Abstract
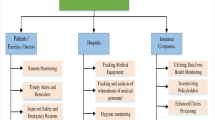
With the development in IT technology and with growing demands of users, a ubiquitous environment is being made. Because individual identification is important in ubiquitous environment, RFID technology would be used frequently. RFID is a radio frequency identification technology to replace bar code. The reader transmits query (request of user information) and tag-provides user information. RFID has various advantages, such as high speed identification rates, mass memory storages. However, eavesdropping is possible as well as a problem that user information is exposed (Juels et al. in Conference on Computer and Communications Security—ACM CCS, pp. 103–111, 2003; Ohkubo et al. in RFID Privacy Workshop 2003; Weis et al. in International Conference on Security in Pervasive Computing, pp. 201–212, 2003; Weis et al. in Cryptographic Hardware and Embedded Systems—CHES, pp. 454–469, 2002). Therefore, when off-line customer had visited bank for banking service, RNTS (RFID number ticket service) system provides both anonymity in customer identification and efficiency of banking service. In addition, RNTS system protects privacy of an off-line user visiting the bank and it is an efficient method offering service in order of arriving in the bank.
Similar content being viewed by others
References
Juels A, Revest, Szydlo M (2003) The blocker tag: selective blocking of RFID tags for consumer privacy. In: Conference on computer and communications security-ACM CCS, pp 103–111
Ohkubo M, Suzuki K, Kinoshita S (2003) Cryptographic approach to ‘privacy-friendly’ tags. In: RFID Privacy Workshop
Weis S, Sarma S, Rivest R, Engels D (2003) Security and privacy aspects of low-cost radio frequency identification systems. In: International conference on security in pervasive computing, pp 201–212
Weis S, Sarma S, Engels D (2002) RFID systems and security and privacy implications. In: Cryptographic hardware and embedded systems-CHES, pp 454–469
Vajda I, Buttyan L (2003) Lightweight authentication protocols for low-cost RFID tags. In: UBICOMP 2003
Weis S, Sarma S, Rivest R, Engels D (2003) Security and privacy aspects of low-cost radio frequency identification systems. In: International conference on security in pervasive computing, pp 201–212
Henrici D, Mullerm P (2004) Hash-based enhancement of location privacy for radio-frequency identification devices using varying identifiers. In: Workshop on pervasive computing and communications security—PerSec, pp 219–224
Hwang Y-J, Lee S-M, Lee DH, Lim JI (2004) Low-cost RFID authentication protocol in ubiquitous environment. In: Conference on information security and cryptology—Summer, vol 14, no 1, pp 109–114
Yang J, Park J, Lee H, Ren K, Kim K (2005) Mutual authentication protocol for low-cost RFID. In: Encrypt workshop
Peris-Lopez P, Hernandez-Castro J, Estevez-Tapiador J, Ribagorda A (2006) EMAP: An efficient mutual authentication protocol for low-cost RFID tags. In: OTM federated conferences and workshop: IS workshop
Peris-Lopez P, Hernandez-Castro J, Estevez-Tapiador J, Ribagorda A (2006) LMAP: A real lightweight mutual authentication protocol for low-cost RFID tags. In: Workshop on RFID security
Peris-Lopez P, Hernandez-Castro J, Estevez-Tapiador J, Ribagorda A (2006) M2AP: A minimalist mutual-authentication protocol for low-cost RFID tags. In: International conference on ubiquitous intelligence and computing—UIC 2006
Weis S (2003) Security and privacy in radio-frequency identification devices. Masters thesis
Weis S, Sarma S, Engels D (2002) RFID systems and security and privacy implications. In: Cryptographic hardware and embedded systems—CHES, pp 454–469
Yoo SH, Kim K, Hwang YH, Lee PJ (2004) Status-based RFID authentication protocol. J Korea Inst Inf Secur Cryptol 14(6):57–68
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Jeong, C.H., Ahn, K.S. Efficient RNTS system for privacy of banking off-line customer. J Supercomput 55, 307–319 (2011). https://doi.org/10.1007/s11227-009-0346-x
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11227-009-0346-x