Abstract
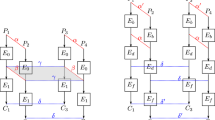
Lightweight block cipher is usually used in smart environment to protect confidentiality as well as to authentication. TWINE is a lightweight block cipher proposed by Japan scholar in SAC 2012 suits for kinds of platform from software to hardware. The cipher algorithm iterates a generalized Feistel structure with an improved block shuffle each sub-block includes an SP type round function. It with 64-bit block size, supports 80/128-bit key size and has 36 rounds iteration. This paper further investigates the security of TWINE, presents a new related-key impossible differential attack on reduced-round TWINE with 80-bit key (i.e. TWINE-80). By choosing the relations of keys carefully and exploring an equivalent structure of TWINE based on analysis of the encryption process, we show a 17-round related-key differential and then construct a 15-round related-key impossible differential trial. By using this trail, a 24-round related-key impossible differential attack on TWINE-80 is conducted. The result shows that the known impossible differential attack on TWINE-80 can be improved by one round.




Similar content being viewed by others
References
Barbera R, Giorgio E, Hwang S, Ricciardi G (2012) Gustav: CPU accounting for small-sized grid infrastructures. Int J Grid Util Comput 3(2/3):89–96
Barenghi A, Pelosi G, Terraneo F (2013) Secure and efficient design of software block cipher implementations on microcontrollers. Int J Grid Util Comput 4(2/3):110–118
Beaulieu R, Shors D, Smith J, Clark ST, Weeks B, Wingers L (2015) SIMON and SPECK: block ciphers for the internet of things. Cryptology ePrint Archive. http://eprint.iacr.org/2015/585. Accessed 9 Jul 2015
Biham E (1991) New types of cryptanalytic attacks using related keys. J Cryptol 4(1):3–72
Biham E, Biryukov A, Shamir A (1999) Cryptanalysis of Skipjack reduced to 31 rounds using impossible differentials. In: Proceedings of EUROCRYPT, Springer, vol 1592, pp 12–23
Biryukov A, Derbez P, Perrin L (2015) Differential analysis and meet-in-the-middle attack against round-reduced TWINE. In: Proceedings of FSE, Springer, vol 9054, pp 3–27
Bogdanov A, Knudsen L (2007) PRESENT: an ultra-lightweight block cipher. In: Proceedings of CHES, Springer, vol 4727, pp 450–466
Borghoff J, Canteaut A, Guneysu T, Kavun E, Knezevic M, Knudsen L, Leander G, Nikov V, Paar C, Rechberger C, Rombouts P, Thomsen S, Yalcin T (2012) Prince-a low-latency block cipher for pervasive computing applications. In: Proceedings of ASIACRYPT, Springer, vol 7658, pp 208–225
Boztas O, Karakoc F, Coban M (2013) Multidimensional meet-in-the-middle attacks on reduced-round TWINE-128. In: Proceedings of LightSec, Springer, vol 8162, pp 55–67
Canright D (2005) A very compact S-Box for AES. In: Proceedings of CHES, Springer, vol 3659, pp 441–455
Carabas M, Carabas C, Gheorghe L, Deaconescu R, Tapus N (2016) Monitoring and auditing mobile operating system. Int J Space Based Situat Comput 6(1):54–63
Chen L, Qi X, Liu L, Zheng G (2017) A security routing protocol based on convergence degree and trust. Int J Grid Util Comput 8(1):38–45
Chen P, Liao F, Wei H (2014) Related-key impossible differential attack on a lightweight block cipher MIBS. J Commun 35:190–193
Coban M, Karakoc F, Boztas O (2012) Biclique Cryptanalysis of TWINE. In: Proceedings of CANS, Springer, vol 7712, pp 43–55
Gong Z, Nikova S, Law Y (2011) KLEIN: a new family of light weight block ciphers. In: Proceedings of RFID security and privacy, Springer, vol 7055, pp 1–18
Guo J, Peyrin T, Poschmann A, Robshaw M (2011) The LED block cipher. In: Proceedings of CHES, Springer, vol 6917, pp 326–341
Hamida E, Javed M, Znaidi W (2017) Adaptive security provisioning for vehicular safety applications. Int J Space Based Situat Comput. https://doi.org/10.1504/IJSSC.2017.084120
Jaballah W, Mosbah M, Youssef H, Zemmari A (2015) Lightweight secure group communications for resource constrained devices. Int J Space Based Situat Comput 5(4):187–200
Knudsen L (1998) DEAL: a 128-bit block cipher. Technical report, Department of Informatics, University of Bergen, Norway
Kong H, Wang W, Zhang G (2015) Automatic search algorithm of meet in the middle attack on TWINE-128. J Cryptol Res 2(6):559–569
Lee D, Kim D, Kwon D, Kim H (2014) Efficient hardware implementation of the lightweight block encryption algorithm LEA. Sensors 14:975–994
Martins D, Guyennet H (2011) Security in wireless sensor networks: a survey of attacks and countermeasures. Int J Space Based Situat Comput 1(2/3):151–162
Mohamed T, Youssef A (2015) Generalized MitM attacks on full TWINE. Inf Process Lett 116(2):128–135
Moradi A, Poschmann A, Ling S, Paar C, Wang H (2011) Pushing the limits: a very compact and a threshold implementation of AES. In: Proceedings of EUROCRYPT, Springer, vol 6632, pp 69–88
Shibutani K, Isobe T, Hiwatari H, Mitsuda A, Akishita T, Shirai T (2011) Piccolo: an Ultra-lightweight block cipher. In: Proceedings of CHES, Springer, vol 6917, pp 342–357
Suzaki T, Minematsu K, Morioka S, Kobayashi E (2013) TWINE: a lightweight block cipher for multiple platforms. In: Proceedings of SAC, Springer, vol 7707, pp 339–354
Wang X, Ma J, Yang X (2015) A new proxy re-encryption scheme for protecting critical information systems. J Ambient Intell Hum Comput 6(6):699–711
Wang X, Ma J, Xhafa F, Zhang M, Luo X (2017) Cost-effective secure e-health cloud system using identity based cryptographic techniques. Future Gener Comput Syst 67:242–254
Wang Y, Wu W (2014) Improved multidimensional zero-correlation linear cryptanalysis and applications to LBlock and TWINE. In: Proceedings of ACISP, Springer, vol 8544, pp 1–16
Wen L, Wang M, Zhao J (2014) Related-key impossible differential attack on reduced round LBlock. J Comput Sci Technol 29(1):165–176
Zheng X, Jia K (2014) Impossible differential attack on reduced-round TWINE. In: Proceedings of ICISC, Springer, vol 8565, pp 123–143
Acknowledgements
The work in this paper is supported by Foundation of Science and Technology on Information Assurance Laboratory (no. KJ-15-010), China Postdoctoral Science Foundation (no. 2015M582912), and Basic Research Program of Engineering University of Chinese Armed Police Force (no. WJY201522).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Wei, Y., Xu, P. & Rong, Y. Related-key impossible differential cryptanalysis on lightweight cipher TWINE. J Ambient Intell Human Comput 10, 509–517 (2019). https://doi.org/10.1007/s12652-017-0675-1
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12652-017-0675-1