Abstract
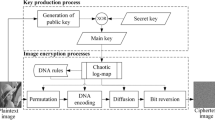
In this paper, a new chaotic steganography method based on Fuzzy Inference System (FIS), using Discrete Cosine Transform (DCT) on color and grayscale images is proposed. The proposed algorithm is designed in three different approaches to have important factors of robustness, imperceptibility, and transparency with respect to applications. In order to achieve this goal, important parameters in the Human Visual System (HVS), such as texture and luminance, using DCT coefficients are computed. For more precision and flexibility in selecting host blocks for embedding, FIS system is used. Due to the importance of robustness and transparency in different applications, the best target host blocks are intelligently determined using the degree defined in the fuzzy system. This flexibility greatly enhances the efficiency of the algorithm in various using goals. One of the outstanding aspects of the proposed method is error controlling with increasing capacity. At first, embedding is done on middle frequency (MF) then to increase the capacity, coefficients in high frequency are also considered with two different zigzag scanning directions in selection, middle to high (MHF) and high to middle (HMF). The ordering selection of different color channels (for color image), blocks, coefficients in embedding phase, and encryption algorithm of secret message are done by chaotic sequences which has a positive impact on security level. Providing an efficient integration technique (synchronization) in the number of coefficients of each block leads to increasing the security of the proposed method. One of best novelty which causes decreasing bit error rate (BER) beside increasing capacity, is approximating of the distortion during DCT and IDCT operations in embedding phase. The experimental results demonstrate that high level of transparency and robustness for MF, and if more capacity is needed, although both algorithms HMF and MHF have desirable results, but HMF provides higher level of transparency and MHF more robustness against noises and attacks which can be used with respect to applications.




















Similar content being viewed by others
References
Al-Dmour H, Al-Ani A (2016) A steganography embedding method based on edge identification and XOR coding. Expert Syst Appl 46:293–306
Artz D (2001) Digital steganography: hiding data within data. IEEE Internet Comput 5(3):75–80
Baig F, Khan MF, Beg S, Shah T, Saleem K (2016) Onion steganography: a novel layering approach. Nonlinear Dynamics 84(3):1431–1446
Bovik AC (ed) (2009) The essential guide to image processing. Academic Press, Cambridge
Chan CK, Cheng LM (2004) Hiding data in images by simple LSB substitution. Pattern Recogn 37(3):469–474
Chang CC, Chen TS, Chung LZ (2002) A steganographic method based upon JPEG and quantization table modification. Inf Sci 141(1):123–138
Chen, YZ, Han Z, Li SP, Lu CH, Yao XH (2010) An adaptive steganography algorithm based on block sensitivity vectors using HVS features. In Image and Signal Processing (CISP), 2010 3rd International Congress on (Vol. 3, pp. 1151–1155). IEEE
Chowdhuri P, Jana B, Giri D (2018) Secured steganographic scheme for highly compressed color image using weighted matrix through DCT. Int J Comput Appl 7:1–12
Chowdhuri P, Jana B, Giri D (2018) A Novel Steganographic Scheme Using Weighted Matrix in Transform Domain. In International Conference on Mathematics and Computing, pp. 27–35. Springer, Singapore.
Dande SC, Agrawal SS, Hirekhan SR (2016, April) Implementation of colour image steganography using LSB and edge detection technique: A LabVIEW approach. In Communication and Signal Processing (ICCSP), 2016 International Conference on (pp. 1466–1470). IEEE.
Darshni P, Ghanekar U (2015) A Hybrid Data Hiding Scheme to Enhance the Capacity of One-Third Probability Embedding Method. In Computational Intelligence & Communication Technology (CICT), 2015 IEEE International Conference on (pp. 269–272). IEEE
Doğan Ş (2016) A new data hiding method based on chaos embedded genetic algorithm for color image. Artif Intell Rev 46(1):129–143
El-Rahman SA (2018) A comparative analysis of image steganography based on DCT algorithm and steganography tool to hide nuclear reactors confidential information. Comput Electr Eng 70:380–399
Fan L, Gao T, Cao Y (2013) Improving the embedding efficiency of weight matrix-based steganography for grayscale images. Comput Electr Eng 39(3):873–881
Fridrich J (2009) Steganography in digital media: principles, algorithms, and applications. Cambridge University Press, Cambridge
Hu HT, Chang JR, Hsu LY (2016) Robust blind image watermarking by modulating the mean of partly sign-altered DCT coefficients guided by human visual perception. AEU-International Journal of Electronics and Communications 70(10):1374–1381
Huang F, Huang J, Shi YQ (2012) New channel selection rule for JPEG steganography. IEEE Transactions on Information Forensics and Security 7(4):1181–1191
Hussain M, Wahab AW, Idris YI, Ho AT, Jung KH (2018) Image steganography in spatial domain: A survey. Signal Process Image Commun 65:46–66
Jagadeesh B, Kumar PR, Reddy PC (2016) Robust digital image watermarking based on fuzzy inference system and back propagation neural networks using DCT. Soft Comput 20(9):3679–3686
Ker AD (2005) A general framework for structural steganalysis of LSB replacement. In International Workshop on Information Hiding. Springer Berlin Heidelberg, pp 296–311
Kocarev L, Lian S (2011) Chaos-based cryptography: Theory, algorithms and applications. Springer Science & Business Media, Berlin
Kumar S, Singh A, Kumar M (2019) Information hiding with adaptive steganography based on novel fuzzy edge identification. Defence Technology 15(2):162–169
Kumari S, Li X, Wu F, Das AK, Arshad H, Khan MK (2016) A user friendly mutual authentication and key agreement scheme for wireless sensor networks using chaotic maps. Futur Gener Comput Syst 63:56–75
Langelaar GC, Setyawan I, Lagendijk RL (2000) Watermarking digital image and video data. A state-of-the-art overview. IEEE Signal Process Mag 17(5):20–46
Lin GS, Chang YT, Lie WN (2010) A framework of enhancing image steganography with picture quality optimization and anti-steganalysis based on simulated annealing algorithm. IEEE Transactions on Multimedia 12(5):345–357
Lin CC, Shiu PF (2010) High capacity data hiding scheme for DCT-based images. Journal of Information Hiding and Multimedia Signal Processing 1(3):220–240
Lou DC, Hu MC, Liu JL (2008) Healthcare image watermarking scheme based on human visual model and back-propagation network. Journal of CCIT 37(1):151–162
Miri A, Faez K (2018) An image steganography method based on integer wavelet transform. Multimed Tools Appl:13133–13144
Morkel T, Eloff JH, Olivier MS (2005) An overview of image steganography. In ISSA (pp. 1–11)
Muhammad K, Ahmad J, Rehman NU, Jan Z, Sajjad M (2017) CISSKA-LSB: color image steganography using stego key-directed adaptive LSB substitution method. Multimed Tools Appl 76(6):8597–8626
Nazari M, Sharif A, Mollaeefar M (2016) An improved method for digital image fragile watermarking based on chaotic maps. Multimed Tools Appl:1–17
Nikooghadam M, Jahantigh R, Arshad H (2016) A lightweight authentication and key agreement protocol preserving user anonymity. Multimed Tools Appl:1–23
Oueslati S, Cherif A, Solaiman B (2010) A fuzzy watermarking approach based on the human visual system. International Journal of Image Processing 4(3):218–231
Provos N, Honeyman P (2003) Hide and seek: An introduction to steganography. IEEE security & privacy 99(3):32–44
Raid AM, Khedr WM, El-Dosuky MA, Ahmed W (2014) JPEG image compression using discrete cosine transform-A Survey. arXiv preprint arXiv:1405.6147
Saidi M, Hermassi H, Rhouma R, Belghith S (2017) A new adaptive image steganography scheme based on DCT and chaotic map. Multimed Tools Appl 76(11):13493–13510
Sajasi S, Moghadam AME (2015) An adaptive image steganographic scheme based on noise visibility function and an optimal chaotic based encryption method. Appl Soft Comput 30:375–389
Sajedi H, Jamzad M (2008) Cover selection steganography method based on similarity of image blocks. In Computer and Information Technology Workshops, 2008. CIT Workshops 2008. IEEE 8th International Conference on (pp. 379–384). IEEE
Sakr N, Zhao J, Groza V (2005) A dynamic fuzzy logic approach to adaptive HVS-based watermarking. In Haptic Audio Visual Environments and their Applications, 2005. IEEE International Workshop on (pp. 6-pp). IEEE
Shi YQ, Sun H (1999) Image and video compression for multimedia engineering: Fundamentals, algorithms, and standards. CRC press, Boca Raton
Silman J (2001) Steganography and steganalysis: an overview. Sans Institute 3:61–76
Srivastava A, Lee AB, Simoncelli EP, Zhu SC (2003) On advances in statistical modeling of natural images. Journal of mathematical imaging and vision 18(1):17–33
Suchitra B, Priya M, Raju J (2013) Image Steganography Based On DCT Algorithm for Data Hiding. International Journal of Advanced Research in Computer Engineering & Technology (IJARCET) 2(11)
Sun W, Lu ZM, Wen YC, Yu FX, Shen RJ (2013) High performance reversible data hiding for block truncation coding compressed images. SIViP 7(2):297–306
Vanmathi C, Prabu S (2018) Image Steganography Using Fuzzy Logic and Chaotic for Large Payload and High Imperceptibility. International Journal of Fuzzy Systems 20(2):460–473
Walia E, Jain P, Navdeep N (2010) An analysis of LSB & DCT based steganography. Global Journal of Computer Science and Technology 10(1)
Wang Z, Bovik AC, Sheikh HR, Simoncelli EP (2004) Image quality assessment: From error measurement to structural similarity. IEEE Trans Image Process 13(1)
Yang CN, Kim C, Lo YH (2018) Adaptive real-time reversible data hiding for JPEG images. J Real-Time Image Proc 14(1):147–157
Zhang M, Tong X (2014) A new chaotic map based image encryption schemes for several image formats. J Syst Softw 98:140–154
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Nazari, M., Dorostkar Ahmadi, I. A novel chaotic steganography method with three approaches for color and grayscale images based on FIS and DCT with flexible capacity. Multimed Tools Appl 79, 13693–13724 (2020). https://doi.org/10.1007/s11042-019-08415-1
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-019-08415-1