW-V and SNOW-Vi. Cryptology ePrint Archive, Report 2021/1105. https://ia.cr/2021/1105 (2021).
Shi Z., Jin C., Zhang J., Cui T., Ding L.: A correlation attack on full SNOW-V and SNOW-Vi. Cryptology ePrint Archive, Report 2021/1047. https://ia.cr/2021/1047 (2021).
Todo Y., Isobe T., Meier W., Aoki K., Zhang B.: Fast correlation attack revisited. In: Shacham H., Boldyreva A. (eds.) Advances in Cryptology—CRYPTO 2018, pp. 129–159. Springer, Cham (2018).
UEA2 &UIA I.: Specification of the 3GPP confidentiality and integrity algorithms UEA2 & UIA2. Document 2: SNOW 3G Specifications. Version: 1.1. ETSI. SAGE Specification (2006).
Yang J., Johansson T., Maximov A.: New improved attacks on SNOW-V. Cryptology ePrint Archive, Report 2021/544. https://eprint.iacr.org/2021/544 (2021).
Yang J., Johansson T., Maximov A.: Vectorized linear approximations for attacks on SNOW 3G. IACR Trans. Symmetric Cryptol. 2019(4), 249–271 (2019).
Yang J., Johansson T., Maximov A.: Spectral analysis of ZUC-256. IACR Trans. Symmetric Cryptol. 2020(1), 266–288 (2020).
Zhang B., Xu C., Meier W.: Fast correlation attacks over extension fields, large-unit linear approximation and cryptanalysis of SNOW 2.0. In: Gennaro R., Robshaw M. (eds.) Advances in Cryptology—CRYPTO 2015, pp. 643–662. Springer, Berlin (2015).
Funding
No funds, grants, or other support was received.
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Competing interests
The authors have no competing interests to declare that are relevant to the content of this article.
Additional information
Communicated by C. Mitchell.
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendices
Appendix A: Search for binary linear approximations of \(e2_t\)
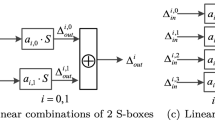
The technique of searching for linear approximations of \(e2_t\) is similar to that of \(e1_t\). The pruning strategy of Algorithm 1 is also applicable. A major difference is that the correlation of linear approximation of another S-box layer must be considered at the same time. Let \(c(u_k^b,h_k^b)\) denote the correlation of linear approximation for the S-box with the input mask \(u_k^b\) and the output mask \(h_k^b\). Algorithm 5 explains these differences in more detail.

Appendix B: A small-scale experiment to check the independency
Let the extension finite field \({\mathbb {F}}_{2^4}\cong {\mathbb {F}}_2[x]/(x^4+x+1)\), variables \(x,y,z\in {\mathbb {F}}_{2^4}^{3}\), and \(S^3\) denote three parallel S-boxes of the block cipher PRESENT. Suppose two linear approximations are as follows
where \(\Lambda ^{(1)}\xrightarrow {B}\Gamma ^{(1)}\). B is an MDS matrix, whose three rows are (1, 1, 2), (1, 2, 1) and (2, 1, 1), respectively.
To simplify the experiment, we require that \(\Lambda ^{(1)}=\Lambda ^{(2)}=\Lambda ^{(3)}\), \(\Gamma ^{(1)}=\Gamma ^{(3)}\) and \(\Lambda ^{(1)}\) is sparse. After computing their individual and joint probability distributions, we evaluate the relative entropy between the joint distribution and the multiplication of two individual distributions. The simulation results show that their differences are very tiny. For example, when \(\Gamma ^{(1)}=\Gamma ^{(3)}=(1,0,0,0)\), the relative entropy is 0.007913. The reason may be that the word weight of \(\Lambda ^{(1)}\) and \(\Gamma ^{(1)}\) are not equal.
Appendix C: Experiments for Algorithm 2
Table 3 indicates a group of test values for Algorithm 2. Furthermore, to verify Algorithm 2, some random sample experiments were performed. For example, let mask \(U=(\text {0x800081c1,0x80000081,0x00000000,0x80008080})\) and \(U=V=\sigma (W)=\sigma (T)\) holds. The theoretical correlation is \(2^{-13.68}\), calculated by Algorithm 2. As more than \(2^{-13.68\times 2}\) of samples are expected to verify the theoretical correlation, we computed empirical correlations through random sample experiments with sample size \(2^{30}\). Moreover, we performed 256 random experiments over several hours, each with a sample size of \(2^{30}\). The sample average and sample variance of the empirical correlation are \(2^{-13.70}\) and \(2^{-30.05}\), respectively, which means that the empirical and theoretical correlation is very close. This result more clearly confirms the theoretical correlation derived by Algorithm 1.
Appendix D: Some good masks of \(\sigma \) modular addition
Table 4 lists several groups of masks with high correlations when there are three active S-boxes. According to Sect. 5.1, we choose \(\Lambda ^{(3)} = \Lambda ^* \oplus \Lambda \). Each cell in the column of \(\Theta _{12}\) has one, two or three values, which are optimal choices for \(\Theta _{12}\). The last column illustrates the correlation \(|c(\sigma (\Theta ),\Lambda ^{(3)},\Lambda ^*)|\) corresponding to these different \(\Theta _{12}\). For example, \(|c(\sigma (\Theta ),\Lambda ^{(3)},\Lambda ^*)|=2^{-18}\) in the first row, when \(\Theta _{12}=\text {0x}c1\). The absolute correlation \(|c(\sigma (\Theta ),\Lambda ^{(3)},\Lambda ^*)|=2^{-19}\), when \(\Theta _{12}=\text {0x}a1\).
Appendix E: Linear approximations with high correlations for full SNOW-V
We list all the eight linear approximations with absolute correlation \(> 2^{-48}\) in Table 5, which corresponds to the work in Sect. 5.1. The last column shows the total correlations. We also list one linear approximation with absolute correlation \(2^{-87.24}\) in Table 6, which corresponds to the work in Sect. 5.2.
Rights and permissions
About this article
Cite this article
Zhou, Z., Feng, D. & Zhang, B. Efficient and extensive search for precise linear approximations with high correlations of full SNOW-V. Des. Codes Cryptogr. 90, 2449–2479 (2022). https://doi.org/10.1007/s10623-022-01090-8
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10623-022-01090-8