Abstract
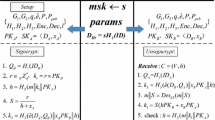
Secure communication is an important task for wireless sensor networks (WSNs). Signcryption is a good choice to guarantee the security of resource-constrained WSNs since it simultaneously achieves confidentiality, authentication, integrity and non-repudiation at a low cost. In this paper, we propose a heterogeneous signcryption scheme for secure communication from the WSNs to an Internet server. In our scheme, the WSNs belong to the certificateless cryptosystem (CLC) and the server belongs to the public key infrastructure (PKI). The CLC has neither key escrow problem nor public key certificates and is very suitable for the WSNs. The PKI is also suitable for the server since the PKI technique has been widely adopted in the Internet security. We prove that our scheme has the existential unforgeability against adaptive chosen message attack under q-strong Diffie–Hellman and modified inverse computational Diffie–Hellman problems and indistinguishability against adaptive chosen ciphertext attack under bilinear Diffie–Hellman inversion problem in the random oracle model. As compared with the existing three certificateless signcryption schemes (i.e., YL, BF and WC), our scheme respectively costs a 28.4, 58.3, and 68.2 % less in computational time and a 26.9, 56.6, and 67.3 % saving in energy consumption (the length of transmitted message is 100 bits).




Similar content being viewed by others
References
Li, F., Zhong, D., & Takagi, T. (2012). Practical identity-based signature for wireless sensor networks. IEEE Wireless Communications Letters, 1(6), 637–640.
Wang, C., Jiang, C., Liu, Y., Li, X. Y., & Tang, S. (2014). Aggregation capacity of wireless sensor networks: Extended network case. IEEE Transactions on Computers, 63(6), 1351–1364.
Zheng, Y. (1997). Digital signcryption or how to achieve cost (signature & encryption) ≪ cost (signature) + cost(encryption). In Advances in cryptology-CRYPTO’97, LNCS 1294 (pp. 165–179). Springer.
Kim, I. T., & Hwang, S. O. (2011). An efficient identity-based broadcast signcryption scheme for wireless sensor networks. In 6th International symposium on wireless and pervasive computing-ISWPC 2011 (pp. 1–6). Hong Kong.
Babamir, F. S., & Eslami, Z. (2012). Data security in unattended wireless sensor networks through aggregate signcryption. KSII Transactions on Internet and Information Systems, 6(11), 2940–2955.
Babamir, F. S., & Norouzi, A. (2014). Achieving key privacy and invisibility for unattendedwireless sensor networks in healthcare. The Computer Journal, 57(4), 624–635.
Li, F., & Xiong, P. (2013). Practical secure communication for integrating wireless sensor networks into the Internet of things. IEEE Sensors Journal, 13(10), 3677–3684.
Senthil kumaran, U., & Ilango, P. (2015). Secure authentication and integrity techniques for randomized secured routing in WSN. Wireless Networks, 21(2), 443–451.
Boneh, D., & Franklin, M. (2003). Identity-based encryption from the weil pairing. SIAM Journal on Computing, 32(3), 586–615.
Yin, A., & Liang, H. (2015). Certificateless hybrid signcryption scheme for secure communication ofwireless sensor networks. Wireless Personal Communications, 80(3), 1049–1062.
Al-Riyami, S.S., & Paterson, K.G. (2003). Certificateless public key cryptography. In Advances in cryptology-ASIACRYPT 2003, LNCS 2894 (pp. 452–474). Springer.
An, J. H., Dodis, Y., & Rabin, T. (2002). On the security of joint signature and encryption. In Advances in cryptology-EUROCRYPT 2002, LNCS 2332 (pp. 83–107). Springer.
Malone-Lee, J., & Mao, W. (2003). Two birds one stone: Signcryption using RSA. In Topics in cryptology-CT-RSA 2003, LNCS 2612 (pp. 211–225). Springer.
Boyen, X. (2003). Multipurpose identity-based signcryption: A swiss army knife for identity-based cryptography. In Advances in cryptology-CRYPTO 2003, LNCS 2729 (pp. 383–399). Springer.
Chen, L., & Malone-Lee, J. (2005). Improved identity-based signcryption. In Public key cryptography-PKC 2005, LNCS 3386 (pp. 362–379). Springer.
Barreto, P. S. L. M., Libert, B., McCullagh, N., & Quisquater, J. J. (2005). Efficient and provably-secure identity-based signatures and signcryption from bilinear maps. In Advances in cryptology-ASIACRYPT 2005, LNCS 3788 (pp. 515–532). Springer.
Jo, H. J., Paik, J. H., & Lee, D. H. (2014). Efficient privacy-preserving authentication in wireless mobile networks. IEEE Transactions on Mobile Computing, 13(7), 1469–1481.
Barbosa, M., & Farshim, P. (2008). Certificateless signcryption. In ACM symposium on information, computer and communications security-ASIACCS 2008 (pp. 369–372). Tokyo, Japan.
Wu, C., & Chen, Z. (2008). A new efficient certificateless signcryption scheme. In International symposium on information science and engineering-ISISE-2008 (pp. 661–664). Shanghai, China.
Sun, Y., & Li, H. (2010). efficient signcryption between TPKC and IDPKC and its multi-receiver construction. Science China Information Sciences, 53(3), 557–566.
Huang, Q., Wong, D. S., & Yang, G. (2011). Heterogeneous signcryption with key privacy. The Computer Journal, 54(4), 525–536.
Li, F., Zhang, H., & Takagi, T. (2013). Efficient signcryption for heterogeneous systems. IEEE Systems Journal, 7(3), 420–429.
Li, F., Zheng, Z., & Jin, C. (2016). Secure and efficient data transmission in the Internet of Things. Telecommunication Systems, 62(1), 111–122.
Roman, R., & Lopez, J. (2009). Integrating wireless sensor networks and the Internet: A security analysis. Internet Research, 19(2), 246–259.
Dutta, R., Barua, R., & Sarkar, P. (2004). Pairing-based cryptographic protocols : A survey. Cryptology ePrint Archive, Report 2004/064.
Choi, K. Y., Park, J. H., Hwang, J. Y., & Lee, D. H. (2007). Efficient certificateless signature schemes . In Applied cryptography and network security-ACNS 2007, LNCS 4521 (pp. 443–458). Springer.
Daemen, J., & Rijmen, V. (2002). The design of Rijndael: AES-the advanced encryption standard. Berlin: Springer.
Pointcheval, D., & Stern, J. (2000). Security arguments for digital signatures and blind signatures. Journal of Cryptology, 13(3), 361–396.
Boneh, D., & Boyen, X. (2004). Short signatures without random oracles. In Advances in cryptology-EUROCRYPT 2004, LNCS 3027 (pp. 56–73). Springer.
Cha, J. C., & Cheon, J. H. (2003). An identity-based signature from gap Diffie–Hellman groups. In Public key cryptography-PKC 2003, LNCS 2567 (pp. 18–30). Springer.
Shim, K. A., Lee, Y. R., & Park, C. M. (2013). EIBAS: An efficient identity-based broadcast authentication scheme in wireless sensor networks. Ad Hoc Networks, 11(1), 182–189.
Gura, N., Patel, A., Wander, A., Eberle, H., & Shantz, S. C. (2004). Comparing elliptic curve cryptography and RSA on 8-bit CPUs. In Cryptographic hardware and embedded systems-CHES 2004, LNCS 3156 (pp. 119–132). Springer.
Cao, X., Kou, W., Dang, L., & Zhao, B. (2008). IMBAS: Identity-based multi-user broadcast authentication in wireless sensor networks. Computer Communications, 31(4), 659–667.
Shim, K. A. (2014). \({{\rm S}}^{{\rm 2DRP}}\): Secure implementations of distributed reprogramming protocol for wireless sensor networks. Ad Hoc Networks, 19, 1–8.
Ma, C., Xue, K., & Hong, P. (2014). Distributed access control with adaptive privacy preserving property for wireless sensor networks. Security and Communication Networks, 7(4), 759–773.
Acknowledgments
This work is supported by the National Natural Science Foundation of China (Grant Nos. 61073176, 61272525, 61302161 and 61462048) and the Fundamental Research Funds for the Central Universities (Grant No. ZYGX2013J069).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Li, F., Han, Y. & Jin, C. Practical Signcryption for Secure Communication of Wireless Sensor Networks. Wireless Pers Commun 89, 1391–1412 (2016). https://doi.org/10.1007/s11277-016-3327-4
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11277-016-3327-4