Abstract
In this paper, we propose a new scheme on implementing the quantum key distribution with two-intensity weak coherent light and compare its performance with other existing methods. Through numerical simulations, we demonstrate that our new scheme can exceed almost all other existing decoy-state methods, e.g., the standard three-intensity decoy-state method and the usual passive decoy-state method, both in the transmission distance and in the final key generation rate, approaching very closely to the ideal case of using an infinite number of decoy states. Besides, we also consider the finite-size key effect. We demonstrate that under current experimental conditions, even when taking statistical fluctuation into account, a quite high key generation rate can still be obtained at very long transmission distance by applying our new scheme.





Similar content being viewed by others
References
Bennett, C.H., Brassard, G.: Quantum cryptography: public key distribution and coin tossing. In: Proceedings of the IEEE international conference on computers, systems and signal processing, pp. 175–179. IEEE, New York (1984)
Lo, H.K., Chau, H.F.: Unconditional security of quantum key distribution over arbitrarily long distances. Science 283, 2050 (1999)
Shor, P.W., Preskill, J.: Simple proof of security of the BB84 quantum key distribution protocol. Phys. Rev. Lett. 85, 441 (2000)
Mayers, D.: Unconditional security in quantum cryptography. J. ACM 48, 351 (2001)
Brassard, G., Lütkenhaus, N., Mor, T., Sanders, B.C.: Limitations on practical quantum cryptography. Phys. Rev. Lett. 85, 1330 (2000)
Lütkenhaus, N.: Security against individual attacks for realistic quantum key distribution. Phys. Rev. A 61, 052304 (2000)
Lütkenhaus, N., Jahma, M.: Quantum key distribution with realistic states: photon-number statistics in the photon-number splitting attack. New J. Phys. 4, 44.1 (2002)
Hwang, W.Y.: Quantum key distribution with high loss: toward global secure communication. Phys. Rev. Lett. 91, 057901 (2003)
Wang, X.B.: Decoy-state protocol for quantum cryptography with four different intensities of coherent light. Phys. Rev. A. 72, 012322 (2005)
Wang, X.B.: Beating the photon-number-splitting attack in practical quantum cryptography. Phys. Rev. Lett. 94, 230503 (2005)
Lo, H.K., Ma, X.F., Chen, K.: Decoy state quantum key distribution. Phys. Rev. Lett. 94, 230504 (2005)
Ma, X.F., Qi, B., Zhao, Y., Lo, H.K.: Practical decoy state for quantum key distribution. Phys. Rev. A 72, 012326 (2005)
Wang, Q., Wang, X.B., Guo, G.C.: Practical decoy state for quantum key distribution. Phys. Rev. A 75, 012312 (2007)
Scarani, V., Acín, A., Ribordy, G., Gisin, N.: Practical decoy-state method in quantum key distribution with a heralded single-photon source. Phys. Rev. Lett. 92, 057901 (2004)
Acín, A., Brunner, N., Gisin, N., Massar, S., Pironio, S., Scarani, V.: Device-independent security of quantum cryptography against collective attacks. Phys. Rev. Lett. 98, 230501 (2007)
Branciard, C., Cavalcanti, E.G., Walborn, S.P., Scarani, V., Wiseman, H.M.: One-sided device-independent quantum key distribution: security, feasibility, and the connection with steering. Phys. Rev. A 85, 010301 (2012)
Braunstein, S.L., Pirandola, S.: Side-channel-free quantum key distribution. Phys. Rev. Lett. 108, 130502 (2012)
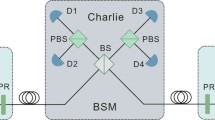
Lo, H.K., Curty, M., Qi, B.: Measurement-device-independent quantum key distribution. Phys. Rev. Lett. 108, 130503 (2012)
Tamaki, K., Lo, H.K., Fung, C.H.F., Qi, B.: Phase encoding schemes for measurement-device-independent quantum key distribution with basis-dependent flaw. Phys. Rev. A 85, 042307 (2012)
Wang, Q., Wang, X.B.: Efficient implementation of the decoy-state measurement-device-independent quantum key distribution with heralded signal-photon sources. Phys. Rev. A 88, 052332 (2013)
Zhao, Y., Qi, B., Ma, X.F., Lo, H.K., Qian, L.: Experimental quantum key distribution with decoy states. Phys. Rev. Lett. 96, 070502 (2006)
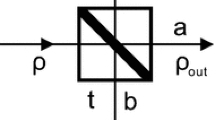
Curty, M., Ma, X., Qi, B., Moroder, T.: Passive decoy-state quantum key distribution with practical light sources. Phys. Rev. A 81, 022310 (2010)
Mauerer, W., Sliberhorn, C.: Quantum key distribution with passive decoy state selection. Phys. Rev. A 75, 050305 (2007)
Zhou, Y.H., Yu, Z.W., Wang, X.B.: Tightened estimation can improve the key rate of measure-device-independent quantum key distribution by more than 100 %. Phys. Rev. A 89, 052325 (2014)
Zhou, C., Bao, W.S., Chen, W., Li, H.W., Yin, Z.Q., Wang, Y., Han, Z.F.: Phase-encoded measurement-device-independent quantum key distribution with practical spontaneous-parametric-down-conversion sources. Phys. Rev. A 88, 052333 (2013)
Tang, Y.L., Yin, H.L., Chen, S.J., Liu, Y., Zhang, W.J., Jiang, X., Zhang, L., Wang, J., You, L.X., Guan, J.Y., Yang, D.X., Wang, Z., Liang, H., Zhang, Z., Zhou, N., Ma, X.F., Chen, T.Y., Zhang, Q., Pan, J.W.: Measurement-device-independent quantum key distribution over 200 km. Phys. Rev. Lett. 113, 190501 (2014)
Fung, C.H.F., Qi, B., Tamaki, K., Lo, H.K.: Phase-remapping attack in practical quantum-key-distribution systems. Phys. Rev. A 75, 032314 (2007)
Qi, B., Fung, C.H.F., Lo, H.K., Ma, X.F.: Time-shift attack in practical quantum cryptosystems. Quantum Inf. Comput. 7, 73 (2007)
Lydersen, L., Wiechers, C., Wittmann, C., Elser, D., Skaar, J., Makarov, V.: Hacking commercial quantum cryptography systems by tailored bright illumination. Nat. Photonics 4, 686 (2010)
Jain, N., Wittmann, C., Lydersen, L., Wiechers, C., Elser, D., Marquardt, C., Makarov, V., Leuchs, G.: Device calibration impacts security of quantum key distribution. Phys. Rev. Lett. 107, 110501 (2011)
Acknowledgments
We gratefully acknowledge the financial support from the National Natural Science Foundation of China through Grants Nos. 11274178, 11311140250, and 61475197, the Project Funded by the Priority Academic Program Development of Jiangsu Higher Education Institutions through Grants No. YX002001, and the Scientific Research Foundation of Nanjing University of Posts and Telecommunications through Grant Nos. NY212011 and NY214142.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Zhu, F., Zhou, XY., Liu, AP. et al. A new scheme on improving the performance of the quantum key distribution with two-intensity weak coherent light. Quantum Inf Process 14, 3773–3784 (2015). https://doi.org/10.1007/s11128-015-1081-2
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11128-015-1081-2