Abstract
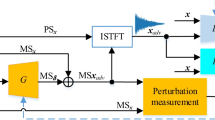
Environmental sounds, everyday audio events that do not consist of music or speech data and are often more diverse and chaotic in their structure, have proven to be a promising type of carrier signals to carry out covert communication as they occur frequently in the natural environment, e.g., marine communication by mimicking dolphin or sea lion whistles. However, a mass collection of the carrier signals still remains a challenging task. Recently proposed generator models represented by Generator Adversarial Nets (GAN) have provided an effective way to synthesize environmental sounds. In this study, an end-to-end convolutional neural network (CNN) is proposed to directly transform the randomly sampled Gaussian noise into environmental sound that contains the secret message. The proposed network structure is composed of upsampling groups and orthogonal quantization layer, which can simultaneously realize factor analysis and information embedding. The design of the orthogonal quantization layer to complete the message embedding task is inspired by spread spectrum, model-based modulation, and compensative quantization. The underlying idea in this study is to treat the secret message as the constraint information in the generative model with the aim of maximizing the complete data model. The alternating back-propagation algorithm is used to train the overall network. Experimental results show that the proposed scheme can generate realistic environmental sounds that convey secret messages, while guaranteeing a high degree of communication reliability.










Similar content being viewed by others
References
Bloch MR (2016) Covert communication over noisy channels: a resolvability perspective. IEEE Trans Inf Theory 62(5):2334–2354
Dol HS, Quesson J, Benders FPA (2008) Covert underwater communication with marine mammal sounds. Undersea Defence Technology-UDT Europe 2008
El-Atawy A, Duan Q, Al-Shaer ES (2017) A novel class of robust covert channels using out-of-order packets. IEEE Transactions on Dependable & Secure Computing 14(2):116–129
Fridrich J, Filler T (2007) Practical methods for minimizing embedding impact in steganography. Electronic Imaging 2007:650502–650502-650515
Goeckel D, Bash B, Guha S, Towsley D (2016) Covert communications when the warden does not know the background noise power. IEEE Commun Lett 20(2):236–239
Goodfellow IJ, Pouget-Abadie J, Mirza M, Xu B, Warde-Farley D, Ozair S, Courville A, Bengio Y (2012) Generative adversarial nets. International Conference on Neural Information Processing Systems, NIPS 2014:2672–2680
Han T, Lu Y, Zhu SC, Wu YN (2017) Alternating back-propagation for generator networks. The 31st AAAI conference on artificial intelligence. AAAI 2017:1–9
He B, Yan S, Zhou X, Lau VKN (2016) On covert communication with noise uncertainty. IEEE Commun Lett 21(4):941–944
Hu J, Yan S, Zhou X, Shu F, Wang J (2017) Covert communication in wireless relay networks. arXiv:1704.04946
Jia Y, Liu G, Zhang L (2015) Bionic camouflage underwater acoustic communication based on sea lion sounds. International Conference on Control, Automation and Information Sciences, ICCAIS 2015:332–336
Kingma DP, Welling M (2013) Auto-encoding variational Bayes. arXiv:1312.6114
Lecun Y, Bottou L, Bengio Y, Haffner P (1998) Gradient-based learning applied to document recognition. Proc IEEE 86(11):2278–2324
Liu S, Qiao G, Yang Y, Zhang L, Chen T (2013) Biologically inspired covert underwater acoustic communication using high frequency dolphin clicks. Oceans 2013:1–5
Liu S, Qiao G, Ismail A (2013) Covert underwater acoustic communication using dolphin sounds. The Journal of the Acoustical Society of America 133(4):EL300–EL306
Liu S, Qiao G, Ismail A, Liu B, Zhang L (2013) Covert underwater acoustic communication using whale noise masking on DSSS signal. Oceans:1–5
Ma Y, Luo X, Li X, Bao Z, Zhang Y (2018) Selection of rich model steganalysis features based on decision rough set α-positive region reduction. IEEE Transactions on Circuits and Systems for Video Technology. https://doi.org/10.1109/TCSVT.2018.2799243
Mazurczyk W, Szczypiorski K (2014) Trends in steganography. Commun ACM 57(3):86–95
McDermott Josh H, Simoncelli Eero P (2011) Sound texture perception via statistics of the auditory periphery: evidence from sound synthesis. Neuron 71(5):926–940
Mcdermott JH, Oxenham AJ, Simoncelli EP (2009) Sound texture synthesis via filter statistics. IEEE Workshop on Applications of Signal Processing to Audio and Acoustics, WASPAA 2009:297–300
Neal RM (2012) MCMC using Hamiltonian dynamics. Handbook of Markov Chain Monte Carlo, 2011, 2(11)
Normanhaignere S, Kanwisher NG, Mcdermott JH (2015) Distinct cortical pathways for music and speech revealed by hypothesis-free voxel decomposition. Neuron 88(6):1281–1296
Piczak KJ (2015) ESC: dataset for environmental sound classification. Proceedings of the 23rd ACM international conference on Multimedia, MM '15:1015–1018
Radford A, Metz L, Chintala S (2015) Unsupervised representation learning with deep convolutional generative adversarial networks. arXiv:1511.06434
Rubin DB, Thayer DT (1982) EM algorithms for ML factor analysis. Psychometrika 47(1):69–76
Sahidullah M, Saha G (2012) Design, analysis and experimental evaluation of block based transformation in MFCC computation for speaker recognition. Speech Comm 54(4):543–565
Sajjad M, Muhammad K, Baik SW, Rho S, Jan Z, Yeo SS, Mehmood I (2017) Mobile-cloud assisted framework for selective encryption of medical images with steganography for resource-constrained devices. Multimedia Tools & Applications 76(3):3519–3536
Shi H, Dong J, Wang W, Qian Y, Zhang X (2017) SSGAN: secure steganography based on generative adversarial networks. arXiv:1707.01613
Sobers TV, Bash BA, Guha S, Towsley D, Goeckel D (2016) Covert communication in the presence of an uninformed jammer. IEEE Trans Wirel Commun 16(9):6193–6206
Tang W, Tan S, Li B, Huang J (2017) Automatic steganographic distortion learning using a generative adversarial network. IEEE Signal Processing Letters 24(10):1547–1551
Tang W, Li B, Tan S, Barni M, Huang J (2018) CNN based adversarial embedding with minimum alteration for image steganography. arXiv:1803.09043
Vedaldi A, Lenc K (2015) MatConvNet: convolutional neural networks for MATLAB. Proceedings of the 23rd ACM international conference on Multimedia. MM '15: 689–692
Wendzel S, Zander S, Fechner B, Herdin C (2015) Pattern-based survey and categorization of network covert channel techniques. ACM Comput Surv 47(3):1–26
Xu G (2017) Deep convolutional neural network to detect J-UNIWARD. The 5th ACM Workshop on Information Hiding and Multimedia Security, IH&MMSec '17:67–73
Yang C, Luo X, Lu J, Liu F (2018) Extracting hidden messages of MLSB steganography based on optimal stego subset. SCIENCE CHINA Inf Sci. https://doi.org/10.1007/s11432-017-9328-2
Yang J, Liu K, Kang X, Wong EK, Shi YQ (2018) Spatial image steganography based on generative adversarial network. arXiv:1804.07939
Zhang Y, Qin C, Zhang W, Liu F, Luo X (2018) On the fault-tolerant performance for a class of robust image steganography. Signal Process 146:99–111
Acknowledgements
This work was supported by The National Natural Science Foundation of China (Grant No. 61602247, 61702235, U1636117, 61472188), Natural Science Foundation of Jiangsu Province (Grant No. BK20150472, BK20160840), CCF-VENUSTECH Foundation (Grant No. 2016011), Fundamental Research Funds for the Central Universities (30920140121006, 30915012208).
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Dai, Y., Liu, W., Liu, G. et al. An end-to-end generative network for environmental sound-based covert communication. Multimed Tools Appl 78, 8635–8653 (2019). https://doi.org/10.1007/s11042-018-6592-2
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-018-6592-2