Abstract
A secret sharing scheme is a protocol by means of which a dealer distributes a secret s among a set of participants P in such a way that only qualified subsets of P can reconstruct the value of s whereas any other subset of P, non-qualified to know s, cannot determine anything about the value of the secret.
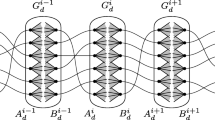
In this paper we provide a general technique to prove upper bounds on the information rate of secret sharing schemes. The information rate is the ratio between the size of the secret and the size of the largest share given to any participant. Most of the recent upper bounds on the information rate obtained in the literature can be seen as corollaries of our result. Moreover, we prove that for any integer d there exists a d-regular graph for which any secret sharing scheme has information rate upper bounded by 2/(d+1). This improves on van Dijk's result dik and matches the corresponding lower bound proved by Stinson in [22].
Similar content being viewed by others
References
Beimel A., Gal A., and Paterson M., Lower Bounds for Monotone Span Programs, Proc. 35th IEEE Symp. on Foundations of Computer Science, (1995), pp. 674–681.
Benaloh J.C. and Leichter J., Generalized Secret Sharing and Monotone Functions, Lecture Notes in Computer Science, Springer-Verlag, Berlin, Vol. 403, (1985), pp. 27–35.
Blakley G.R., Safeguarding Cryptographic Keys, AFIPS Conference Proceedings, Vol. 48, (1979), pp. 313–317.
Blundo C., De Santis A., Giorgio Gaggia A., and Vaccaro U., New Bounds on the Information Rate of Secret Sharing Schemes, IEEE Trans. Inform. Theory, Vol. 41, (1995), pp. 549–554.
Blundo C., De Santis A., Gargano L., and Vaccaro U., On the Information Rate of Secret Sharing Schemes, Theoretical Computer Science, Vol. 154, (1996), pp. 283–306. Preliminary version appeared in Lecture Notes in Computer Science, Springer-Verlag, Berlin, Vol. 740, (1993), pp. 149–169.
Blundo C., De Santis A., Stinson D.R., and Vaccaro U., Graph Decomposition and Secret Sharing Schemes, J. Cryptology, Vol. 8, (1995), pp. 39–64.
Blundo C., De Santis A., and Vaccaro U., Randomness in Distribution Protocols, Lecture Notes in Computer Science, Springer-Verlag, Berlin, Vol. 820, (1994), pp. 568–579. Also to appear in Information and Computation.
Blundo C., De Santis A., and Vaccaro U., On Secret Sharing Schemes, Preprint, (1995).
Brickell E.F. and Davenport D.M., On the Classification of Ideal Secret Sharing Schemes. J. Cryptology, Vol. 4, (1991), pp. 123–134.
Brickell E.F. and Stinson D.R., Some Improved Bounds on the Information Rate of Perfect Secret Sharing Schemes, J. Cryptology, Vol. 5 (1992), pp. 153–166.
Capocelli R.M., De Santis A., Gargano L., and Vaccaro U., On the Size of Shares for Secret Sharing Schemes, J. Cryptology, Vol. 6, (1993), pp. 157–168, 1993. Preliminary version appeared in Lecture Notes in Computer Science, Springer-Verlag, Berlin, Vol. 576, (1992), pp. 101–113.
Cover T.M. and Thomas J.A., Elements of Information Theory, John Wiley & Sons, (1991).
Csimarz L., The Size of a Share Must be Large, Lecture Notes in Computer Science, Springer-Verlag, Berlin, Vol. 950, (1995), pp. 13–22. Also to appear in Journal of Cryptology.
van Dijk M., On the Information Rate of Perfect Secret Sharing Schemes, Design, Codes, and Cryptography, Vol. 6, (1995), pp. 143–169.
Ito M., Saito A., and Nishizeki T., Secret Sharing Scheme Realizing General Access Structure, Proc. IEEE Globecom '87, (1987), pp. 99–102.
W.-A. Jackson, K. Martin, and G.J. Simmons, The Geometry of Shared Secret Schemes, Bulletin of ICA, vol. 1, 1991, pp. 71–88.
Karnin E.D., Greene J.W., and Helmann M.E., On Secret Sharing Systems, IEEE Trans. Inform. Theory, Vol. 29, (1983), pp. 35–41.
Martin K.M., New Secret Sharing Schemes from Old, J. Combin. Math. Combin. Comput., Vol. 14, (1993), pp. 65–77.
Shamir A., How to Share a Secret, Communication of the ACM, Vol. 22, (1979), pp. 612–613.
Simmons G.J., An Introduction to Shared Secret and/or Shared Control Schemes and Their Application, Contemporary Cryptology. The Science of Information Integrity, IEEE Press, New York, (1991), pp. 441–497.
Stinson D.R., An Explication of Secret Sharing Schemes, Designs, Codes and Cryptography, Vol. 2, (1992), pp. 357–390.
Stinson D.R., Decomposition Constructions for Secret Sharing Schemes, IEEE Trans. Inform. Theory, Vol. 40, (1994), pp. 118–125.
Stinson D.R., Cryptography: Theory and Practice. CRC Press, Inc., Boca Raton, (1995).
Author information
Authors and Affiliations
Rights and permissions
About this article
Cite this article
Blundo, C., Santis, A.D., Simone, R.D. et al. Tight Bounds on the Information Rate of Secret Sharing Schemes. Designs, Codes and Cryptography 11, 107–110 (1997). https://doi.org/10.1023/A:1008216403325
Issue Date:
DOI: https://doi.org/10.1023/A:1008216403325