Abstract
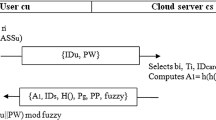
Authentication schemes are widely used mechanisms to thwart unauthorized access of resources over insecure networks. Several smart card based password authentication schemes have been proposed in the literature. In this paper, we demonstrate the security limitations of a recently proposed password based authentication scheme, and show that their scheme is still vulnerable to forgery and offline password guessing attacks and it is also unable to provide user anonymity, forward secrecy and mutual authentication. With the intention of fixing the weaknesses of that scheme, we present a secure authentication scheme. We show that the proposed scheme is invulnerable to various attacks together with attacks observed in the analyzed scheme through both rigorous formal and informal security analysis. Furthermore, the security analysis using the widely-accepted Real-Or-Random (ROR) model ensures that the proposed scheme provides the session key (SK) security. Finally, we carry out the performance evaluation of the proposed scheme and other related schemes, and the result favors that the proposed scheme provides better trade-off among security and performance as compared to other existing related schemes.







Similar content being viewed by others
References
Lamport L (1981) Password authentication with insecure communication. Commun ACM 24(11):770–772
Hwang T-Y (1983) Password authentication using public-key encryption. In: Proceedings of IEEE international Carnahan conference on security technology, pp 141–144
Harn L, Huang D, Laih CS (1989) Password authentication using public-key cryptography. Computers and Mathematics with Applications 18(12):1001–1017
Shimizu A (1991) A dynamic password authentication method using a one-way function. Systems and Computers in Japan 22(7):32–40
Neil H (1994) The s/key (tm) one-time password system. In: Symposium on network and distributed system security, pp 151–157
Shieh S-P, Yang W-H, Sun H-M (1997) An authentication protocol without trusted third party. IEEE Commun Lett 1(3):87–89
Sandirigama M, Shimizu A (2000) Simple and secure password authentication protocol (sas). IEICE Trans Commun 83(6):1363–1365
Chang C-C, Wu T-C (1991) Remote password authentication with smart cards. IEE Proceedings Computers and Digital Techniques 138(3):165–168
Hwang M-S, Li L-H (2000) A new remote user authentication scheme using smart cards. IEEE Trans Consum Electron 46(1):28–30
Chan C-K, Cheng L-M (2000) Cryptanalysis of a remote user authentication scheme using smart cards. IEEE Trans Consum Electron 46(4):992–993
Chang C-C (2003) Some forgery attacks on a remote user authentication scheme using smart cards. Informatica 14(3):289–294
Yeh H-T, Sun H-M, Hsieh B-T (2004) Security of a remote user authentication scheme using smart cards. IEICE Trans Commun 87(1):192–194
Sun H-M (2000) An efficient remote use authentication scheme using smart cards. IEEE Trans Consum Electron 46(4):958–961
Chien H-Y, Jan J-K, Tseng Y-M (2002) An efficient and practical solution to remote authentication: smart card. Comput Secur 21(4):372–375
Hsu C-L (2004) Security of Chien et al.’s remote user authentication scheme using smart cards. Computer Standards and Interfaces 26(3):167–169
Ku W-C, Chen S-M (2004) Weaknesses and improvements of an efficient password based remote user authentication scheme using smart cards. IEEE Trans Consum Electron 50(1):204–207
Lee S-W, Kim H-S, Yoo K-Y (2005) Improvement of Chien et al.’s remote user authentication scheme using smart cards. Computer Standards and Interfaces 27(2):181–183
Yoon E-J, Ryu E-K, Yoo K-Y (2004) Further improvement of an efficient password based remote user authentication scheme using smart cards. IEEE Trans Consum Electron 50(2):612–614
Sood SK, Sarje AK, Singh K (2010) An improvement of wang others.’s authentication scheme using smart cards. In: 2010 national conference on communications (NCC). IEEE, pp 1–5
Song R (2010) Advanced smart card based password authentication protocol. Computer Standards & Interfaces 32(5):321–325
Chen B-L, Kuo W-C, Wuu L-C (2014) Robust smart-card-based remote user password authentication scheme. Int J Commun Syst 27(2):377–389
Li X, Niu J, Khan MK, Liao J (2013) An enhanced smart card based remote user password authentication scheme. J Netw Comput Appl 36(5):1365–1371
Xu J, Zhu W-T, Feng D-G (2009) An improved smart card based password authentication scheme with provable security. Computer Standards & Interfaces 31(4):723–728
Jiang Q, Khan MK, Lu X, Ma J, He D (2016) A privacy preserving three-factor authentication protocol for e-health clouds. J Supercomput 72(10):3826–3849
Jiang Q, Chen Z, Li B, Shen J, Yang L, Ma J (2017) Security analysis and improvement of bio-hashing based three-factor authentication scheme for telecare medical information systems. J Ambient Intell Humaniz Comput:1–13
Das ML, Saxena A, Gulati VP (2004) A dynamic id-based remote user authentication scheme. IEEE Trans Consum Electron 50(2):629–631
Liao I-E, Lee C-C, Hwang M-S (2005) Security enhancement for a dynamic id-based remote user authentication scheme. In: International conference on next generation web services practices, 2005. NWeSP 2005. IEEE, p 4
Yoon E-J, Yoo K-Y (2006) Improving the dynamic id-based remote mutual authentication scheme. In: OTM confederated international conferences on the move to meaningful internet systems. Springer, pp 499–507
Wang Y-Y, Liu J-Y, Xiao F-X, Dan J (2009) A more efficient and secure dynamic id-based remote user authentication scheme. Comput Commun 32(4):583–585
Wen F, Li X (2012) An improved dynamic id-based remote user authentication with key agreement scheme. Comput Electr Eng 38(2):381–387
Chang Y-F, Tai W-L, Chang H-C (2014) Untraceable dynamic-identity-based remote user authentication scheme with verifiable password update. Int J Commun Syst 27(11):3430–3440
Jiang Q, Ma J, Li G, Li X (2015) Improvement of robust smart-card-based password authentication scheme. Int J Commun Syst 28(2):383–393
Xie Q, Dong N, Wong DS, Hu B (2016) Cryptanalysis and security enhancement of a robust two-factor authentication and key agreement protocol. Int J Commun Syst 29(3):478–487
Kumari S, Khan MK, Li X (2014) An improved remote user authentication scheme with key agreement. Comput Electr Eng 40(6):1997–2012
Lu Y, Li L, Peng H, Yang Y (2016) Robust anonymous two-factor authenticated key exchange scheme for mobile client-server environment. Security and Communication Networks 9(11):1331–1339
Wang D, Gu Q, Cheng H, Wang P (2016) The request for better measurement: a comparative evaluation of two-factor authentication schemes. In: Proceedings of the 11th ACM on Asia conference on computer and communications security. ACM, pp 475–486
Kaul SD, Awasthi AK (2016) Security enhancement of an improved remote user authentication scheme with key agreement. Wirel Pers Commun 89(2):621–637
Qi M, Chen J (2017) An efficient two-party authentication key exchange protocol for mobile environment. Int J Commun Syst 30(16):1–8
Wang C, Wang D, Xu G, Guo Y (2017) A lightweight password-based authentication protocol using smart card. Int J Commun Syst 30(16):1–11
Liao I-E, Lee C-C, Hwang M-S (2006) A password authentication scheme over insecure networks. J Comput Syst Sci 72(4):727–740
Wu S, Zhu Y, Pu Q (2012) Robust smart-cards-based user authentication scheme with user anonymity. Security and Communication Networks 5(2):236–248
Yang G, Wong DS, Wang H, Deng X (2008) Two-factor mutual authentication based on smart cards and passwords. J Comput Syst Sci 74(7):1160–1172
Madhusudhan R, Mittal RC (2012) Dynamic id-based remote user password authentication schemes using smart cards: a review. J Netw Comput Appl 35(4):1235–1248
Wang D, Cheng H, He D, Wang P (2018) On the challenges in designing identity-based privacy-preserving authentication schemes for mobile devices. IEEE Syst J 12(1):916–925
Karuppiah M (2016) Remote user authentication scheme using smart card: a review. Int J Internet Protoc Technol 9(2-3):107–120
Karuppiah M, Saravanan R (2014) A secure remote user mutual authentication scheme using smart cards. Journal of Information Security and Applications 19(4):282–294
Karuppiah M, Saravanan R (2015) A secure authentication scheme with user anonymity for roaming service in global mobility networks. Wirel Pers Commun 84(3):2055–2078
Wu F, Xu L, Kumari S, Li X, Das AK, Khan MK, Karuppiah M, Baliyan R (2016) A novel and provably secure authentication and key agreement scheme with user anonymity for global mobility networks. Security and Communication Networks 9(16):3527–3542
Karuppiah M, Saravanan R (2015) Cryptanalysis and an improvement of new remote mutual authentication scheme using smart cards. J Discret Math Sci Cryptogr 18(5):623–649
Wang D, Wang P, Liu J (2014) Improved privacy-preserving authentication scheme for roaming service in mobile networks. In: 2014 IEEE wireless communications and networking conference (WCNC). IEEE, pp 3136–3141
Dolev D, Yao A (1983) On the security of public key protocols. IEEE Trans Inf Theory 29(2):198–208
Kocher P, Jaffe J, Jun B (1999) Differential power analysis. In: Annual international cryptology conference. Springer, pp 388–397
Messerges TS, Dabbish EA, Sloan RH (2002) Examining smart-card security under the threat of power analysis attacks. IEEE Trans Comput 51(5):541–552
Ma C-G, Wang D, Zhao S-D (2014) Security flaws in two improved remote user authentication schemes using smart cards. Int J Commun Syst 27(10):2215–2227
Bonneau J, Herley C, Van Oorschot PC, Stajano F (2012) The quest to replace passwords: a framework for comparative evaluation of web authentication schemes. In: 2012 IEEE symposium on security and privacy. IEEE, pp 553–567
Odelu V, Das AK, Goswami A (2015) An efficient ECC-based privacy-preserving client authentication protocol with key agreement using smart card. Journal of Information Security and Applications 21:1–19
Sarkar P (2010) A simple and generic construction of authenticated encryption with associated data. ACM Trans Inf Syst Secur 13(4):33
Stinson DR (2006) Some observations on the theory of cryptographic hash functions. Des Codes Crypt 38 (2):259–277
Das AK (2013) A secure and effective user authentication and privacy preserving protocol with smart cards for wireless communications. Netw Sci 2(1):12–27
Abdalla M, Fouque PA, Pointcheval D (2005) Password-based authenticated key exchange in the three-party setting. In: 8th international workshop on theory and practice in public key cryptography public key cryptography (PKC 2005), vol 3386 of Lecture Notes in Computer Science, pp 65–84, Les Diablerets, Switzerland. Springer, Berlin
Chang CC, Le HD (2016) A provably secure, efficient, and flexible authentication scheme for ad hoc wireless sensor networks. IEEE Trans Wirel Commun 15(1):357–366
Das AK, Kumari S, Odelu V, Li X, Wu F, Huang X (2016) Provably secure user authentication and key agreement scheme for wireless sensor networks. Security and Communication Networks 9(16):3670–3687
Wang D, He D, Wang P, Chu C-H (2015) Anonymous two-factor authentication in distributed systems: certain goals are beyond attainment. IEEE Trans Dependable Secure Comput 12(4):428–442
Islam SK (2014) Design and analysis of an improved smartcard-based remote user password authentication scheme. Int J Commun Syst 29(11):1708–1719
Scott M, Costigan N, Abdulwahab W (2006) Implementing cryptographic pairings on smartcards. In: International workshop on cryptographic hardware and embedded systems. Springer, pp 134–147
Crypto+ + library. [online]. http://www.cryptopp.com
Acknowledgments
The authors would like to thank the anonymous reviewers and the editor for their valuable feedback on the paper which helped us to improve its quality and presentation.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Karuppiah, M., Das, A.K., Li, X. et al. Secure Remote User Mutual Authentication Scheme with Key Agreement for Cloud Environment. Mobile Netw Appl 24, 1046–1062 (2019). https://doi.org/10.1007/s11036-018-1061-8
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11036-018-1061-8