Abstract
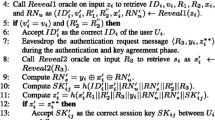
User authentication plays an important role to protect resources or services from being accessed by unauthorized users. In a recent paper, Das et al. proposed a secure and efficient uniqueness-and-anonymity-preserving remote user authentication scheme for connected health care. This scheme uses three factors, e.g. biometrics, password, and smart card, to protect the security. It protects user privacy and is believed to have many abilities to resist a range of network attacks, even if the secret information stored in the smart card is compromised. In this paper, we analyze the security of Das et al.’s scheme, and show that the scheme is in fact insecure against the replay attack, user impersonation attacks and off-line guessing attacks. Then, we also propose a robust uniqueness-and-anonymity-preserving remote user authentication scheme for connected health care. Compared with the existing schemes, our protocol uses a different user authentication mechanism to resist replay attack. We show that our proposed scheme can provide stronger security than previous protocols. Furthermore, we demonstrate the validity of the proposed scheme through the BAN (Burrows, Abadi, and Needham) logic.
Similar content being viewed by others
References
Burrows, M., Abadi, M., and Needham, R., A logic of authentication. ACM Trans. Comput. Syst. 8(1):18–36, 1990.
Chang, Y.-F., Yu, S.-H., and Shiao, D.-R., An uniqueness-and-anonymity-preserving remote user authentication scheme for connected healthcare. J. Med. Syst. 37:9902, 2013.
Chen, H. M., Lo, J. W., and Yeh, C. K., An efficient and secure dynamic ID-based authentication scheme for Telecare medical information systems. J. Med. Syst. 36(6):3907–3915, 2012.
Das, A. K., Analysis and improvement on an efficient biometric-based remote user authentication scheme using smart cards. IET Inf. Secur. 5(3):145–151, 2011.
Das, A. K., and Goswami, A., A secure and efficient uniqueness -and-anonymity-preserving remote user authentication scheme for connected health care. J. Med. Syst. 37:9948, 2013.
Das, M. L., Two-factor user authentication in wireless sensor networks. IEEE Trans. Wirel. Commun. 8(3):1086–1090, 2009.
Hwang, M. S., and Li, L. H., A new remote user authentication scheme using smart cards. IEEE Trans. Consum. Electron. 46(1):28–30, 2000.
Jina, A. T. B., Linga, D. N. C., and Goh, A., Biohashing: Two factor authentication featuring fingerprint data and tokenised random number. Pattern Recogn. 37(11):2245–2255, 2004.
Khan, M. K., Zhang, J., and Wang, X., Chaotic hash-based fingerprint biometric remote user authentication scheme on mobile devices. Chaos Solitons Fractals 35(3):519–524, 2008.
Kocher, P., Jaffe, J., and Jun, B., Differential power analysis. In: Proceedings of Advances in Cryptology-CRYPTO’99. Vol. 1666, pp. 388–397. LNCS, 1999.
Lee, N. Y., and Chiu, Y. C., Improved remote authentication scheme with smart card. Comput. Stand. Interfac. 27(2):177–180, 2005.
Li, C.-T., and Hwang, M.-S., An efficient biometric-based remote user authentication scheme using smart cards. J. Netw. Comput. Appl. 33:1–5, 2010.
Li, X., Niu, J.-W., Ma, J., Wang, W.-D., and Liu, C.-L., Cryptanalysis and improvement of a biometrics-based remote user authentication scheme using smart cards. J. Netw. Comput. Appl. 34:73–79, 2011.
Lumini, A., and Nanni, L., An improved BioHashing for human authentication. Pattern Recogn. 40(3):1057–1065, 2007.
Messerges, T. S., Dabbish, E. A., and Sloan, R. H., Examining smart-card security under the threat of power analysis attacks. IEEE Trans. Comput. 51(5):541–552, 2002.
Wen, F. T., Susilo, W., and Yang, G. M., A robust smart card-based anonymous user authentication protocol for wireless communications. Secur. Comm. Networks, 2013 doi:10.1002/sec.816.
Wen, F. T., Susilo, W., and Yang, G. M., A secure effective anonymous user authentication scheme for roaming service in global mobility networks. Wirel. Pers. Commun., 2013. doi:10.1007/s11277-013-1243-4.
Wu, Z.-Y., Lee, Y.-C., Lai, F., Lee, H.-C., and Chung, Y., A secure authentication scheme for Telecare medicine information systems. J. Med. Syst. 36(3):1529–35, 2010.
He, D.-B. H., Jianhua, C., and Rui, Z., A more secure authentication scheme for telecare medicine information systems. J. Med. Syst. 36(3):1989–1995, 2012.
Yang, G., Wong, D. S., Wang, H., Deng, X., Two-factor mutual authentication based on smart cards and passwords. J. Computer Syst. Sci. 74(7):1160–1172, 2008.
Author information
Authors and Affiliations
Corresponding author
Additional information
Conflict of interests
The authors declare that we have no conflict of interest.
Rights and permissions
About this article
Cite this article
Wen, F. A Robust Uniqueness-and-Anonymity-Preserving Remote User Authentication Scheme for Connected Health Care. J Med Syst 37, 9980 (2013). https://doi.org/10.1007/s10916-013-9980-1
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s10916-013-9980-1