Abstract
One of the methods for information security risk assessment is the substantiated choice and realization of countermeasures against threats. A situational fuzzy OWA model of a multicriteria decision making problem concerning the choice of countermeasures for reducing information security risks is proposed. The proposed model makes it possible to modify the associated weights of criteria based on the information entropy with respect to the aggregation situation. The advantage of the model is the continuous improvement of the weights of the criteria and the aggregation of experts’ opinions depending on the parameter characterizing the aggregation situation.
Similar content being viewed by others
References
Petrenko, S.A. and Simonov, S.V., Upravlenie informatsionnymi riskami. Ekonomicheski opravdannaya bezopasnost’ (Information Risk Control. Economically Justified Safety), Moscow: DMK Press, 2004.
ISO/IEC 27005:2007, Information Technology—Security Techniques—Information Security Risk Management, November 2007.
Stoneburner, G., Goguen, A., and Feringa, A., NIST Special Publication 800-30: Risk Management Guide for Information Technology Systems, Recommendations of the National Institute of Standards and Technology, 2002.
Barber, B. and Davey, J., The Use of the CCTA Risk Analysis and Management Methodology CRAMM, Proc. MEDINFO92, North Holland, 1992. pp. 1589–1593.
Alberts, C.J., Behrens, S.G., et al., Operationally Critical Threat, Asset and Vulnerability Evaluation (OCTAVE), Framework. Pittsburg, Carnegie Mellon, 1999, pp. 1–69.
Buyens, K., De Win, B., and Joosen, W., Empirical and Statistical Analysis of Risk Analysis-Driven Techniques for Threat Management, The 2nd Int. Conf. on Availability, Reliability and Security (ARES), 2007, pp. 1034–1041.
Loparev, S. and Shelupanov, A., Analysis of Instrumental Means of Risk Estimation of Information Leak in Computer Network of Enterprise. Voprosy Zashchity Informatsii, 2003, no. 4.
Yager, R.R., On Ordered Weighted Averaging Aggregation Operators in Multi-criteria Decision Making, IEEE Trans. Systems, Man Cybernet., 1988, vol. 18, no. 1, pp. 183–190.
Jiang, H. and Eastman, J.R., Application of Fuzzy Measures in Multi-criteria Evaluation in GIS, Int. J. Geography Information Systems, 2000, vol. 14, no. 2, pp. 173–184.
Merigó, J.M., The Fuzzy Probabilistic Weighted Averaging Operator and Its Application in Decision Making, Proc. 9th Int. Conf. on Intelligent Systems Design and Applications-ISDA, 2009, pp. 485–490.
Ramanathan, R. and Ganesh, L.S., A Multi-Objective Programming Approach to Energy Resource Allocation Problems, Int. J. Energy Research, 1990, vol. 17, no. 2, pp. 105–119.
Tesfamariam, S. and Sadiq, R., Probabilistic Risk Analysis Using Ordered Weighted Averaging (OWA) Operators, Stochastic Environmental Research and Risk Assessment, 2008, vol. 22, no. 1, pp. 1–15.
Mitchell, H.B. and Schaefer, P.A., Multiple Priorities in an Induced Ordered Weighted Averaging Operator, Int. J. Intelligent Systems, 2000, vol. 15, no. 4, pp. 317–327.
Xu, Z.S. and Da, Q.L., An Overview of Operators for Aggregating Information, Int. J. Intelligent Systems, 2003, vol. 18, no. 1, pp. 953–968.
Herrera, F., Herrera-Viedma, E., and Verdegay, J.I., Direct Approach Processes in Group Decision Making Using Linguistic OWA Operators, Fuzzy Sets and Systems, 1996, vol. 79, no. 2, pp. 175–190.
Saati, T.L., The Analytic Hierarchy Process, McGraw-Hill, 1980.
Chen-Tung Chen, Extensions of the TOPSIS for Group Decision-Making under Fuzzy Environment, Fuzzy Sets and Systems, 2000, vol. 114, no.1, pp. 1–9.
Knight, F.H., Risk, Uncertainty and Profit, Boston, MA: Hart, Schaffner & Marx, 1921.
Derevyanko, P.M., Comparison of Fuzzy and Imitation Approach to Simulation of Enterprise Activity in Uncertainty Conditions, in Sov. problemy ekonomiki i upravleniya narodnym khozyaistvom (Contempory Problems of Economics and National Ecinomy Management), St. Petersburg, 2005, pp. 289–292.
Nedosekin, A.O., Fuzzy Financial Management, Moscow: AFA Library, 2003.
Nedosekin, A.O., Nechetko-mnozhestvennyi analiz riska fondovykh investitsii (Fuzzy Multiple Analysis of Stock Investment Risk), St. Petersburg: Sezam, 2002.
Karimi, I. and Hüllermeier, E., Risk Assessment System of Natural Hazards: A New Approach Based on Fuzzy Probability, Fuzzy Sets and Systems, 2007, vol. 158, no. 9, pp. 987–999.
Dikmen, I., Birgonul, M.T., and Han, S., Using Fuzzy Risk Assessment to Rate Cost Overrun Risk in International Construction Projects, Int. J. Project Management, 2007, vol. 25, no. 5, pp. 494–505.
Alguliev, R.M. and Imamverdiev, Y.N., About One Method of Risk Measurement of Maintenance of Information Security of Corporative Networks Because of Fuzzy Sets, Proc. 4th Int. Conf. New Information Technol., Minsk, 2000, pp. 76–81.
Avdoshin, A.S., Estimation of Immunity of Information System by Fuzzy Logic Methods, Vestnik Samar. Gos. Tekh. Univ., 2005, vol. 32, pp. 191–193.
Balashov, P.A., Kislov, R.I., and Bezguzikov, V.P., Estimation of Information Safety Risks on the Base of Fuzzy Logic, Bezopasnost’ Kop’yuternykh System. Konfident, 2003, no. 5, pp. 56–59.
Dotsenko, S.M., Zaichikov, A.A., and Malysh, V.N., Increase of Objectivity of Source Data as Alternative to Fuzzy Logic Method at the Estimation of Information Safety, Zashchita Informatsii. Konfident, 2004, no. 5, pp. 83–85.
Fuller, R., On Obtaining OWA Operator Weights: a Short Survey of Recent Developments, Proc. 5th IEEE Int. Conf. Comput. Cybernetics, Gammarth, Tunisia, 2007, pp. 241–244.
Yager, R.R., Families of OWA Operators, Fuzzy Sets and Systems, 1993, vol. 59, no. 2, pp. 125–148.
Filev, D. and Yager, R.R., On the Issue of Obtaining OWA Operator Weights, Fuzzy Sets and Systems, 1998, vol. 94, no. 2, pp. 157–169.
Yager, R.R. and Filev, D., Induced Ordered Weighted Averaging Operators, IEEE Trans. on Systems, Man and Cybernetics, Part B, Cybernetics, 1999, vol. 29, no. 2, pp. 141–150.
O’Hagan, M., Aggregating Template or Rule Antecedents in Real-Time Expert Systems with Fuzzy Set Logic, Proc. 22nd Annu. IEEE Asilomar Conf., Signals, Syst., Comput., Pacific Grobe, CA, 1988, pp. 681–689.
Fullér, R. and Majlender, P., An Analytic Approach for Obtaining Maximal Entropy OWA Operator Weights, Fuzzy Sets and Systems, 2001, vol. 124, no. 1, pp. 53–57.
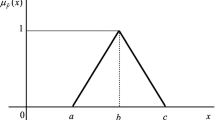
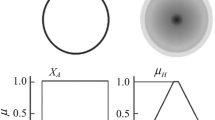
Zadeh, L.A., The Concept of Linguistic Variable and Its Application to Approximate Reasoning, Information Sciences, 1975, vol. 8, no. 3, pp. 199–249; vol. 8, no. 4, pp. 301–357; vol. 9, no. 1, pp. 43–80.
Bojadziev, G. and Bojadziev, M., Fuzzy Logic for Business, Finance, and Management (Advances in Fuzzy Systems: Applications and Theory, World Scientific Publ., 2nd ed., vol. 23.
Borisov, A.N., Krumberg, O.A., and Fedorov, I.P., Prinyatie reshenii na osnove nechetkikh modelei (Decision-Making on the Basis of Fuzzy Models), Riga: Zinatne, 1990.
Litvak, B.G., Ekspertnye otsenki i prinyatie reshenii (Expert Estimations and Decision Making), Moscow: Patent, 1996.
Ogletree, T.W., Practical Firewalls, Que, 2000.
Hsu, H.M. and Chen, C.T., Fuzzy Credibility Relation Method for Multiple Criteria Decision Making Problems, Inform. Sci., 1997, vol. 96, no. 1, pp. 79–91.
Author information
Authors and Affiliations
Corresponding author
Additional information
Original Russian Text © Ya.N. Imamverdiev, S.A. Derakshande, 2011, published in Avtomatika i Vychislitel’naya Tekhnika, 2011, No. 1, pp. 30–42.
About this article
Cite this article
Imamverdiev, Y.N., Derakshande, S.A. Fuzzy OWA model for information security risk management. Aut. Conrol Comp. Sci. 45, 20–28 (2011). https://doi.org/10.3103/S0146411611010056
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.3103/S0146411611010056