Abstract
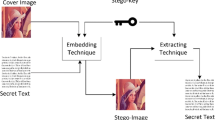
In this study, a new high-capacity, low-distortion, and reversible data hiding method based on RGB that hides color images inside color images is proposed. The proposed method divides the 24-bit image into 8-bit (1byte) meaningful segments, and the first most important 4 bits of the 8-bit data are hidden directly while the less important negligible 4-bit is not hidden and it is completed by rounding at approximate value through the function. The first 4 bits hidden in extraction are combined with the 4 bits from the function to retrieve 1 byte of information. In this way, since the 8-bit data is reduced to 4 bits, the method performs lossy hiding. Since the size of the data reduces by half owing to this method, it offers twice the capacity compared to the traditional LSB methods. When the same amount of data is hidden, the method creates lower distortion in the cover image than traditional LSB methods. Peak signal to noise ratio (PSNR) and structural similarity quality criterion (SSIM), which are frequently used in the literature, are used to measure the image quality of the proposed method. The test results showed that the proposed method achieved twice as much capacity in comparison to the traditional LSB method, higher efficiency than the studies in the literature, and higher PSNR and SSIM values as undetectable are obtained.











Similar content being viewed by others
References
Abdulla AA (2015) Exploiting Similarities Between Secret and Cover Images for Improved Embedding Efficiency and Security in Digital Steganography. Dissertation, The University of Buckingham
Abdulla AA, Jassim SA, Sellahewa H (2013) Secure Steganography Technique Based on Bitplane Indexes, 2013 IEEE Intern Symp Multimedia 287–291. https://doi.org/10.1109/ISM.2013.55
Abdulla AA, Sellahewa H, Jassim SA (2014) Steganography based on pixel intensity value decomposition, Proc. SPIE 9120, Mobile Multimedia/Image Process Sec App 2014, 912005 (28 May 2014); https://doi.org/10.1117/12.2050518
Abdulla AA, Sellahewa H, Jassim SA (2019) Improving embedding efficiency for digital steganography by exploiting similarities between secret and cover images. Multimed Tools Appl 78:17799–17823. https://doi.org/10.1007/s11042-019-7166-7
Chan C (2009) On Using LSB Matching Function for Data Hiding in Pixels. Fundamenta Informaticae 96(1–2): 49–59. https://doi.org/10.3233/FI-2009-166
Chen B, Luo W, Zheng P, Huang J (2020) Universal stego post-processing for enhancing image steganography. J Inform Secur App 55. https://doi.org/10.1016/j.jisa.2020.102664
Duan X, Gou M, Liu N, Wang W, Qin C (2020) High-capacity image steganography based on improved Xception. Sensors 20(24):1–16. https://doi.org/10.3390/s20247253
Durdu A (2007) Analysis of steganographed audio files with the guide of artificial neural networks. Dissertation, Dissertation, Sakarya University
Durdu A (2016) A high capacity reversible steganography method based on LSB mapping area for hiding lossy images into images. Dissertation, Sakarya University
Hore A, Ziou D (2010) Image Quality Metrics: PSNR vs. SSIM, 2010 20th International Conference on Pattern Recognition, Istanbul 2366–2369. https://doi.org/10.1109/ICPR.2010.579
Islam MR, Tanni TR, Parvin S, Sultana MJ, Siddiqa A (2020) A modified LSB image steganography method using filtering algorithm and stream of password. Inform Secur J. https://doi.org/10.1080/19393555.2020.1854902
Karakus S, Avci E (2020) A new image steganography method with optimum pixel similarity for data hiding in medical images. Med Hypotheses 139. https://doi.org/10.1016/j.mehy.2020.109691
Kalaichelvi V, Meenakshi P, Vimala Devi P, Manikandan H, Venkateswari P, Swaminathan S (2020) A stable image steganography: a novel approach based on modified RSA algorithm and 2–4 least significant bit (LSB) technique. J Ambient Intell Humaniz Comput. https://doi.org/10.1007/s12652-020-02398-w
Khan S, Abbas N, Nasir M, Haseeb K, Saba T, Rehman A, Mehmood Z (2020) Steganography-assisted secure localization of smart devices in internet of multimedia things (IoMT). Multimedia Tools App. https://doi.org/10.1007/s11042-020-09652-5
Khodaei M, Faez K (2012) New adaptive steganographic method using least-significant-bit substitution and pixel-value differencing. IET Image Proc 6(6):677–686. https://doi.org/10.1049/iet-ipr.2011.0059
Laishram D, Tuithung T (2020) A novel minimal distortion-based edge adaptive image steganography scheme using local complexity: (BEASS). Multimedia Tools App. https://doi.org/10.1007/s11042-020-09519-9
Liao X, Yin J, Chen M, Qin Z (2020) Adaptive Payload Distribution in Multiple Images Steganography Based on Image Texture Features. IEEE Trans Dependable Secur Comput 1–1. https://doi.org/10.1109/tdsc.2020.3004708
Liao X, Yu Y, Li B, Li Z, Qin Z (2020) A New Payload Partition Strategy in Color Image Steganography. IEEE Trans Circuits Syst Video Technol 30(3):685–696. https://doi.org/10.1109/TCSVT.2019.2896270
Liu HH, Su PC, Hsu MH (2020) An Improved Steganography Method Based on Least-Significant-Bit Substitution and Pixel-Value Differencing. KSII Trans Internet Inf Syst 14(11):4537–4556. https://doi.org/10.3837/tiis.2020.11.016
Mandal JK, Das D (2012) Steganography using adaptive pixel value differencing(APVD)of gray images through exclusion of overflow/underflow. In 2nd Int Conf Comp Sci Eng App (CCSEA-2012), Delhi, India. https://doi.org/10.5121/csit.2012.2211
Mielikainen J (2006) LSB matching revisited. IEEE Signal Process Lett 13(5):285–287. https://doi.org/10.1109/LSP.2006.870357
Olcay C, Saran N (2013) İmge İçine Bilgi Gizlemede Kullanılan LSB Yöntemlerinin Karşılaştırması. Çankaya Univ J Sci Eng 10(1):17–32
Sharp T (2001) An Implementation of Key-Based Digital Signal Steganography. In: Moskowitz I.S. (eds) Information Hiding. IH 2001. Lecture Notes in Computer Science, Springer, Berlin, Heidelberg 2137. https://doi.org/10.1007/3-540-45496-92
Shen SY, Huang LH (2015) A data hiding scheme using pixel value differencing and improving exploiting modification directions. Comput Secur 48:131–141. https://doi.org/10.1016/j.cose.2014.07.008
Swain G (2016) Adaptive pixel value differencing steganography using both vertical and horizontal edges. Multimedia Tools App 75(21):13541–13556. https://doi.org/10.1007/s11042-015-2937-2
Tuncer T (2018) A probabilistic image authentication method based on chaos. Multimedia Tools Appl 77:21463–21480. https://doi.org/10.1007/s11042-017-5569-x
Wang Z, Bovik AC, Sheikh HR, Simoncelli EP (2004) Image quality assessment: From error visibility to structural similarity. IEEE Trans Image Process 13(4):600–612. https://doi.org/10.1109/TIP.2003.819861
Wang Y, Tang M, Wang Z (2020) High-capacity adaptive steganography based on LSB and Hamming code. Optik 213. https://doi.org/10.1016/j.ijleo.2020.164685
Wu D, Tsai W (2003) A steganographic method for images by pixel-value differencing. Pattern Recogn Lett 24(9–10):1613–1626. https://doi.org/10.1016/S0167-8655(02)00402-6
Yang CY, Wang WF (2015) Block-based colour image steganography using smart pixel-adjustment. In: Sun H, Yang CY, Lin CW, Pan JS, Snasel V, Abraham A (eds) Genetic and Evolutionary Computing. Adv Intelligent Syst Comput Springer, Germany, pp 145–154
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Durdu, A. A new reversible low-distortion steganography method that hides images into RGB images with low loss. Multimed Tools Appl 81, 953–973 (2022). https://doi.org/10.1007/s11042-021-11405-x
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-021-11405-x