Abstract
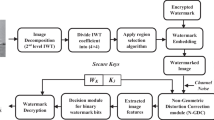
Imperceptibility, security, capacity, and robustness are among many aspects of image watermarking design. An ideal watermarking system should embed a large amount of information perfectly securely, but with no visible degradation to the host image. Many researchers have geared efforts towards developing specific techniques for variant applications. In this paper, we propose an adjustable-purpose, reversible and fragile watermarking scheme for image watermarking by particle swarm optimization (PSO). In general, given any host image and watermark, our scheme can provide an optimal watermarking solution. First, the content of a host image is analyzed to extract significant regions of interest (ROIs) automatically. The remaining regions of non-interest (RONIs) are collated for embedding watermarks by different amounts of bits determined by PSO to achieve optimal watermarking. The parameters can be adjusted relying upon user’s watermarking purposes. Experimental results show that the proposed technique has accomplished higher capacity and higher PSNR (peak signal-to-noise ratio) watermarking.












Similar content being viewed by others
References
Alattar AM (2004) Reversible watermark using the difference expansion of a generalized integer transform. IEEE Trans Image Processing 13(8):1147–1156
Al-Qershi OM, Khoo BE (2013) Two-dimensional difference expansion (2D-DE) scheme with a characteristics-based threshold. Signal Process 93(1):154–162
Arsalan M, Malik SA, Khan A (2012) Intelligent reversible watermarking in integer wavelet domain for medical images. J Syst Softw 85(4):883–894
Chadha R, Allison D (1988) Decomposing rectilinear figures into rectangles. In: Technical report. Virginia Polytechnic Institute and State University, Department of Computer Science, pp 1–34
Coatrieux G, Pan W, Cuppens-Boulahia N, Cuppens F, Roux C (2013) Reversible watermarking based on invariant image classification and dynamic histogram shifting. IEEE Transactions on information forensics and security 8(1):111–120
Chang CC, Tsai P, Lin CC (2005) SVD-based digital image watermarking scheme. Pattern Recogn Lett 26(10):1577–1586
Dittmann J, Nack F (2000) Copyright-copywrong. IEEE Multimedia 7(4):14–17
Guo C, Ma Q, Zhang L (2008) Spatio-temporal saliency detection using phase spectrum of quaternion Fourier transform. Proc. IEEE Conference on Computer Vision and Pattern Recognition, In, pp 1–8
Guo P, Wang J, Li B, Lee S (2014) A variable threshold-value authentication architecture for wireless mesh networks. Journal of Internet Technology 15(6):929–936
Honsinger CW, Jones PW, Rabbani M, Stoffel JC (2001) Lossless recovery of an original image containing embedded data. U.S. Patent No. 6,278,791. Washington, DC: U.S. Patent and Trademark Office.
Hou X, Zhang L (2007) Saliency detection: a spectral residual approach. Proc. IEEE Conference on Computer Vision and Pattern Recognition, In, pp 1–8
Huang J, Shi Y, Shi Y (2000) Embedding image watermarks in DC components. IEEE Trans Circuits and Systems for Video Technology 10(6):974–979
Itti L, Koch C, Niebur E (1998) A model of saliency-based visual attention for rapid scene analysis. IEEE Trans Pattern Analysis & Machine Intelligence 20(11):1254–1259
Ko LT, Chen JE, Shieh YS, Hsin HC, Sung TY (2011) Nested quantization index modulation for reversible watermarking and its application to healthcare information management systems. Computational and Mathematical Methods in Medicine 2012:1–8
Khan A, Malik SA (2014) A high capacity reversible watermarking approach for authenticating images: exploiting down-sampling, histogram processing, and block selection. Inf Sci 256(1):162–183
Khan A, Siddiqa A, Munib S, Malik SA (2014) A recent survey of reversible watermarking techniques. Inf Sci 279(9):251–272
Kennedy J (2010) Particle swarm optimization. In Encyclopedia of Machine Learning, Springer US, pp 760–766
Luo L, Chen Z, Chen M, Zeng X, Xiong Z (2010) Reversible image watermarking using interpolation technique. IEEE Transactions on information forensics and security 5(1):187–193
Li J, Li X, Yang B, Sun X (2015) Segmentation-based image copy-move forgery detection scheme. IEEE Trans Information Forensics and Security 10(3):507–518
Lin SD, Chen CF (2000) A robust DCT-based watermarking for copyright protection. IEEE Trans Consumer Electronics 46(3):415–421
Ni Z, Shi YQ, Ansari N, Su W (2006) Reversible data hiding. IEEE Transactions on Circuits and Systems for Video Technology 16(3):354–362
Qin C, Chang CC, Chiu YP (2014) A novel joint data-hiding and compression scheme based on SMVQ and image inpainting. IEEE Trans. Image Processing 23(3):969–978
Qin C, Chang CC, Hsu TJ (2015) Reversible data hiding scheme based on exploiting modification direction with two steganographic images. Multimedia Tools and Applications 74(15):5861–5872
Qin C, Zhang X (2015) Effective reversible data hiding in encrypted image with privacy protection for image content. J Vis Commun Image Represent 31(8):154–164
Ren Y, Shen J, Wang J, Han J, Lee S (2015) Mutual verifiable provable data auditing in public cloud storage. Journal of Internet Technology 16(2):317–323
Ruderman DL, Bialek W (1994) Statistics of natural images: scaling in the woods. Phys Rev Lett 73(6):814–822
Shih FY (2007) Digital watermarking and steganography: fundamentals and techniques. CRC Press, Boca Raton, FL
Sachnev V, Kim HJ, Nam J, Suresh S, Shi YQ (2009) Reversible watermarking algorithm using sorting and prediction. IEEE Transactions on Circuits and Systems for Video Technology 19(7):989–999
Shih FY, Wu YT (2005) Robust watermarking and compression for medical images based on genetic algorithms. Inf Sci 175(3):200–216
Srivastava A, Lee AB, Simoncelli EP, Zhu SC (2003) On advances in statistical modeling of natural images. Journal of Mathematical Imaging and Vision 18(1):17–33
Tudoroiu A., Caciula I, Coltuc D (2011) Block map implementation of difference expansion reversible watermarking. In IEEE 10th International Symposium on Signals, Circuits and Systems, pp. 1–4
Thodi DM, Rodríguez JJ (2007) Expansion embedding techniques for reversible watermarking. IEEE Trans Image Process 16(3):721–730
Thodi DM, Rodriguez JJ (2004) Prediction-error based reversible watermarking. In IEEE International Conference on Image Processing, pp. 1549–1552)
Tian J (2003) Reversible data embedding using a difference expansion. IEEE transaction on circuits Syst. Video Techn 13(8):890–896
Wang Z, Bovik AC (2002) A universal image quality index. IEEE Signal Processing Letters 9(3):81–84
Wang YR, Lin WH, Yang L (2011) An intelligent watermarking method based on particle swarm optimization. Expert Syst Appl 38(7):8024–8029
Xia Z, Wang X, Sun X, Liu Q, Xiong N (2016) Steganalysis of LSB matching using differences between nonadjacent pixels. Multimedia Tools and Applications 75(4):1947–1962
Xia Z, Wang X, Sun X, Wang B (2014) Steganalysis of least significant bit matching using multi-order differences. Security and Communication Networks 7(8):1283–1291
Xuan G, Yang C, Zhen Y, Shi YQ, Ni Z (2004) Reversible data hiding using integer wavelet transform and companding technique. In International Workshop on Digital Watermarking, pp. 115–124
Zhang X, Wang S (2007) Statistical fragile watermarking capable of locating individual tampered pixels. IEEE Signal Processing Letters 14(10):727–730
Zhang X, Wang S (2008) Fragile watermarking with error-free restoration capability. IEEE Trans Multimedia 10(8):1490–1499
Zheng Y, Jeon B, Xu D, Wu QM, Zhang H (2015) Image segmentation by generalized hierarchical fuzzy c-means algorithm. Journal of Intelligent and Fuzzy Systems 28(2):961–973
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Shih, F.Y., Zhong, X., Chang, IC. et al. An adjustable-purpose image watermarking technique by particle swarm optimization. Multimed Tools Appl 77, 1623–1642 (2018). https://doi.org/10.1007/s11042-017-4367-9
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-017-4367-9