Abstract
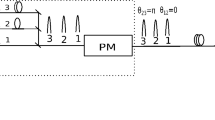
We propose a multiple-pulse phase-matching quantum key distribution protocol to exceed the linear key rate bound and to achieve higher error tolerance. In our protocol, Alice and Bob generate at first their own pulse train (each train should contain L pulses) as well as random bit sequences and also encode each pulse of their train with a randomized phase and a modulation phase. As the next step, both encoded trains are simultaneously sent to Charlie, who performs an interference detection and may be also an eavesdropper. After a successful detection is announced by Charlie, Alice and Bob open the randomized phase of each pulse and keep only communications when the summation of the difference randomized phases at two success detections’ time stamps for Alice and Bob is equal to 0 or \(\pi \). Thereafter, Alice and Bob compute the sifted key with the time stamps. The above procedure is repeated until both Alice and Bob achieve sufficiently long sifted keys. We can also show that the secret key rate of the proposed QKD protocol can beat the rate-loss limit of so far known QKD protocols when the transmission distance is greater than 150–175 km. Moreover, the proposed protocol has a higher error tolerance, approximately 22.5%, when the transmission distance is 50 km and \(L = 128\). The secret key rate and the transmission distance of our protocol are superior to that of the round-robin differential phase shift quantum key distribution protocol Sasaki et al. (Nature 509:475–480, 2014) and the measurement-device-independent quantum key distribution protocol Lo et al. (Phys Rev Lett 108:130503, 2012), and the secret key rate performance is better in both cases than that of phase-matching quantum key distribution when bit train length is greater than 16.





Similar content being viewed by others
References
Bennett, C.H., Brassard, G.: Quantum cryptography: public-key distribution and coin tossing. Proc. IEEE Int. Conf. Comput. Syst. Signal Process. 175–179 (1984)
Gisin, N., Ribordy, G., Tittel, W., Zbinden, H.: Quantum cryptography. Rev. Mod. Phys. 74, 145 (2002)
Wang, X.-B.: Beating the photon-number-splitting attack in practical quantum cryptography. Phys. Rev. Lett. 94, 230503 (2005)
Wang, X.-B.: Three-intensity decoy-state method for device-independent quantum key distribution with basis-dependent errors. Phys. Rev. A 87, 012320 (2013)
Lo, H.K., Curty, M., Qi, B.: Measurement-device-independent quantum key distribution. Phys. Rev. Lett. 108, 130503 (2012)
Braunstein, S.L., Pirandola, S.: Side-channel-free quantum key distribution. Phys. Rev. Lett. 108, 130502 (2012)
Sasaki, T., Yamamoto, Y., Koashi, M.: Practical quantum key distribution protocol without monitoring signal disturbance. Nature 509, 475–478 (2014)
Ma, X., Qi, B., Zhao, Y., Lo, H.K.: Practical decoy state for quantum key distribution. Phys. Rev. A 72, 012326 (2005)
Lo, H.K., Ma, X., Chen, K.: Decoy state quantum key distribution. Phys. Rev. Lett. 94, 230504 (2005)
Lucamarini, M., Yuan, Z.L., Dynes, J.F., Shields, A.J.: Overcoming the rate-distance barrier of quantum key distribution without using quantum repeaters. Nature 557, 400–403 (2018)
Inamori, H., Lütkenhaus, N., Mayers, D.: Unconditional security of practical quantum key distribution. Eur. Phys. J. D 41, 599 (2007)
Wang, L., Zhao, S.-M., Gong, L.-Y., Cheng, W.-W.: Free-space measurement-device-independent quantum-key-distribution protocol using decoy states with orbital angular momentum. Chin. Phys. B 24, 120307 (2015)
Wang, S., Yin, Z.-Q., Chen, W.: Experimental demonstration of quantum key distribution without monitoring of the signal disturbance. Nat. Photonics 9, 832–836 (2015)
Wang, L., Zhao, S.-M.: Round-robin differential-phase-shift quantum key distribution with heralded pair-coherent sources. Quantum Inf. Process. 16, 100 (2017)
Chen, D., Zhao, S.H., Shi, L., Liu, Y.: Measurement-device-independent quantum key distribution with pairs of vector vortex beams. Phys. Rev. A 93, 032320 (2016)
Wang, X.Y., Zhao, S.H., Dong, C., Zhu, Z.D., Gu, W.Y.: Orbital angular momentum-encoded measurement device independent quantum key distribution under atmospheric turbulence. Quantum Inf. Process. 18, 304 (2019)
Zhou, Y.-H., Yu, Z.-W., Wang, X.-B.: Making the decoy-state measurement-device-independent quantum key distribution practically useful. Phys. Rev. A 93, 042324 (2016)
Yin, H.-L., Chen, T.-Y., Yu, Z.-W.: Measurement-device-independent quantum key distribution over a 404 km optical fiber. Phys. Rev. Lett. 117, 190501 (2016)
Curty, M., Lewenstein, M., Lütkenhaus, N.: Entanglement as a precondition for secure quantum key distribution. Phys. Rev. Lett. 92, 217903 (2004)
Azuma, K., Mizutani, A., Lo, H.K.: Fundamental rate-loss trade-off for the optical quantum key distribution. Nat. Commun. 7, 13523 (2016)
Pirandola, S., Laurenza, R., Ottaviani, C., Banchi, L.: Fundamental limits of repeaterless quantum communications. Nat. Commun. 8, 15043 (2017)
Sangouard, N., Simon, C., De Riedmatten, H., Gisin, N.: Quantum repeaters based on atomic ensembles and linear optics. Rev. Mod. Phys. 83, 33 (2011)
Tamaki, K., Lo, H.K., Wang, W., Lucamarini, M.: Information theoretic security of quantum key distribution overcoming the repeaterless secret key capacity bound. arxiv:1805.05511 (2018)
Ma, X.-F., Zeng, P., Zhou, H.: Phase-matching quantum key distribution. Phys. Rev. X 8, 031043 (2018)
Wang, X.-B., Yu, Z.-W., Hu, X.-L.: Sending or not sending: twin-field quantum key distribution with large misalignment error. Phys. Rev. A 98, 062323 (2018)
Cui, C., Yin, Z.-Q., Wang, R.: Twin-field quantum key distribution without phase postselection. Phys. Rev. A 11, 034053 (2018)
Mao, Q.-P., Wang, L., Zhao, S.-M.: Plug-and-play round-robin differential phase-shift quantum key distribution. Sci. Rep. 7, 15435 (2017)
Guan, J.-Y., Can, Z., Liu, Y.: Experimental passive round-robin differential phase-shift quantum key distribution. Phys. Rev. Lett. 114, 180502 (2015)
Gottesman, D., Lo, H.K., Lütkenhaus, N., Preskill, J.: Security of quantum key distribution with imperfect devices. Quantum Inf. Comput. 4, 325 (2004)
Acknowledgements
The paper is supported in part by the National Natural Science Foundation of China (61871234 and 11847062) and the open research fund of Key Lab of Broadband Wireless Communication and Sensor Network Technology, Ministry of Education (Grant No. JZNY201710).
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendices
Appendix A
The quantum states of Alice and Bob are given by
respectively, where \(\hat{a}_{m}^{+}, \hat{b}_{m}^{+}\) are the creation operator of Alice’s and Bob’s m-th position at a and b paths, respectively, as shown in Fig. 1. After the interference by the beam splitter which replaces \(\hat{a}_{m}^{+}\) by \((\hat{c}_{m}^{+}+\hat{d}_{m}^{+})/\sqrt{2}\) and \(\hat{b}_{n}^{+}\) by \((\hat{c}_{m}^{+}-\hat{d}_{n}^{+})/\sqrt{2}\), the output result becomes
There are six items in the output result, and only the last four items are kept, since the detection results are discarded when there is only one click in the detectors. The four items’ probabilities are,
Appendix B
Here, the detector results and the sifted key for Alice(Bob) when \(\big |\phi _A^{m}+\phi _B^{n}-\phi _A^{n}-\phi _B^{m}\big |=0\) are listed in Table 2. The detector results are divided into two types, denoted as SAME which represents the two clicks triggered by the same detector, and DIFF which represents the two clicks triggered by different detectors.
Rights and permissions
About this article
Cite this article
Chen, G., Wang, L., Li, W. et al. Multiple-pulse phase-matching quantum key distribution. Quantum Inf Process 19, 416 (2020). https://doi.org/10.1007/s11128-020-02920-1
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11128-020-02920-1