Abstract
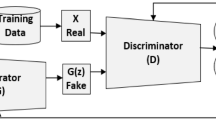
Artificial intelligence (AI) technology ruling people is still the scene in the science fiction film, but hackers using AI technology against existing security measures is an inescapable trend. Network intrusion detection systems (NIDS) based deep learning such as convolutional neural network (CNN) have reached a very high detection rate. But we propose DoS-WGAN, a common architecture that uses the Wasserstein generative adversarial networks (WGAN) with gradient penalty technology to evade network traffic Classifiers. To camouflage offensive denial of service (DoS) attack traffic as normal network traffic, DoS-WGAN automatically synthesizes attack traces that can defeat a existing NIDS/network security defense for DoS cases. Information entropy is used to measure the dispersing performance of generated DoS attack traffic. The generated DoS attack traffic is so similar to the normal traffic that detection algorithm cannot distinguish between them. When we input the generated DoS attack traffic to a NIDS based on CNN in our experiments, the detection rate drops to \(47.6\%\) from \(97.3\%\). To make the training more stable, we integrate the Standardized Euclidean distance and the information entropy to evaluate the training process. We believe that AI technology will play a particularly important role in the game of network attack and defense.




Similar content being viewed by others
References
Arjovsky M, Bottou L (2017) Towards principled methods for training generative adversarial networks. arXiv preprint arXiv:170104862
Arjovsky M, Chintala S, Bottou L (2017) Wasserstein GAN. arXiv preprint arXiv:170107875
Bi J, Zhang K, Cheng X (2009) Intrusion detection based on RBF neural network. In: International symposium on information engineering and electronic commerce, IEEC’09. IEEE, New York, pp 357–360
Biggio B, Corona I, Maiorca D, Nelson B, Šrndić N, Laskov P, Giacinto G, Roli F (2013) Evasion attacks against machine learning at test time. In: Joint European conference on machine learning and knowledge discovery in databases, vol 8190. Springer, Berlin, pp 387–402
Bode MA, Oluwadare SA, Alese BK, Thompson FB (2015) Risk analysis in cyber situation awareness using Bayesian approach. In: 2015 international conference on cyber situational awareness, data analytics and assessment (CyberSA). IEEE, New York, pp 1–12
Brain G (2015) Tensorflow. Open source software library. https://tensorflow.google.cn/. Accessed 24 Dec 2018
Canbay Y, Sagiroglu S (2016) A hybrid method for intrusion detection. In: 2015 IEEE 14th international conference on machine learning and applications (ICMLA). IEEE, New York, pp 156–161
Chauhan M, Pratap A, Sonika, Dixit A (2015) Designing a technique for detecting intrusion based on modified adaptive resonance theory network. In: 2015 international conference on green computing and internet of things (ICGCIoT). IEEE, New York, pp 448–451
Chordia AS, Gupta S (2016) An effective model for anomaly ids to improve the efficiency. In: 2015 international conference on green computing and internet of things (ICGCIoT). IEEE, New York, pp 190–194
Fu Y, Zhu Y, Yu H (2009) Study of neural network technologies in intrusion detection systems. In: 5th international conference on wireless communications, networking and mobile computing, WiCom’09. IEEE, New York, pp 4454–4457
Goodfellow IJ, Pouget-Abadie J, Mirza M, Xu B, Warde-Farley D, Ozair S, Courville A, Bengio Y (2014) Generative adversarial nets. In: International conference on neural information processing systems, pp 2672–2680
Gulrajani I, Ahmed F, Arjovsky M, Dumoulin V, Courville AC (2017) Improved training of Wasserstein GANs. In: Advances in neural information processing systems, pp 5767–5777
Haykin S (1994) Neural networks: a comprehensive foundation. Prentice Hall PTR, London
Hu W, Tan Y (2017) Generating adversarial malware examples for black-box attacks based on GAN. arXiv:1702.05983
Jiang J, Zhang C, Kamel M (2003) RBF-based real-time hierarchical intrusion detection systems. In: 2003 proceedings of the international joint conference on neural networks, vol 2(2), pp 1512–1516
Khosravi-Farmad M, Ramaki AA, Bafghi AG (2015) Risk-based intrusion response management in IDS using Bayesian decision networks. In: 2015 5th international conference on computer and knowledge engineering (ICCKE). IEEE, New York, pp 307–312
Kingma D, Ba J (2014) Adam: a method for stochastic optimization. Comput Sci
Kumar VD, Radhakrishnan S (2014) Intrusion detection in MANET using self organizing map (SOM). In: 2014 international conference on recent trends in information technology (ICRTIT). IEEE, New York, pp 1–8
Padmadas M, Krishnan N, Kanchana J, Karthikeyan M (2014) Layered approach for intrusion detection systems based genetic algorithm. In: 2013 IEEE international conference on computational intelligence and computing research (ICCIC). IEEE, New York, pp 1–4
Sahu S, Mehtre BM (2015) Network intrusion detection system using j48 decision tree. In: 2015 international conference on advances in computing, communications and informatics (ICACCI). IEEE, New York, pp 2023–2026
Salimans T, Goodfellow I, Zaremba W, Cheung V, Radford A, Chen X (2016) Improved techniques for training GANs. In: Advances in neural information processing systems, pp 2234–2242
Senthilnayaki B, Venkatalakshmi K, Kannan A (2015) Intrusion detection using optimal genetic feature selection and svm based classifier. In: 2015 3rd international conference on signal processing, communication and networking (ICSCN). IEEE, New York, pp 1–4
Stolfo S, Lee W (1999) Kddcup 1999 dataset. The data set used for the third international knowledge discovery and data mining tools competition. http://kdd.ics.uci.edu/databases/kddcup99/kddcup99.html. Accessed 29 Mar 2018
Teng L, Teng S, Tang F, Zhu H, Zhang W, Liu D, Liang L (2015) A collaborative and adaptive intrusion detection based on svms and decision trees. In: 2014 IEEE international conference on data mining workshop (ICDMW). IEEE, New York, pp 898–905
Villani C (2009) Optimal transport: old and new. In: Grundlehren der mathematischen Wissenschaften. Springer, Berlin
Vinayakumar R, Soman K, Poornachandran P (2017) Applying convolutional neural network for network intrusion detection. In: 2017 international conference on advances in computing, communications and informatics (ICACCI). IEEE, New York, pp 1222–1228
Wahengbam M, Marchang N (2012) Intrusion detection in MANET using fuzzy logic. In: 2012 3rd national conference on emerging trends and applications in computer science (NCETACS). IEEE, New York, pp 189–192
Xu W, Qi Y, Evans D (2016) Automatically evading classifiers: a case study on PDF malware classifiers. In: Proceedings of the 2016 network and distributed systems symposium. http://dx.doi.org/10.14722/ndss.2016.23115
Yang Z, Karahoca A, Yang N, Aydin N (2008) Network intrusion detection by using cellular neural network with Tabu search. In: ECSIS symposium on bio-inspired learning and intelligent systems for security, BLISS’08. IEEE, New York, pp 64–68
Zhang XY, Zeng HS, Jia L (2010) Research of intrusion detection system dataset-KDD CUP99. Comput Eng Des 31(22):4809–4805
Zhu JY, Park T, Isola P, Efros AA (2017) Unpaired image-to-image translation using cycle-consistent adversarial networks. arXiv preprint arXiv:170310593
Acknowledgements
We thank the anonymous reviewers of this work for their helpful feedback. This research is supported in part by a grant from the National Natural Science Foundation of China (no. 61672358). This research is also supported in part by a grant from Basic Research Program of Shenzhen, China under its Suppress Distributed Denial of Service Attacks in IoT Program (no. JCYJ20170302154032530). All opinions expressed in this paper are solely those of the authors.
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Yan, Q., Wang, M., Huang, W. et al. Automatically synthesizing DoS attack traces using generative adversarial networks. Int. J. Mach. Learn. & Cyber. 10, 3387–3396 (2019). https://doi.org/10.1007/s13042-019-00925-6
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s13042-019-00925-6