Abstract
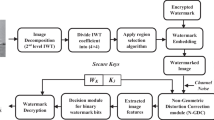
Spread spectrum modulation based watermarking has proved to be effective, robust and cryptographically secure. It hides watermark by spreading its spectrum with a pseudo-noise (PN) sequence and then adding them to a host image as a watermarked image. In regular approaches, to achieve PN sequence at the transmitter, receiver must use a separate channel for detecting hidden information. The unique PN sequence must have a low cross correlation and thereby can be duplicated easily by hostile attackers. In this paper a novel approach based on the Self-Encoded Spread Spectrum (SESS) is proposed. PN code is derived from the original image signal itself and the spreading sequence of watermark signal is recovered without any information from the transmitter. It is contributed a higher secure feature by using of the time-varying SESS. Genetic algorithm is applied to achieve best BER and PAD by optimizing Spreading Length, Quantization Length, payload capacity and Signal to interference ratio.










Similar content being viewed by others
References
Ghosh, S., Ray, P., Maity, S. P., & Rahaman, H. (2009). Spread spectrum image watermarking with digital deisign. IEEE International Advance Computing Conference 2009, Patiala, India.
Asghari, V. R., & Ardebilipour, M. (2004). Spread spectrum code estimation by genetic algorithm. International Journal of signal processing, 1(4).
Yen, K., & Hanzo, L. (2001). Genetic algorithm assisted joint multiuser symbol detection and fading channel estimation for synchronous CDMA systems. IEEE Transaction on Selected Areas in Communication, 19(6).
Asghari, V. R., & Ardebilipour, M. (2005). Spread spectrum code estimation by particle swarm algorithm. International Journal of Signal Processing, 2(4), 268–272.
Hua, K., Jang, W. M., & Nguyen, L. (2009). Cooperative self encoded spread spectrum in fading channels. International Journal of Communication, Network and system, 2, 91–96.
Maity, S., Maity, S. P., & Sil, J. (2009). Spread spectrum watermark embedder optimization using genetic algorithms, advances in pattern recognition 2009. Kolkata, India.
Sedghi, S., Mashhadi, H. R., & Khademi, M. (2006). Detecting hidden information from a spread spectrum watermarked signal by genetic algorithm 2006 IEEE congress on evolutionary computation Sheraton Vancouver Wall Centre Hotel. Vancouver, BC, Canada.
Gao, Q., Li, R., Wang, H., Dang, H., & Liu, L. (2004). Spread spectrum digital watermarking algorithm using gold codes. Journal of Xi’an Jiaotong University, 28(2).
Marvel, L. M., Retter, C. T., & Boncelet, C. G. J. (1998). Hiding information in images 1998 international conference on image processing, Chicago, USA.
Ruanaidh, J. J. K. O., & Csurka, G. (1999). A Bayesian approach to spread spectrum watermark detection and secure copyright protection for digital image libraries. IEEE computer society conference on computer vison and pattern recognition, Fort Collins, USA.
Shi, Z., & Schlegel, C. (2001). Joint iterative decoding of serially concatenated error control coded CDMA. IEEE JSAC, 19(8), 1646–1653.
Vassaux, B., Bas, P., & Chassery, J. M. (2001). A new CDMA technique for digital image watermarking, enhancing capacity of insertion and robustness 2001 International Corrence on Image Processing. Thessaloniki, Greece.
Konorski, J. (2011). Wireless and mobile networking (Foreword). Telecommunication Systems, 48(3–4), 233–236.
Dixon, R. C. (1984). Spread spectrum system. New York, NY: Wiley.
Sarwate, D. V., & Pursley, M. B. (1980). Crosscorrelation properties of pseudorandom and related sequences. Proceedings of IEEE, 68, 593–619.
Duel-Hallen, A. (1995). Multi-user detection for CDMA systems. IEEE Personal Communications, 2(2), 46–58.
Verdu, S. (1998). Multiuser detection. Cambridge: Cambridge University Press.
Gray, S. D., Kocic, M., & Brady, D. (1995). Multi-user detection in mismatched multiple access channel. IEEE Transactions on Communications, 43(12), 3080–3099.
Holtzman, J. M. (1992). A simple, accurate method to calculate spread-spectrum multuple access error probabilities. IEEE Transactions on Communications, 40(4).
Zhou, L., Wang, X., Tu, W., Mutean, G., & Geller, B. (2010). Distributed scheduling scheme for video streaming over multi-channel multi-radio multi-hop wireless networks. IEEE Journal on Selected Areas in Communications, 28(3), 409–419.
Zhou, L., Chao, H.-C., & Vasilakos, A. (2011). Joint forensics-scheduling strategy for delay-sensitive multimedia applications over heterogeneous networks. IEEE Journal on Selected Areas in Communications, 29(7), 1358–1367.
Zhou, L., & Chen, H.-H. (2011). On multimedia scheduling with constrained control channels. IEEE Transactions on Multimedia, 13(5), 1040–1051.
Acknowledgments
This research was supported in part by DUE S-STEM Grant-1154490 from the US Natural Science Foundation and seed grant in Dept. of Electrical and Computer Engineering at Lawrence Technological University
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Hua, K., Wang, W. High security self-encoded spread spectrum watermarking using genetic algorithms. Telecommun Syst 60, 143–148 (2015). https://doi.org/10.1007/s11235-014-9928-x
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11235-014-9928-x